300-415 Cisco Implementing Cisco SD-WAN Solutions (300-415 ENSDWI) Free Practice Exam Questions (2026 Updated)
Prepare effectively for your Cisco 300-415 Implementing Cisco SD-WAN Solutions (300-415 ENSDWI) certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
Which OMP route is selected for equal OMP route preference values on WAN Edge routers?
Which two features does the application firewall provide? (Choose two.)
Which SD-WAN component allows an administrator to manage and store software images for SD-WAN network elements?
Which TCP Optimization feature is used by WAN Edge to prevent unnecessary retransmissions and large initial TCP window sizes to maximize throughput and achieve a better quality?
What are two benefits of installing Cisco SD-WAN controllers on cloud-hosted services? (Choose two.)
Refer to the exhibit.
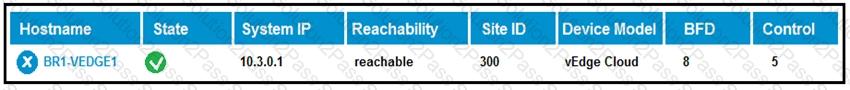
What does the BFD value of 8 represent?
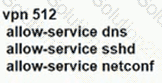
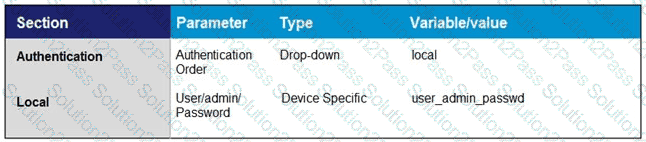
An engineer must automate certificate signing through Cisco. Which vManage configuration achieves this task?
A)
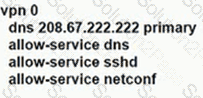
B)
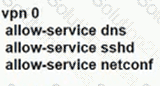
C)
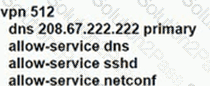
D)
How many network interface cards are needed to add in virtual machine settings when installing vSmart controller on VMware vSphere ESXi Hypervisor software?
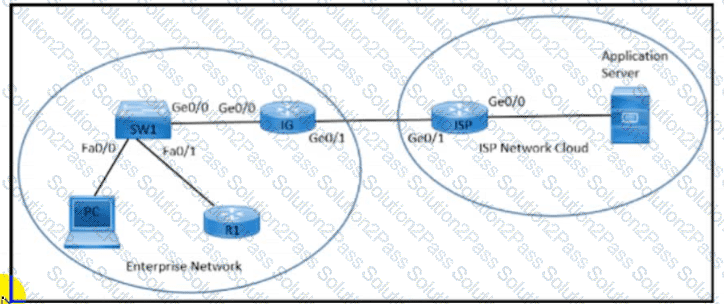
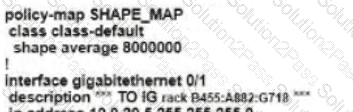
Refer to the exhibit. An enterprise network is connected with an ISP network on an 80 Mbps bandwidth link. The network operation team observes 100 Mbps traffic on the 1Gig-ISP link during peak hours Which configuration provides bandwidth control to avoid traffic congestion during peak hours?
A)
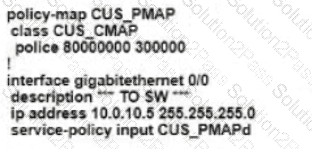
B)
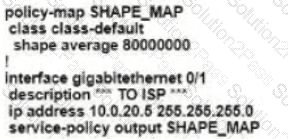
C)
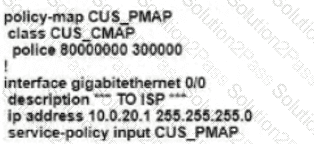
D)
Which scheduling method is configured by default for the eight queues in the cloud vEdge router1?
On which device is a service FW address configured to Insert firewall service at the hub?
Which API call retrieves a list of all devices in the network?
How must the application-aware enterprise firewall policies be applied within the same WAN Edge router?
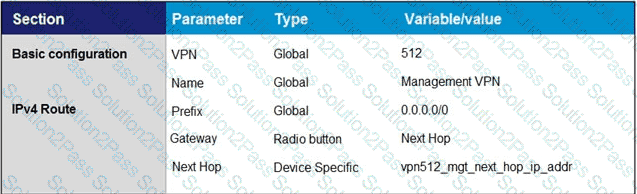
Which feature template configures OMP?
A)
B)
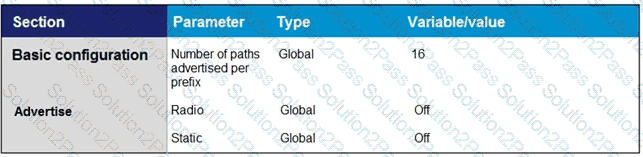
C)
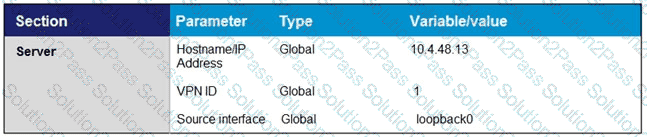
D)
Which component of the Cisco SD-WAN control plane architecture should be located in a public Internet address space and facilitates NAT-traversal?
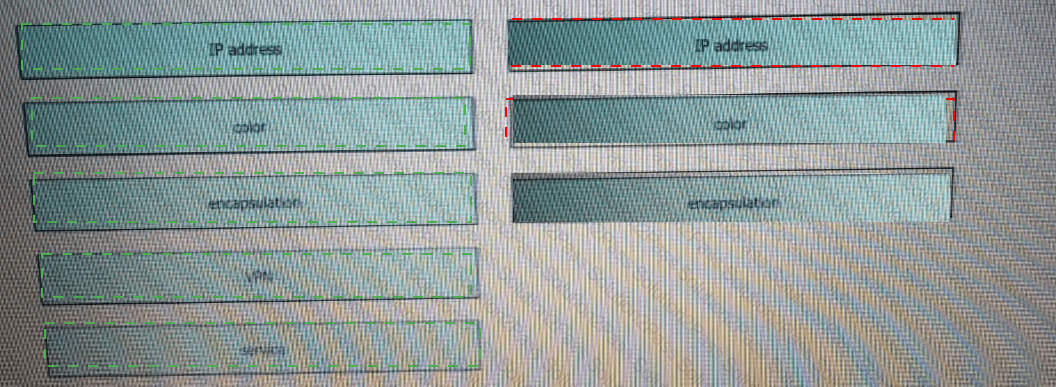
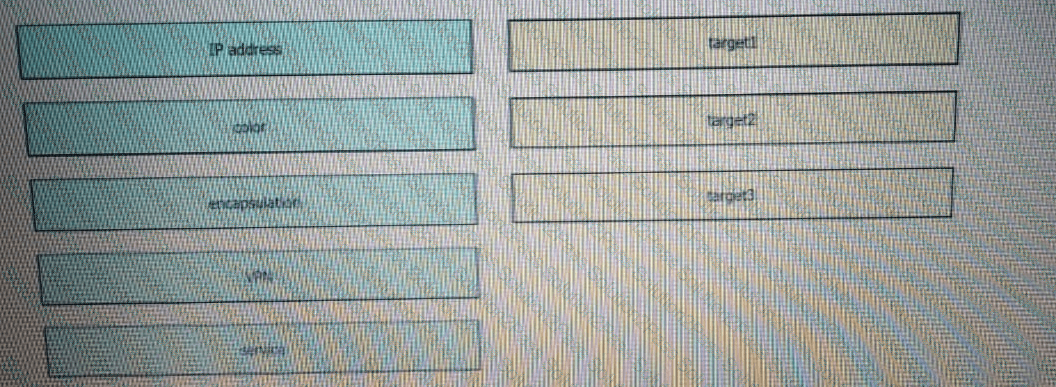
Drag and drop the attributes from the left that make each transport location unique onto the right. Not all options are used.
Which secure connection should be used to access the REST APIs through the Cisco vManage web server?
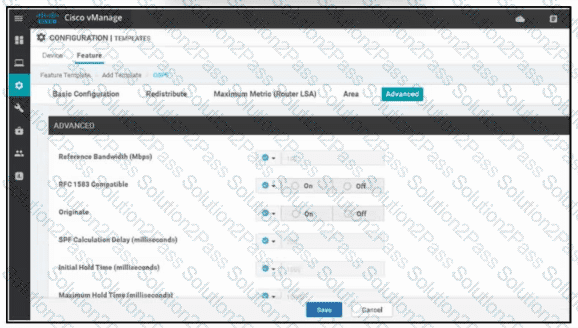
Refer to the exhibit. A network administrator is configuring OSPF advanced configuration parameters from a template using the vManager GUI for a branch WAN Edge router to calculate the cost of summary routes to an ASBR. Which action achieves this configuration?
Which controller is used for provisioning and configuration in a Cisco SD-WAN solution?
Which service VPN must be reachable from all WAN Edge devices and the controllers?