IDP CrowdStrike Certified Identity Specialist(CCIS) Exam Free Practice Exam Questions (2026 Updated)
Prepare effectively for your CrowdStrike IDP CrowdStrike Certified Identity Specialist(CCIS) Exam certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
How does the Falcon sensor for Windows contribute to the enforcement in Falcon Identity Protection?
How long does it typically take Falcon Identity to develop a baseline of a user?
To enforce conditional access policies with Identity Verification, an MFA connector can be configured for different authentication methods such as:
When creating an API key, which scope should be selected to retrieve Identity Protection detection and incident information?
How many days will an identity-based incident be suppressed if new events related to the same incident occur?
Which entity tab will show an administrator how to lower the account's risk score?
Which of the following isNOTan available Goal within the Domain Security Overview?
Which of the following users would most likely have aHIGHrisk score?
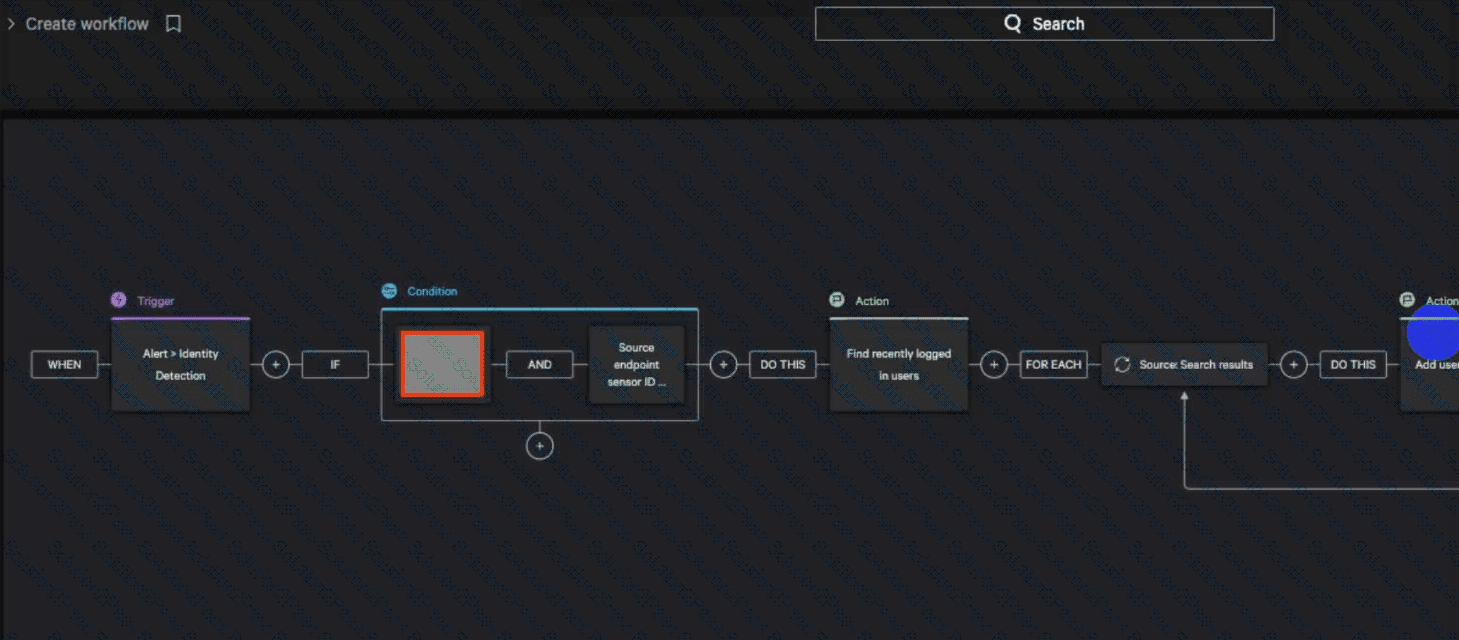
Considering the following example, what MITRE ATT&CK tactic would you use to complete the workflow?
What setting can be switched under the Domain Security Overview for each Active Directory domain and/or Azure tenant?
Which of the following are minimum requirements for showing the Falcon Identity Verification Dialog on the end user’s machine?
The events are excluded by default while Low, Medium, and High detections are visible.
The NIST SP 800-207 framework for Zero Trust Architecture defines validation and authentication standards for users in which network locations?
What trigger will cause a Falcon Fusion Workflow to activate from Falcon Identity Protection?
The CISO of your organization recently read a report about the increased usage of identity brokers and is interested in finding a solution for the company. Which of the following makes Falcon Identity a valid solution for the organization?
Which of the following would cause an identity-based incident type to change?
The Enforce section of Identity Protection is used to:
