FCSS_CDS_AR-7.6 Fortinet FCSS - Public Cloud Security 7.6 Architect Free Practice Exam Questions (2026 Updated)
Prepare effectively for your Fortinet FCSS_CDS_AR-7.6 FCSS - Public Cloud Security 7.6 Architect certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
Exhibit.
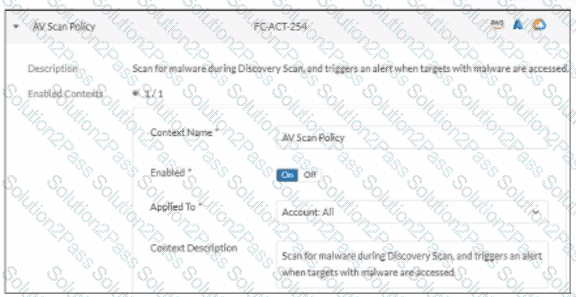
In which type of FortiCNP insights can an administrator examine the findings triggered by this policy?
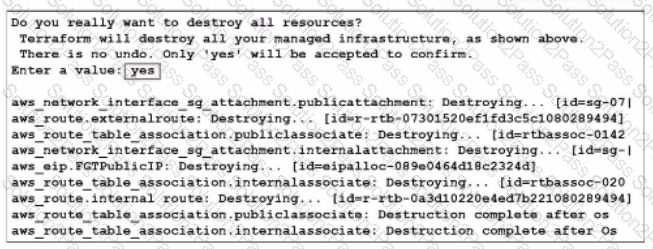
What would be the impact of confirming to delete all the resources in Terraform?
An organization is deploying FortiDevSec to enhance security for containerized applications, and they need to ensure containers are monitored for suspicious behavior at runtime.
Which FortiDevSec feature is best for detecting runtime threats?
Refer to the exhibit.
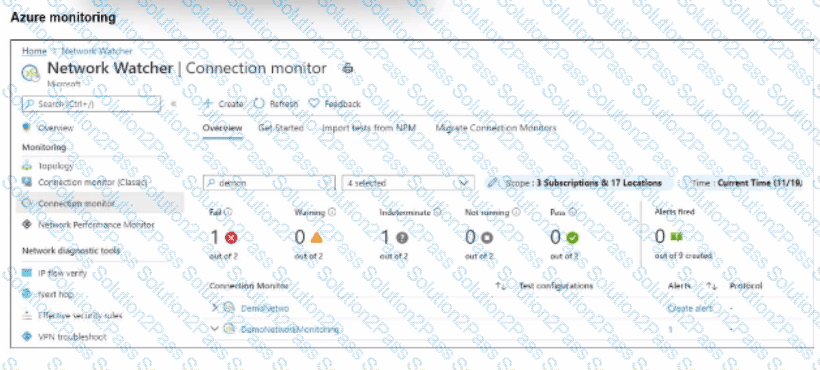
After analyzing the native monitoring tools available in Azure, an administrator decides to use the tool displayed in the exhibit.
Why would an administrator choose this tool?
You must add an Amazon Web Services (AWS) network access list (NACL) rule to allow SSH traffic to a subnet for temporary testing purposes. When you review the current inbound and outbound NACL rules, you notice that the rules with number 5 deny SSH and telnet traffic to the subnet.
What can you do to allow SSH traffic?
Which statement about Transit Gateway (TGW) in Amazon Web Services (AWS) is true?
You need a solution to safeguard public cloud-hosted web applications from the OWASP Top 10 vulnerabilities. The solution must support the same region in which your applications reside, with minimum traffic cost.
Which solution meets the requirements?
Refer to the exhibit.
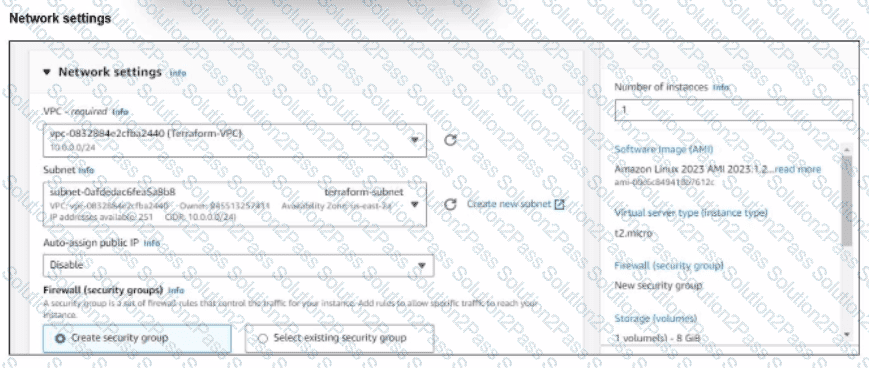
You have deployed a Linux EC2 instance in Amazon Web Services (AWS) with the settings shown on the exhibit.
What next step must the administrator take to access this instance from the internet?
An administrator is configuring a software-defined network (SDN) connector in FortiWeb to dynamically obtain information about existing objects in an Amazon Elastic Kubernetes Service (EKS) cluster.
Which AWS policy should the administrator attach to a user to achieve this goal?
In an SD-WAN TGW Connect topology, which three initial steps are mandatory when routing traffic from a spoke VPC to a security VPC through a Transit Gateway? (Choose three.)
You have deployed a FortiGate HA cluster in Azure using a gateway load balancer for traffic inspection. However, traffic is not being routed correctly through the firewalls.
What can be the cause of the issue?
