FCSS_NST_SE-7.6 Fortinet NSE 6 - Network Security 7.6 Support Engineer Free Practice Exam Questions (2026 Updated)
Prepare effectively for your Fortinet FCSS_NST_SE-7.6 Fortinet NSE 6 - Network Security 7.6 Support Engineer certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
Which two protocol states indicate that traffic is bidirectional? (Choose two.)
What is an accurate description of LDAP authentication using the regular bind type?
Which statement about parallel path processing is correct (PPP)?
Refer to the exhibit.

Partial output of the get vpn ipsec tunnel details command is shown. Based on the output, which two statements are correct? (Choose two.)
Refer to the exhibit.
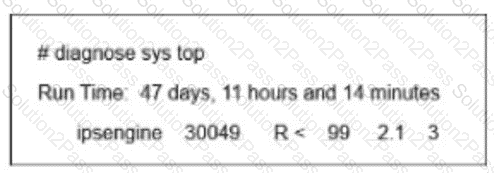
FortiGate is showing continuous high CPU usage During a maintenance window, the CLI command diagnose sys top displays the output shown in the exhibit. The CLI command diagnose twat application ipsmonitor 5 was run. but the CPU usage by daemon ipsengine did not drop Which immediate action can you take to reduce the CPU usage effectively?
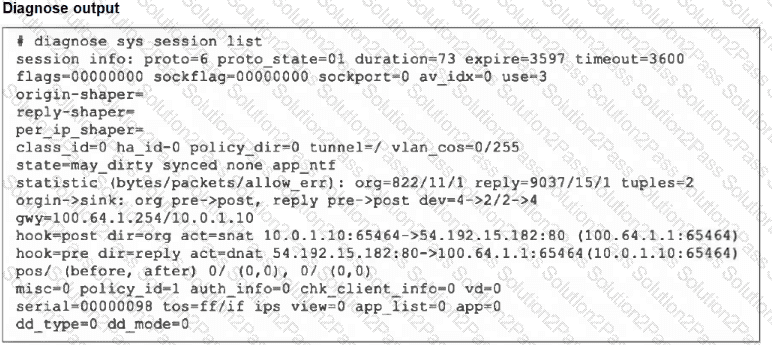
Refer to the exhibit, which shows the omitted output of a session table entry.
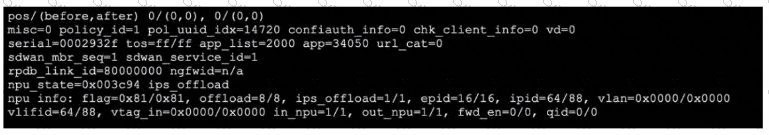
Which two statements are true? (Choose two.)
Exhibit.
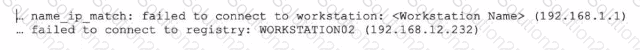
Refer to the exhibit, which shows two entries that were generated in the FSSO collector agent logs.
What three conclusions can you draw from these log entries? {Choose three.)
What are two functions of automation stitches? (Choose two.)
Refer to the exhibit.
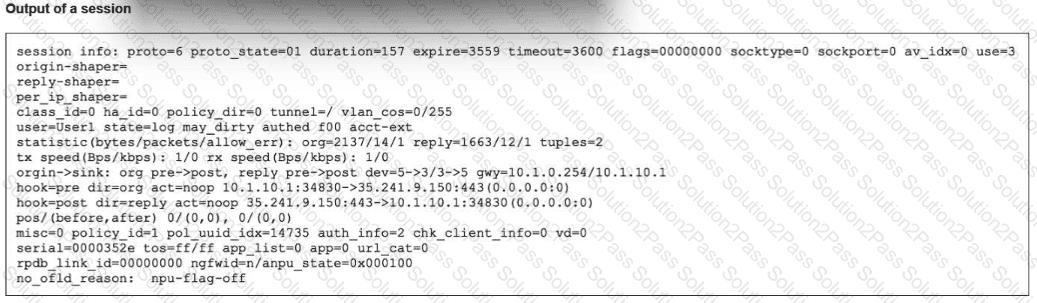
The exhibit shows the output of a session. Which two statements are correct? (Choose two.)
When FortiGate enters conserve mode because of memory pressure, which action can FortiGate perform to preserve memory?
Refer to the exhibit, which shows the output of diagnose sys session list.
If the HA ID for the primary device is 0, what happens if the primary fails and the secondary becomes the primary?
A FortiGate administrator is troubleshooting a VPN that is failing to establish.
As a first step, the administrator is attempting to sniff the traffic using the command:
# diagnose sniffer packet any ‘’udp port 500 or udp port 4500 or esp’’ 4
After several minutes there is still no output. What is the most Likely reason for this?
Refer to the exhibit, which shows the modified output of the routing kernel.
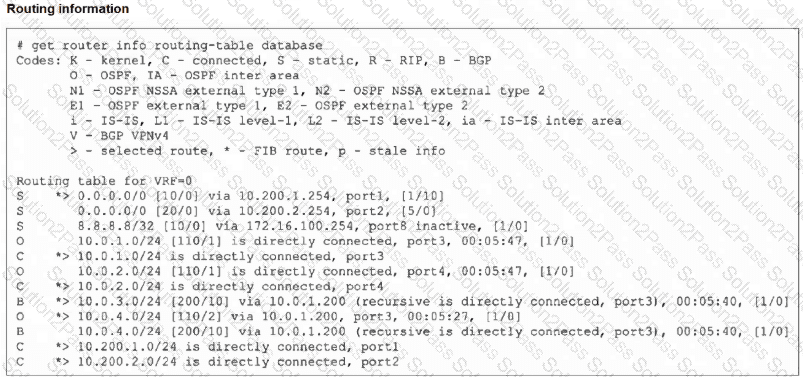
Which statement is true?
An administrator wants to capture encrypted phase 2 traffic between two FotiGate devices using the built-in sniffer.
If the administrator knows that there Is no NAT device located between both FortiGate devices, which command should the administrator run?
Refer to the exhibit, which a network topology and a partial routing table.
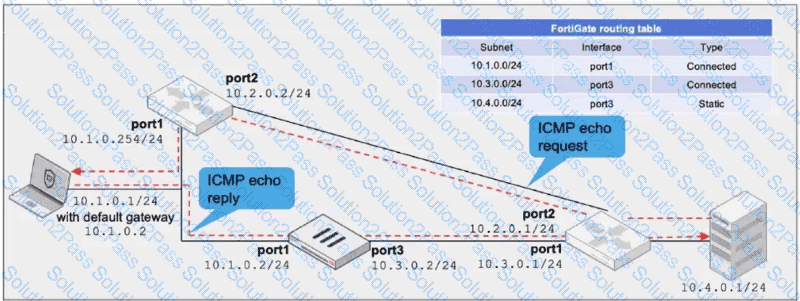
FortiGate has already been configured with a firewall policy that allows all ICMP traffic to flow from port1 to port3.
Which changes must the administrator perform to ensure the server at 10.4.0.1/24 receives the echo reply from the laptop at 10.1.0.1/24?
In the SAML negotiation process, which section does the Identity Provider (IdP) provide the SAML attributes utilized in the authentication process to the Service Provider (SP)?
During the SAML negotiation process, in which section does the Identity Provider (IdP) provide the SAML attributes used in the authentication process to the Service Provider (SP)?
Refer to the exhibit, which shows the output of the command get router info bgp neighbors 100.64.2.254 advertised-routes.
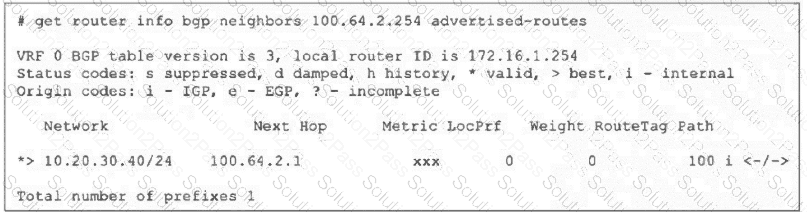
What can you conclude from the output?
Which authentication option can you not configure under config user radius on FortiOS?
Refer to the exhibit.
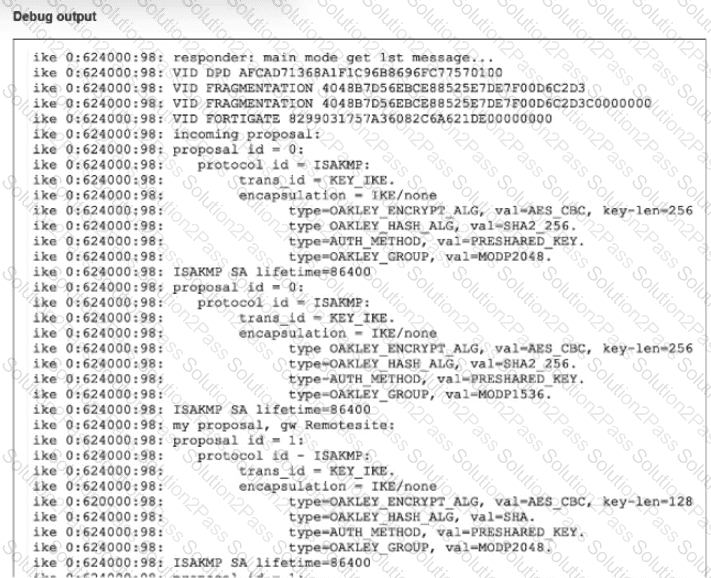
A partial output from an IKE real-time debug is shown
The administrator does not have access to (he remote gateway
Based on the debug output, which two conclusions can you draw? (Choose two.)
