CPEH-001 GAQM Certified Professional Ethical Hacker (CPEH) Free Practice Exam Questions (2026 Updated)
Prepare effectively for your GAQM CPEH-001 Certified Professional Ethical Hacker (CPEH) certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
The network in ABC company is using the network address 192.168.1.64 with mask 255.255.255.192. In the network the servers are in the addresses 192.168.1.122, 192.168.1.123 and 192.168.1.124.
An attacker is trying to find those servers but he cannot see them in his scanning. The command he is using is:
nmap 192.168.1.64/28.
Why he cannot see the servers?
The security concept of "separation of duties" is most similar to the operation of which type of security device?
Which of these options is the most secure procedure for storing backup tapes?
During a security audit of IT processes, an IS auditor found that there were no documented security procedures. What should the IS auditor do?
A large mobile telephony and data network operator has a data that houses network elements. These are essentially large computers running on Linux. The perimeter of the data center is secured with firewalls and IPS systems. What is the best security policy concerning this setup?
A company's security policy states that all Web browsers must automatically delete their HTTP browser cookies upon terminating. What sort of security breach is this policy attempting to mitigate?
The "black box testing" methodology enforces which kind of restriction?
Which of the following is designed to identify malicious attempts to penetrate systems?
Risks = Threats x Vulnerabilities is referred to as the:
While performing online banking using a Web browser, a user receives an email that contains a link to an interesting Web site. When the user clicks on the link, another Web browser session starts and displays a video of cats playing a piano. The next business day, the user receives what looks like an email from his bank, indicating that his bank account has been accessed from a foreign country. The email asks the user to call his bank and verify the authorization of a funds transfer that took place.
What Web browser-based security vulnerability was exploited to compromise the user?
Which of the following security operations is used for determining the attack surface of an organization?
Sid is a judge for a programming contest. Before the code reaches him it goes through a restricted OS and is tested there. If it passes, then it moves onto Sid. What is this middle step called?
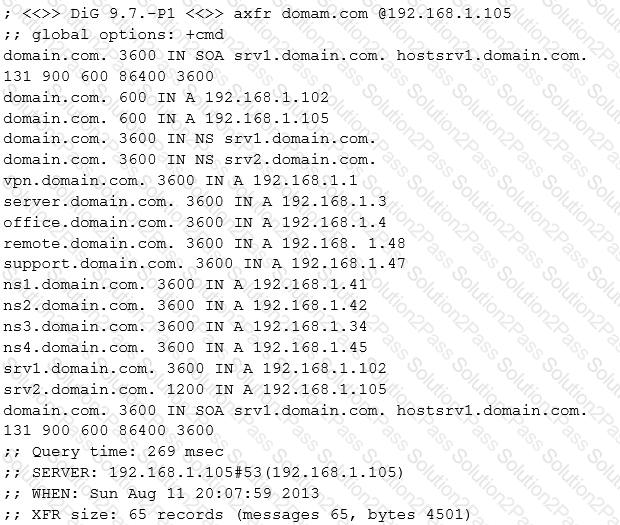
Look at the following output. What did the hacker accomplish?
You're doing an internal security audit and you want to find out what ports are open on all the servers. What is the best way to find out?
Bob learned that his username and password for a popular game has been compromised. He contacts the company and resets all the information. The company suggests he use two-factor authentication, which option below offers that?
A company's Web development team has become aware of a certain type of security vulnerability in their Web software. To mitigate the possibility of this vulnerability being exploited, the team wants to modify the software requirements to disallow users from entering HTML as input into their Web application.
What kind of Web application vulnerability likely exists in their software?
Craig received a report of all the computers on the network that showed all the missing patches and weak passwords. What type of software generated this report?
Which of the following tools can be used for passive OS fingerprinting?
Jimmy is standing outside a secure entrance to a facility. He is pretending to have a tense conversation on his cell phone as an authorized employee badges in. Jimmy, while still on the phone, grabs the door as it begins to close.
What just happened?
Email is transmitted across the Internet using the Simple Mail Transport Protocol. SMTP does not encrypt email, leaving the information in the message vulnerable to being read by an unauthorized person. SMTP can upgrade a connection between two mail servers to use TLS. Email transmitted by SMTP over TLS is encrypted. What is the name of the command used by SMTP to transmit email over TLS?
If an attacker uses the command SELECT*FROM user WHERE name = ‘x’ AND userid IS NULL; --‘; which type of SQL injection attack is the attacker performing?
You are looking for SQL injection vulnerability by sending a special character to web applications. Which of the following is the most useful for quick validation?
When conducting a penetration test, it is crucial to use all means to get all available information about the target network. One of the ways to do that is by sniffing the network. Which of the following cannot be performed by the passive network sniffing?
Which of the following Bluetooth hacking techniques does an attacker use to send messages to users without the recipient’s consent, similar to email spamming?
What is the least important information when you analyze a public IP address in a security alert?
Which of the following act requires employer’s standard national numbers to identify them on standard transactions?
In which of the following password protection technique, random strings of characters are added to the password before calculating their hashes?
Why should the security analyst disable/remove unnecessary ISAPI filters?
The collection of potentially actionable, overt, and publicly available information is known as
You are a security officer of a company. You had an alert from IDS that indicates that one PC on your Intranet is connected to a blacklisted IP address (C2 Server) on the Internet. The IP address was blacklisted just before the alert. You are staring an investigation to roughly analyze the severity of the situation. Which of the following is appropriate to analyze?
