H12-351_V1.0 Huawei HCIE-WLAN (Written) V1.0 Free Practice Exam Questions (2026 Updated)
Prepare effectively for your Huawei H12-351_V1.0 HCIE-WLAN (Written) V1.0 certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
In a multicast solution, there must be reachable unlcast routes between multicast sources and receivers.
iMaster NCE-Campuslnsight comprehensively analyzes WLAN client access, displays success rates and time consumption of association, --------, and DHCP. It also provides issue analysis and optimization suggestions. (Enter lowercase letters.)
Which of the following are typical 802. IX authentication modes? (Select All that apply)
Which of the following statements about the home agent are true? (Select All that Apply)
Which of the following components is not included In a typical RFID system?
Which of the following statements about attack defense is true?
On a campus network, which of the following problems may occur when you manually create a static VXLAN tunnel? (Select All that Apply)
Which of the fallowings is not an IPv6 address type?
In the early phase of a project, after the project requirements are clarified, the project owner should Checklist to describe the customer's requirements. (Capitalize the first letter of each word.)
In 802. IX authentication using port-based access control, once a user is authenticated successfully on a port, subsequent users on this port can access the network without authentication. When the authenticated user goes offline, all other users are denied access to the network.
iMaster NCE-Campuslnsight provides Intelligent radio calibration for high-load APs to increase the frequency bandwidth. This function applies to both 5 GHz and 2.4 GHz frequency bands.
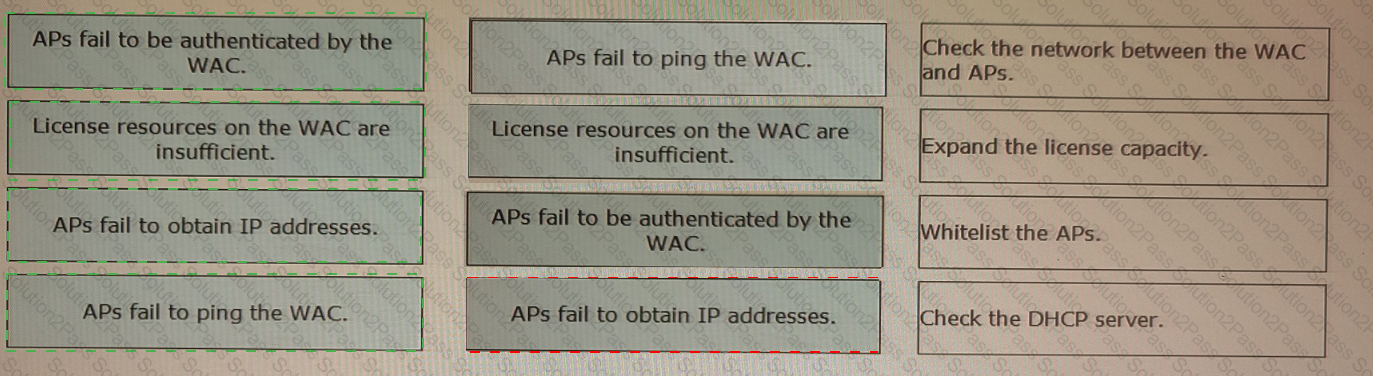
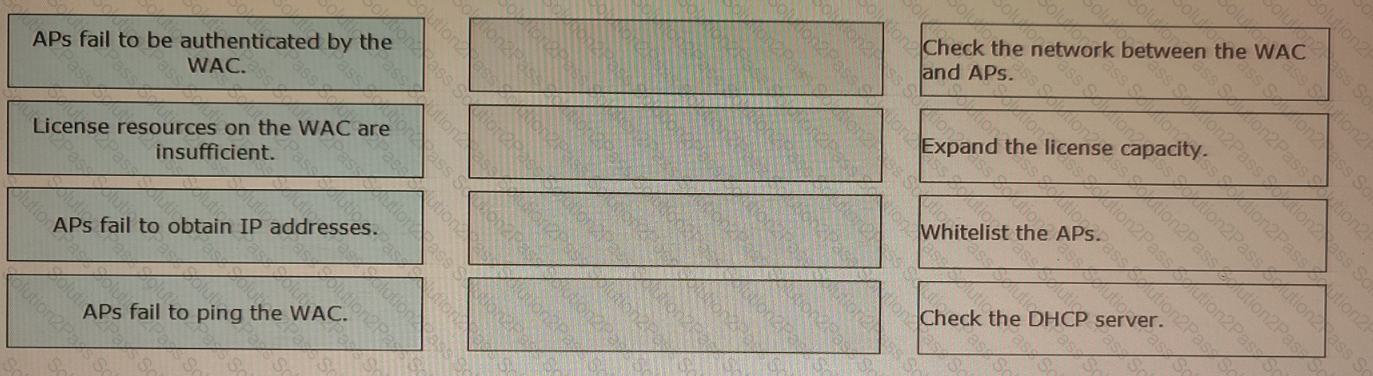
Drag the reasons for AP onboarding failures on the left to the corresponding troubleshooting operations on the right.
Which of the following statements about EAP relay and EAP termination are false? (Select All that apply)
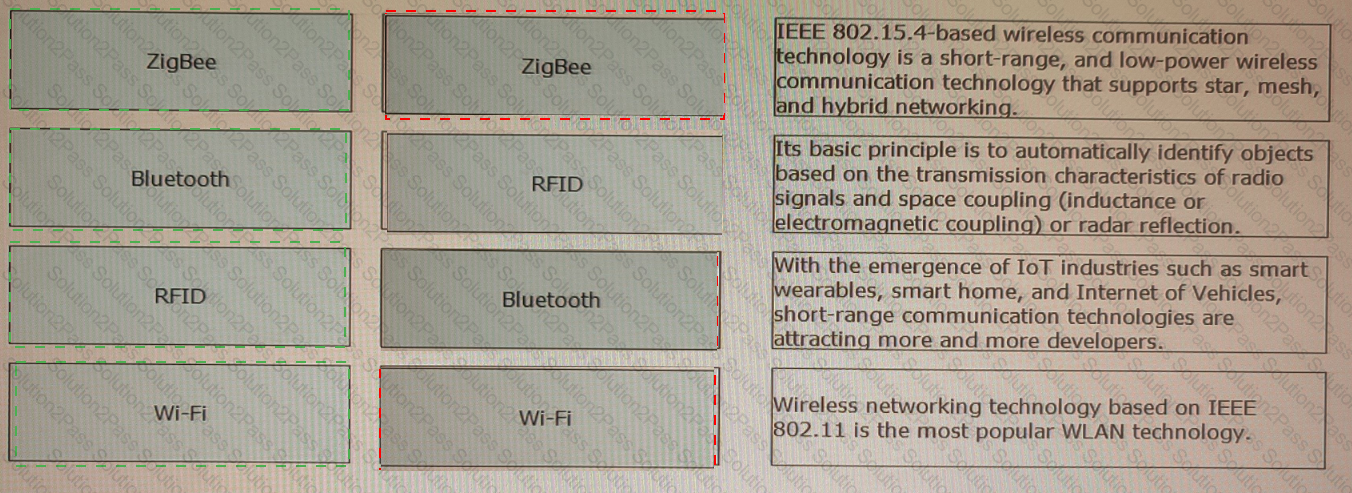
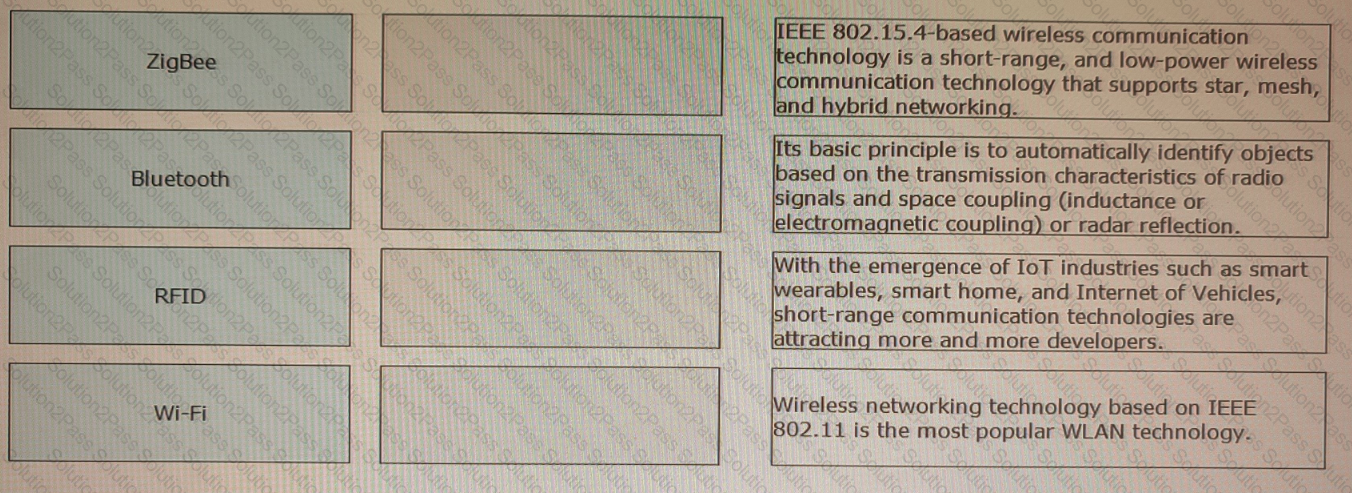
Drag the short-range wireless IoT technologies on the left to their corresponding descriptions on the right.
In Huawei's smart roaming solution, which of the following methods can be used by a WAC to discover and maintain neighboring AP entries of STAs? (Select All that Apply)
Which of the following tools are commonly used for WLAN network planning, acceptance, or health evaluation? (Select All that Apply)
Which of the following statements correctly arranges matching modes used by URL filtering in descending order of priority?
After multicast-to-unicast conversion is enabled on an AP's air interface, which of the followings is the destination MAC address of multicast packets sent over the air interface?