MCD-Level-2 MuleSoft Certified Developer - Level 2 (Mule 4) Free Practice Exam Questions (2026 Updated)
Prepare effectively for your MuleSoft MCD-Level-2 MuleSoft Certified Developer - Level 2 (Mule 4) certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
A company has been using CI/CD. Its developers use Maven to handle build and deployment activities.
What is the correct sequence of activities that takes place during the Maven build and deployment?
A system API that communicates to an underlying MySQL database is deploying to CloudHub. The DevOps team requires a readiness endpoint to monitor all system APIs.
Which strategy should be used to implement this endpoint?
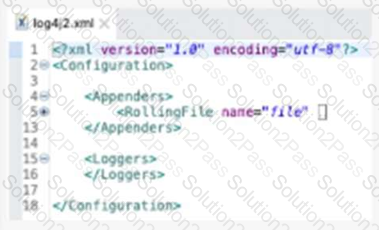
Refer to the exhibit.
What action must be performed to log all the errors raised by the VM Connector?
Which statement is true about using mutual TLS to secure an application?
A custom policy needs to be developed to intercept all cutbound HTTP requests made by Mule applications.
Which XML element must be used to intercept outbound HTTP requests?
An API has been developed and deployed to CloudHub Among the policies applied to this API is an allowlist of IP addresses. A developer wants to run a test in Anypoint Studio and does not want any policies applied because their workstation is not included in the allowlist.
What must the developer do in order to run this test locally without the policies applied?
Which type of cache invalidation does the Cache scope support without having to write any additional code?
The Center for Enablement team published a common application as a reusable module to the central Nexus repository.
How can the common application be included in all API implementations?
A Mule application contain two policies Policy A and Policy A has order1, and Policy B has order 2. Policy A Policy B, and a flow are defined by he configuration below.

When a HTTP request arrives at the Mule application’s endpoint, what will be the execution order?
A scatter-gather router is configured with four routes:Route A, B, C and D.
Route C false.
A Mule application for processing orders must log the order ID for every log message output.
What is a best practice to enrich every log message with the order ID?
An organization uses CloudHub to deploy all of its applications.
How can a common-global-handler flow be configured so that it can be reused across all of the organization’s deployed applications?
A developer is working on a project that requires encrypting all data before sending it to a backend application. To accomplish this, the developer will use PGP encryption in the Mule 4 Cryptography module.
What is required to encrypt the data before sending it to the backend application?
Refer to the exhibit.
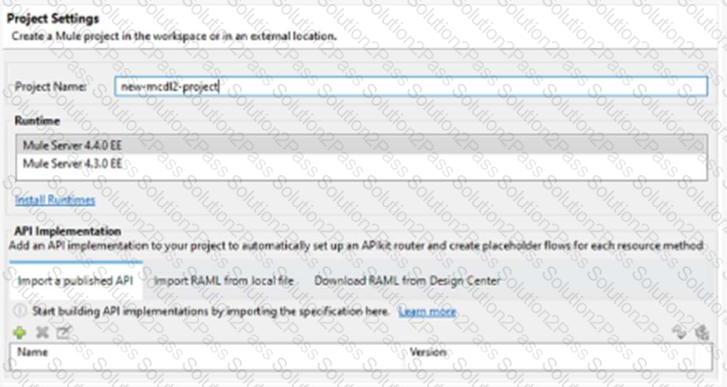
When creating a new project, which API implementation allows for selecting the correct API version and scaffolding the flows from the API specification?
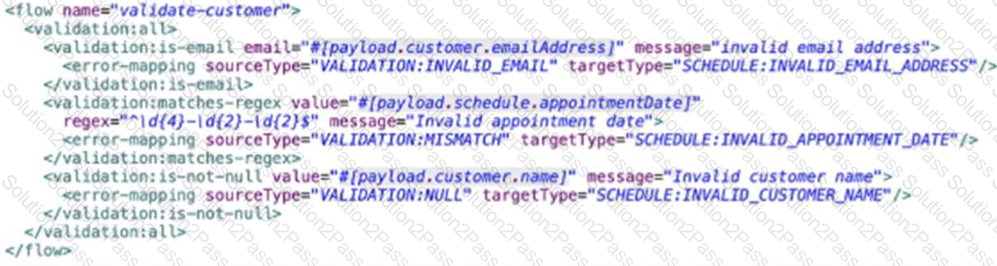
An API has been built to enable scheduling email provider. The front-end system does very little data entry validation, and problems have started to appear in the email that go to patients. A validate-customer’’ flow is added validate the data.
What is he expected behavior of the ‘validate-customer’’ flow?
Which properties are mandatory on the HTTP Connector configuration in order to use the OAuth 2.0 Authorization Code grant type for authentication?
A healthcare portal needs to validate the token that it sends to a Mule API. The developer plans to implement a custom policy using the HTTP Policy Transform Extension to match the token received in the header from the heathcare portal.
Which files does the developer need to create in order to package the custom policy?
A Mule application includes a subflow containing a Scatter.Gather scope. Within each log of the Scatter.Gatter. an HTTP connector calls a PUT endpoint to modify records in different upstream system. The subflow is called inside an Unit successful scope to retry if a transitory exception is raised.
A technical spike is being performed to increase reliability of the Mule application.
Which steps should be performed within the Mule flow above the ensure idempontent behavior?
