PPAN01 Proofpoint Certified Threat Protection Analyst Exam Free Practice Exam Questions (2026 Updated)
Prepare effectively for your Proofpoint PPAN01 Certified Threat Protection Analyst Exam certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
What is the primary function of the People Page in the Threat Protection Workbench and TAP Dashboard?
Which filter category in the TAP Dashboard helps identify threats targeting VIPs or specific geographies?
An analyst wants to use the Threats page in TAP Dashboard to review all messages related to a phishing campaign that contain an attachment. What is the correct method to filter these messages?
An analyst is reviewing the Notable Senders section in Proofpoint Supplier Threat Protection.
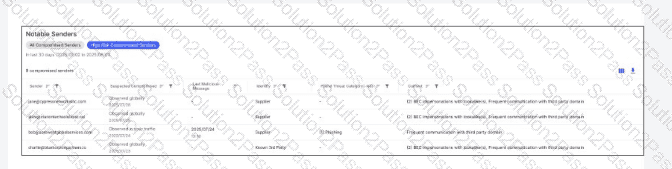
Based on the data shown in the exhibit, which vendor’s email activity should be investigated first?
For which two reasons should organizations customize their incident response plans based on NIST SP 800-61 or another incident response standard? (Select two.)
What is the purpose of Smart Search?
Refer to Exhibit:
X-Proofpoint-Banner-Trigger: inbound
MIM-version: 1.0
Content-Type: multipart/mixed; boundary="boundary-1698346305"
X-CLX-Shades: MLX
X-Proofpoint-Virus-Version: vendor=baseguard
engine=ICAP:2.0.272,Aquarius:18.0.987,Hydra:6.0.619,FMLib:17.11.176.26 definitions=2023-10-26_22,2023-10-26_01,2023-05-22_02
X-Proofpoint-Spam-Details: rule=spam policy=default score=89 bulkscore=0 phishscore=0 mlxlogscore=-91 suspectscore=0 malwarescore=0 adultscore=0 spamscore=89 classifier=spam adjust=0 reason=mlx scancount=l engine=8.12.0-2310240000 definitions=main-2310260209
In the process of reviewing a false positive, you see the following email header. What was the reason the message was quarantined by the Proofpoint Protection Server?
Which activity is part of the Preparation phase in the NIST lifecycle?
You would like to view the total number of uncleared threats or false positives that have been interacted with by users over the past 2 weeks. How can this be accomplished on the TAP Dashboard?
Which of the following is an item that should be included in an incident report as part of the post-incident debrief?
What is a defining characteristic of Advanced Persistent Threat (APT) actors?
Exhibit:

What can be determined by the threat information shown in the exhibit?
What best describes the nature of the NIST incident response lifecycle?
Which scenario would prevent URL Defense from rewriting a URL?
A college student receives the email shown in the exhibit.
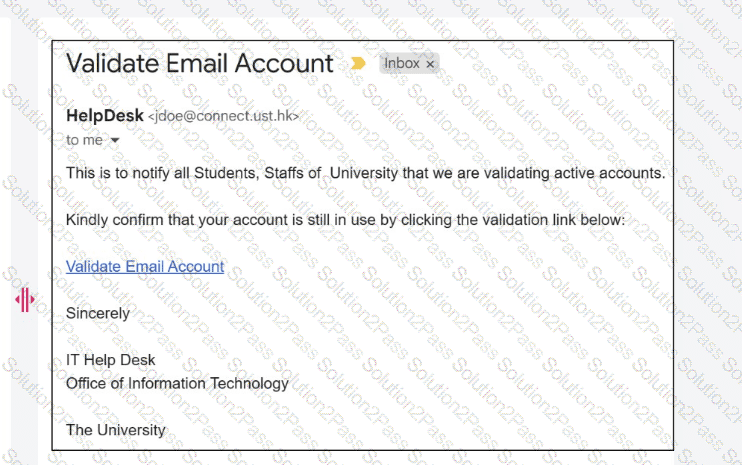
What type of attack is being performed?
