SCS-C03 Amazon Web Services AWS Certified Security – Specialty Free Practice Exam Questions (2026 Updated)
Prepare effectively for your Amazon Web Services SCS-C03 AWS Certified Security – Specialty certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
A company has the following security policy for its Amazon Aurora MySQL databases for a single AWS account:
• Database storage must be encrypted at rest.
• Deletion protection must be enabled.
• Databases must not be publicly accessible.
• Database audit logs must be published to Amazon CloudWatch Logs.
A security engineer must implement a solution thatcontinuously monitorsall Aurora MySQL resources for compliance with this policy. The solution must be able todisplay a database ' s compliance state for each part of the policy at any time.
Which solution will meet these requirements?
A company must immediately disable compromised IAM users across all AWS accounts and collect all actions performed by the user in the last 7 days.
Which solution will meet these requirements?
An ecommerce website was down for 1 hour following a DDoS attack. Users were unable to connect to the website during the attack period. The ecommerce company ' s security team is worried about future potential attacks and wants to prepare for such events. The company needs to minimize downtime in its response to similar attacks in the future.
Which steps would help achieve this? (Select TWO.)
A company has a VPC that has no internet access and has the private DNS hostnames option enabled. An Amazon Aurora database is running inside the VPC. A security engineer wants to use AWS Secrets Manager to automatically rotate the credentials for the Aurora database. The security engineer configures the Secrets Manager default AWS Lambda rotation function to run inside the same VPC that the Aurora database uses. However, the security engineer determines that the password cannot be rotated properly because the Lambda function cannot communicate with the Secrets Manager endpoint.
What is the MOST secure way that the security engineer can give the Lambda function the ability to communicate with the Secrets Manager endpoint?
A company is running a new workload across accounts that are in an organization in AWS Organizations. All running resources must have a tag ofCostCenter, and the tag must have one of three approved values. The company must enforce this policy and must prevent any changes of the CostCenter tag to a non-approved value.
Which solution will meet these requirements?
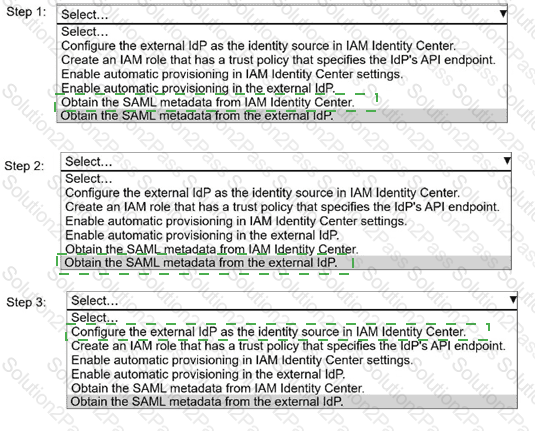
A security engineer needs to implement AWS IAM Identity Center with an external identity provider (IdP).
Select and order the correct steps from the following list to meet this requirement. Select each step one time or not at all. (Select and order THREE.)
. Configure the external IdP as the identity source in IAM Identity Center.
. Create an IAM role that has a trust policy that specifies the IdP ' s API endpoint.
. Enable automatic provisioning in IAM Identity Center settings.
. Enable automatic provisioning in the external IdP.
. Obtain the SAML metadata from IAM Identity Center.
. Obtain the SAML metadata from the external IdP.
A company is planning to deploy a new log analysis environment. The company needs to analyze logs from multiple AWS services in near real time. The solution must provide the ability to search the logs and must send alerts to an existing Amazon Simple Notification Service (Amazon SNS) topic when specific logs match detection rules.
Which solution will meet these requirements?
A company ' s security engineer is designing an isolation procedure for Amazon EC2 instances as part of an incident response plan. The security engineer needs to isolate a target instance to block any traffic to and from the target instance, except for traffic from the company ' s forensics team. Each of the company ' s EC2 instances has its own dedicated security group. The EC2 instances are deployed in subnets of a VPC. A subnet can contain multiple instances.
The security engineer is testing the procedure for EC2 isolation and opens an SSH session to the target instance. The procedure starts to simulate access to the target instance by an attacker. The security engineer removes the existing security group rules and adds security group rules to give the forensics team access to the target instance on port 22.
After these changes, the security engineer notices that the SSH connection is still active and usable. When the security engineer runs a ping command to the public IP address of the target instance, the ping command is blocked.
What should the security engineer do to isolate the target instance?
A company runs a web application on a fleet of Amazon EC2 instances that are in an Auto Scaling group. The EC2 instances are in the same VPC subnet as other workloads.
A security engineer deploys Amazon GuardDuty and integrates it with AWS Security Hub. The security engineer needs to implement anautomated solutionto detect and respond to anomalous traffic patterns. The solution must follow AWS best practices forinitial incident responseand mustminimize disruptionto the web application.
Which solution will meet these requirements?
A company’s application team needs a new AWS Key Management Service (AWS KMS) customer managed key to use with Amazon S3. The company’s security policy requires separate keys for different AWS services to limit security exposure.
How can a security engineer limit the KMS customer managed key to work with only Amazon S3?
A security team manages a company’s AWS Key Management Service (AWS KMS) customer managed keys. Only members of the security team can administer the KMS keys. The company ' s application team has a software process that needs temporary access to the keys occasionally. The security team needs to provide the application team ' s software process with access to the keys.
Which solution will meet these requirements with the LEAST operational overhead?
A company operates an Amazon EC2 instance that is registered as a target of a Network Load Balancer (NLB). The NLB is associated with a security group. The security group allows inbound TCP traffic on port 22 from 10.0.0.0/23.
The company maps the NLB to two subnets that share the same network ACL and route table. The route table has a route for 0.0.0.0/0 to an internet gateway. The network ACL has one inbound rule that has a priority of 20 and that allows TCP traffic on port 22 from 10.0.0.0/16.
A security engineer receives an alert that there is an unauthorized SSH session on the EC2 instance. The unauthorized session originates from 10.0.1.5. The company ' s incident response procedure requires unauthorized SSH sessions to beimmediately interrupted. The instance must remain running, and its memory must remain intact.
Which solution will meet these requirements?
A company uses an organization in AWS Organizations to manage its 250 member accounts. The company also uses AWS IAM Identity Center with a SAML external identity provider (IdP). IAM Identity Center has been delegated to a member account. The company ' s security team has access to the delegated account.
The security team has been investigating a malicious internal user who might be accessing sensitive accounts. The security team needs to know when the user logged into the organization during the last 7 days.
Which solution will quickly identify the access attempts?
A company is using Amazon Macie, AWS Firewall Manager, Amazon Inspector, and AWS Shield Advanced in its AWS account. The company wants to receive alerts if a DDoS attack occurs against the account.
Which solution will meet this requirement?
A company runs an internet-accessible application on several Amazon EC2 instances that run Windows Server. The company used an instance profile to configure the EC2 instances. A security team currently accesses the VPC that hosts the EC2 instances by using an AWS Site-to-Site VPN tunnel from an on-premises office. The security team issues a policy that requires all external access to the VPC to be blocked in the event of a security incident. However, during an incident, the security team must be able to access the EC2 instances to obtain forensic information on the instances.
Which solution will meet these requirements?
A company uses AWS Organizations. The company has teams that use an AWS CloudHSM hardware security module (HSM) that is hosted in a central AWS account. One of the teams creates its own new dedicated AWS account and wants to use the HSM that is hosted in the central account.
How should a security engineer share the HSM that is hosted in the central account with the new dedicated account?
A company runs an application on an Amazon EC2 instance. The application generates invoices and stores them in an Amazon S3 bucket. The instance profile that is attached to the instance has appropriate access to the S3 bucket. The company needs to share each invoice with multiple clients that do not have AWS credentials. Each client must be able to download only the client ' s own invoices. Clients must download their invoices within 1 hour of invoice creation. Clients must use only temporary credentials to access the company ' s AWS resources.
Which additional step will meet these requirements?
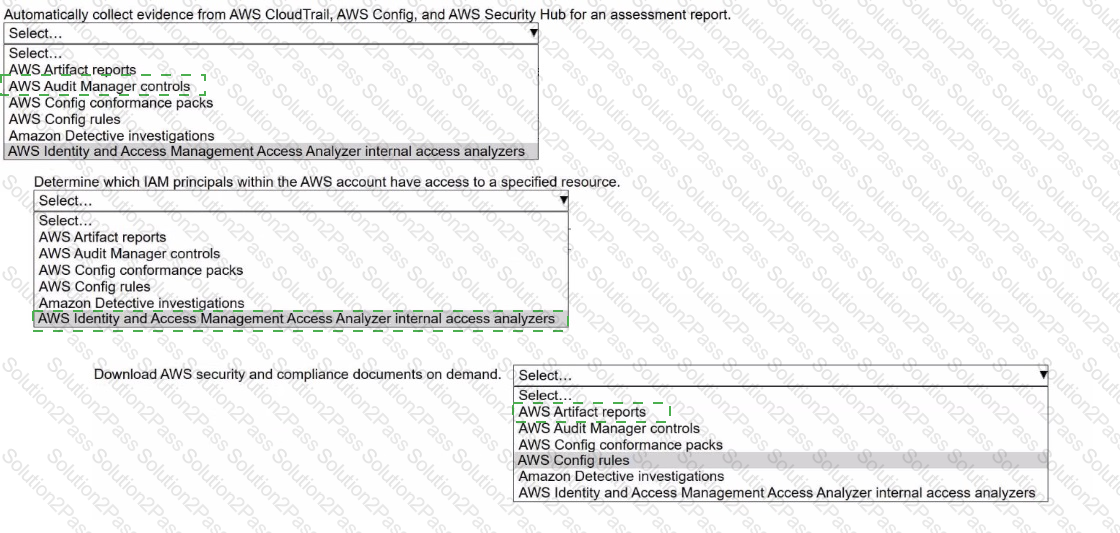
A security engineer needs to prepare for a security audit of an AWS account.
Select the correct AWS resource from the following list to meet each requirement. Select each resource one time or not at all. (Select THREE.)
• AWS Artifact reports
• AWS Audit Manager controls
• AWS Config conformance packs
• AWS Config rules
• Amazon Detective investigations
• AWS Identity and Access Management Access Analyzer internal access analyzers
A company runs a web application on a fleet of Amazon EC2 instances that are in an Auto Scaling group. The EC2 instances are in the same VPC subnet as other workloads.
A security engineer deploys an Amazon GuardDuty detector in the same AWS Region as the EC2 instances and integrates GuardDuty with AWS Security Hub.
The security engineer needs to implement an automated solution to detect and appropriately respond to anomalous traffic patterns for the web application. The solution must comply with AWS best practices forinitial response to security incidentsand mustminimize disruptionto the web application.
Which solution will meet these requirements?
A company wants to establish separate AWS Key Management Service (AWS KMS) keys to use for different AWS services. The company ' s security engineer created the following key policy to allow the infrastructure deployment team to create encrypted Amazon Elastic Block Store (Amazon EBS) volumes by assuming the InfrastructureDeployment IAM role:
{
" Version " : " 2012-10-17 " ,
" Id " : " key-policy-ebs " ,
" Statement " : [
{
" Sid " : " Enable IAM User Permissions " ,
" Effect " : " Allow " ,
" Principal " : {
" AWS " : " arn:aws:iam::123456789012:root "
},
" Action " : " kms:* " ,
" Resource " : " * "
},
{
" Sid " : " Allow use of the key " ,
" Effect " : " Allow " ,
" Principal " : {
" AWS " : " arn:aws:iam::123456789012:role/aws-reserved/sso.amazonaws.com/InfrastructureDeployment "
},
" Action " : [
" kms:Encrypt " ,
" kms:Decrypt " ,
" kms:ReEncrypt* " ,
" kms:GenerateDataKey* " ,
" kms:DescribeKey " ,
" kms:CreateGrant " ,
" kms:ListGrants " ,
" kms:RevokeGrant "
],
" Resource " : " * " ,
" Condition " : {
" StringEquals " : {
" kms:ViaService " : " ec2.us-west-2.amazonaws.com "
}
}
}
]
}
The security engineer recently discovered that IAM rolesother thanthe InfrastructureDeployment role used this key for other services.
Which change to the policy should the security engineer make to resolve these issues?