200-201 Cisco Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS) Free Practice Exam Questions (2026 Updated)
Prepare effectively for your Cisco 200-201 Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS) certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
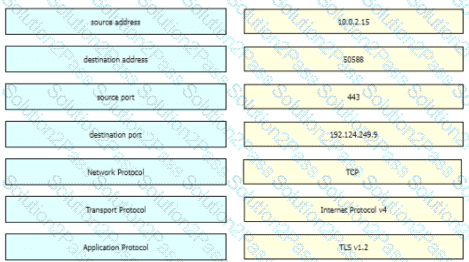
A suspicious user opened a connection from a compromised host inside an organization. Traffic was going through a router and the network administrator was able to identify this flow. The admin was following 5-tuple to collect needed data. Which information was gathered based on this approach?
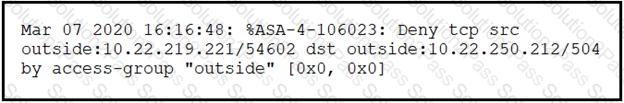
Refer to the exhibit.
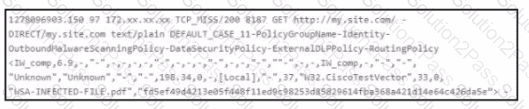
Which technology produced the log?
Developers must implement tasks on remote Windows environments. They decided to use scripts for enterprise applications through PowerShell. Why does the functionality not work?
Which type of evasion technique is accomplished by separating the traffic into smaller segments before transmitting across the network?
What is the difference between the rule-based detection when compared to behavioral detection?
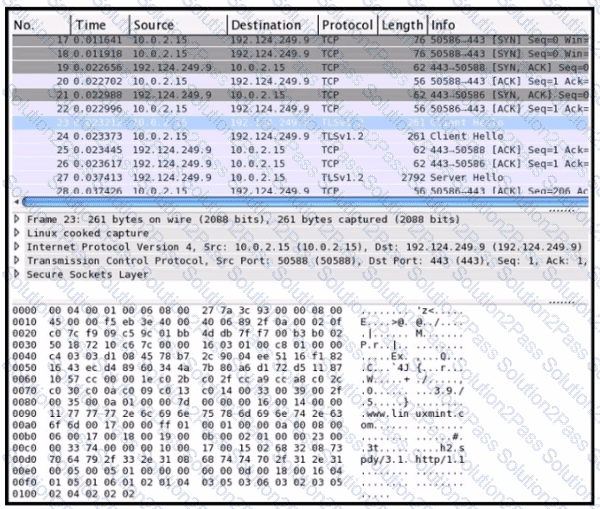
Refer to the exhibit Drag and drop the element names from the left onto the corresponding pieces of the PCAP file on the right.
Refer to the exhibit.
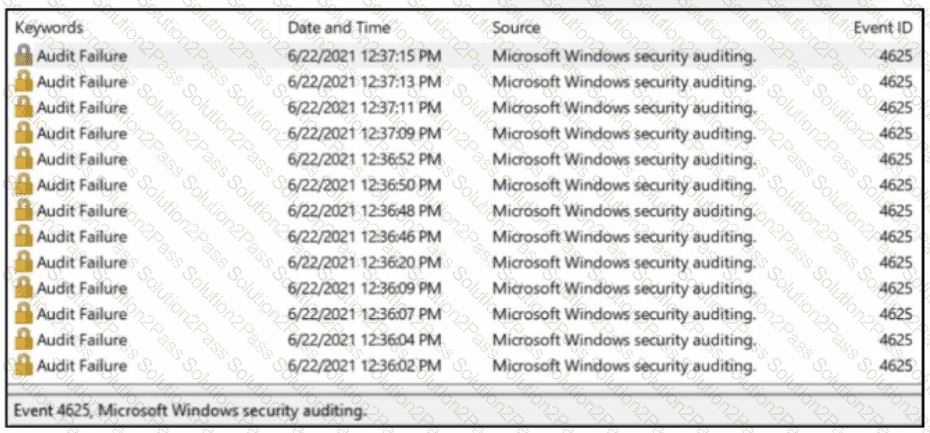
A SOC analyst received a message from SIEM about abnormal activity on the Windows server The analyst checked the Windows event log and saw numerous Audit Failures logs. What is occurring?
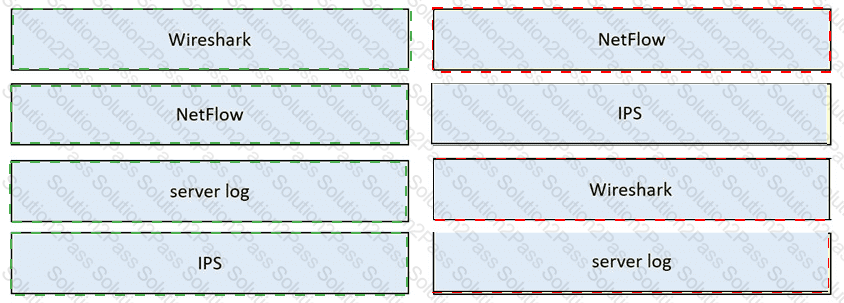
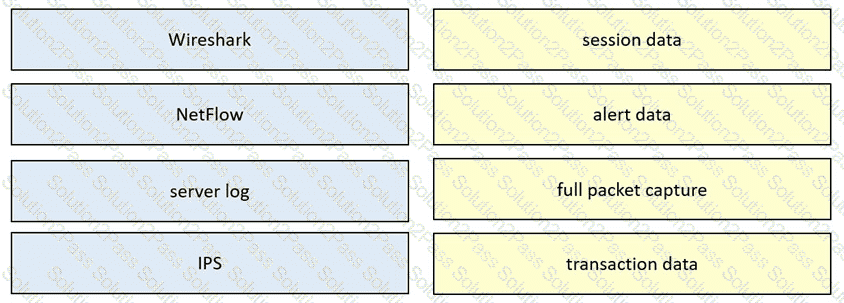
Drag and drop the data source from the left onto the data type on the right.
Which classification of cross-site scripting attack executes the payload without storing it for repeated use?
What is the difference between a threat and an exploit?
Refer to the exhibit.
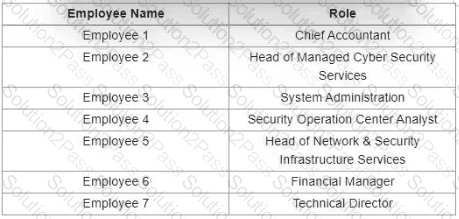
Which stakeholders must be involved when a company workstation is compromised?
Refer to the exhibit.
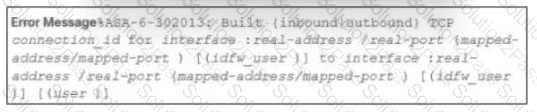
During the analysis of a suspicious scanning activity incident, an analyst discovered multiple local TCP connection events Which technology provided these logs?
Refer to the exhibit.
Which technology generates this log?
Which attack method is being used when an attacker tries to compromise a network with an authentication system that uses only 4-digit numeric passwords and no username?
Which step in the incident response process researches an attacking host through logs in a SIEM?
An analyst must choose one source of information for further troubleshooting. A key requirement is to use low storage space over the next 12 months while being able to quickly determine the source and scope of an attack to effectively mitigate it. Which source of information should the analyst choose?
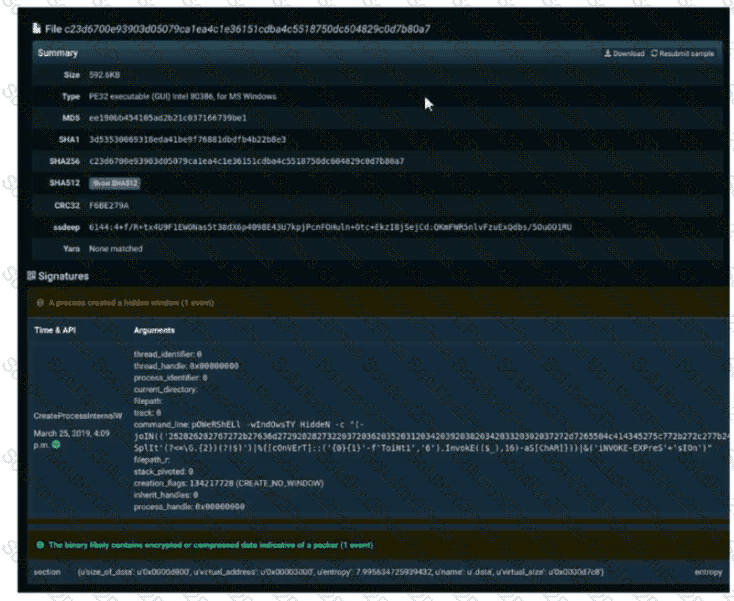
Refer to the exhibit. A SOC engineer is analyzing Cuckoo Sandbox report for a file that has been identified as suspicious by the endpoint security system. What is the state of the file?
Which of these is a defense-in-depth strategy principle?
How is SQL injection prevented?
What are the two characteristics of the full packet captures? (Choose two.)

 A screenshot of a computer Description automatically generated
A screenshot of a computer Description automatically generated