200-201 Cisco Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS) Free Practice Exam Questions (2026 Updated)
Prepare effectively for your Cisco 200-201 Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS) certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
Which type of attack is a blank email with the subject "price deduction" that contains a malicious attachment?
An analyst received a ticket about degraded processing capability for one of the HR department's servers. On the same day, an engineer noticed disabled antivirus software and could not determine when or why it occurred. According to the NIST Incident Handling Guide, what is the next phase of this investigation?
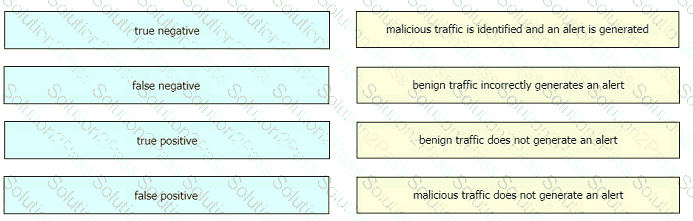
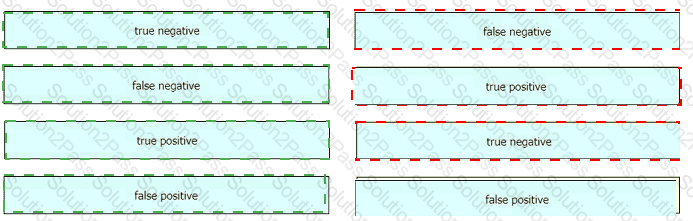
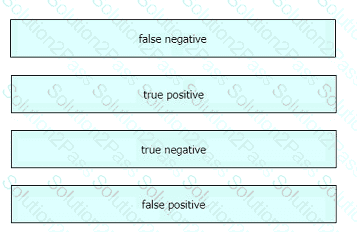
Drag and drop the event term from the left onto the description on the right.
A security engineer must protect the company from known issues that trigger adware. Recently new incident has been raised that could harm the system. Which security concepts are present in this scenario?
Refer to the exhibit.
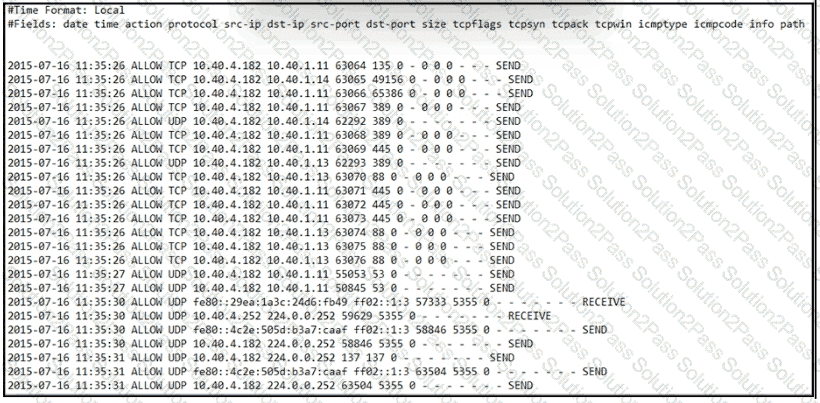
An engineer received an event log file to review. Which technology generated the log?
What is the difference between a vulnerability and an attack surface?
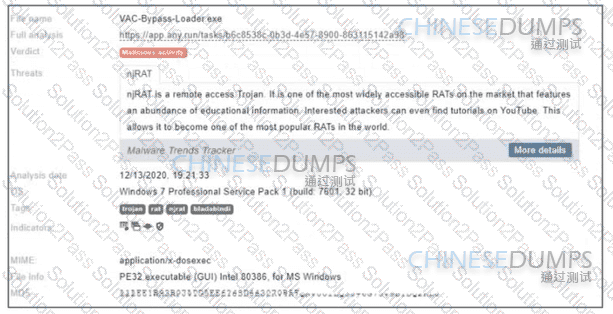
Refer to the exhibit. Where is the executable file?
What is the relationship between a vulnerability and a threat?
Which management concept best describes developing, operating, maintaining, upgrading, and disposing of all resources?
What describes the public key infrastructure (PKI)?
What is a difference between signature-based and behavior-based detection?
Which security principle requires more than one person is required to perform a critical task?
An intruder attempted malicious activity and exchanged emails with a user and received corporate information, including email distribution lists. The intruder asked the user to engage with a link in an email. When the fink launched, it infected machines and the intruder was able to access the corporate network.
Which testing method did the intruder use?
What is the difference between discretionary access control (DAC) and role-based access control (RBAC)?
Which technique is a low-bandwidth attack?
What is a description of "phishing" as a social engineering attack"?
An analyst is using the SIEM platform and must extract a custom property from a Cisco device and capture the phrase, "File: Clean." Which regex must the analyst import?
An engineer is working on the implementation of digital certificates for new cntical web applications One of the requirements is that the https connection must be validated and protected against malicious network impersonators The server will be exposed externally from the DMZ network Which certificate must be used?
What is the impact of false positive alerts on business compared to true positive?

Refer to the exhibit. An attacker scanned the server using Nmap. What did the attacker obtain from this scan?
 A screenshot of a computer Description automatically generated
A screenshot of a computer Description automatically generated