350-601 Cisco Implementing Cisco Data Center Core Technologies (350-601 DCCOR) Free Practice Exam Questions (2026 Updated)
Prepare effectively for your Cisco 350-601 Implementing Cisco Data Center Core Technologies (350-601 DCCOR) certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
An administrator in UCS Manager must enable its users to reboot and decommission the servers and perform backup jobs Which set of user privileges permits these activities?
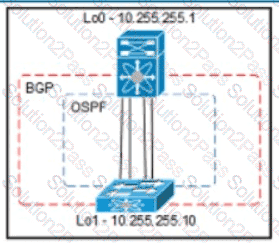
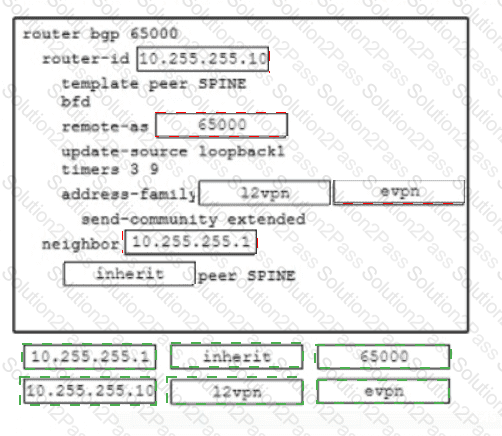
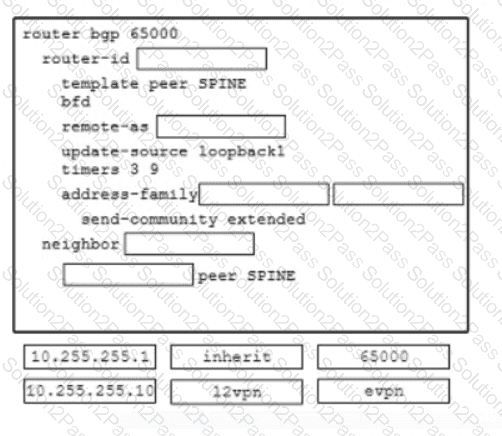
Refer to the exhibit An engineer must provision a VXLAN deployment The OSPF has already been configured as the underlay protocol All BGP configurations will be performed using the template method The deployment must meet these requirements
The local update source for leaf switches must be loopback 1
The router ID must be the local loopback IP address
The external BGP connections must use a template name
Drag and drop the configuration snippets from the bottom to complete the configuration
Which Cisco Nexus Dashboard feature analyzes flow telemetry data that is streamed from a Cisco Nexus 9000 Series Switch?
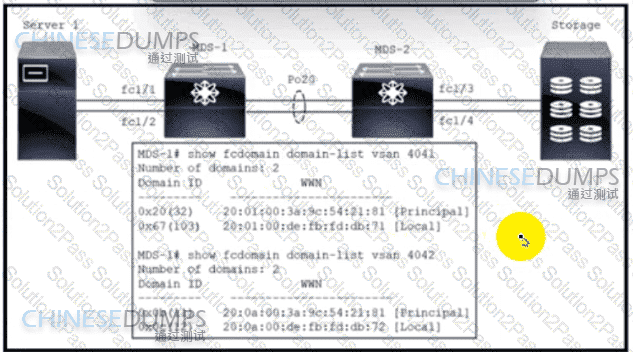
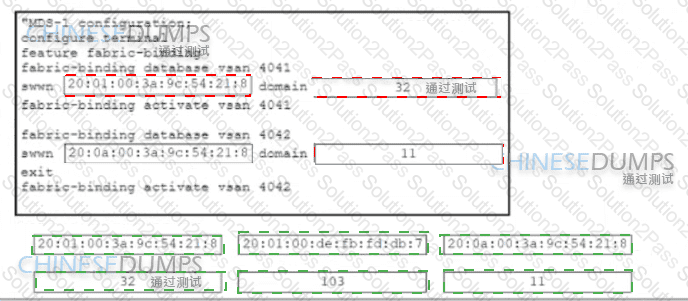
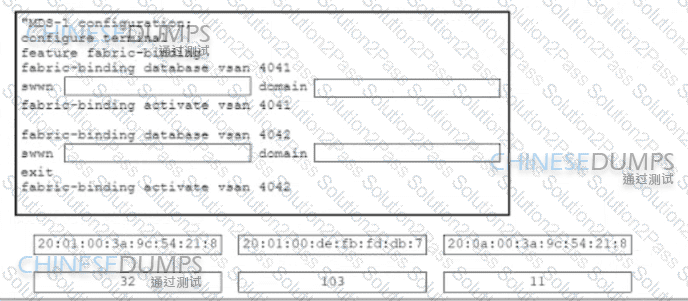
Refer to the exhibit The VSAN 4041 and 4042 are exchanged between two Cisco MDS 9000 Series Switches called MDS-1 and MDS-2 The objective is to deploy a security mechanism on MDS-1 to allow MDS-2 to join the fabric exclusively Drag and drop the code snippets from the bottom onto the boxes in the code to complete the MDS-1 configuration Not all code snippets are used.
Which API standard is used to manage the UCS-X in Intersight Managed Mode?
A Cisco UCS C-Series server needs to be installed in a data center. The server must be managed by using Cisco UCS Manager with a single cable for management and data traffic. Which set of commands must be run on the server after a physical connection is established?
A)
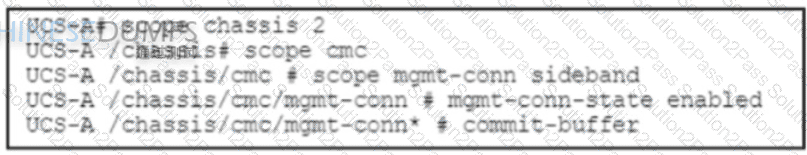
B)
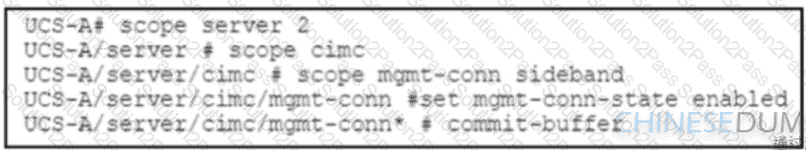
C)
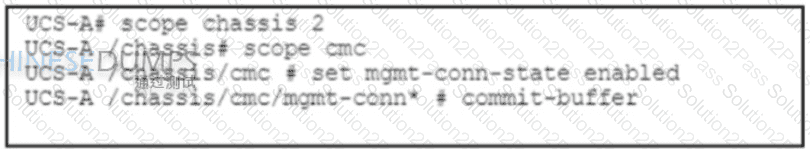
D)
An engineer is implementing traffic monitoring for a server vNIC that is configured with fabric failover enabled. The requirement is for the traffic to be sent to an analyzer, even during a failure of one of the fabric interconnects. The analyzer is connected to unconfigured Ethernet ports on both fabric interconnects. Which configuration accomplishes this task?
Which storage technology provides a simple, high-capacity solution and offers a direct file-access level to the shared storage?
An engineer implements an ACI fabric and must implement microsegmentation of endpoints within the same IP subnet using a network-based attribute. The attribute mapping must allow IP subnet independence. Which attribute must be selected?
A DevOps engineer must use Python to manage a Cisco device. The device is in a highly secure DMZ environment. Only trusted Cisco Python libraries can be used. Which solution meets
the requirements?
Which Cisco Nexus Dashboard service distributes Cisco ACI network configuration policies and templates to different data centers?
An engineer configures a storage environment for a customer with high- security standards. The secure environment is configured in vsan 50. The customer wants to maintain a configuration and active databases and prevent unauthorized switches from joining the fabric. Additionally, the switches must prevent rogue devices from connecting to their ports by automatically learning the WWPNs of the ports connected to them for the first time. Which two configuration sets must be used to meet these requirements? (Chose two.)
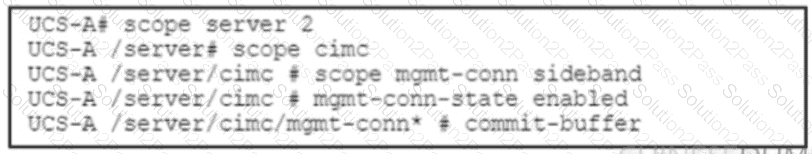
Refer to the exhibit. Which command must be used to configure a VXLAN NVE tunnel interface such that MAC and IP address information are learned in the control plane?
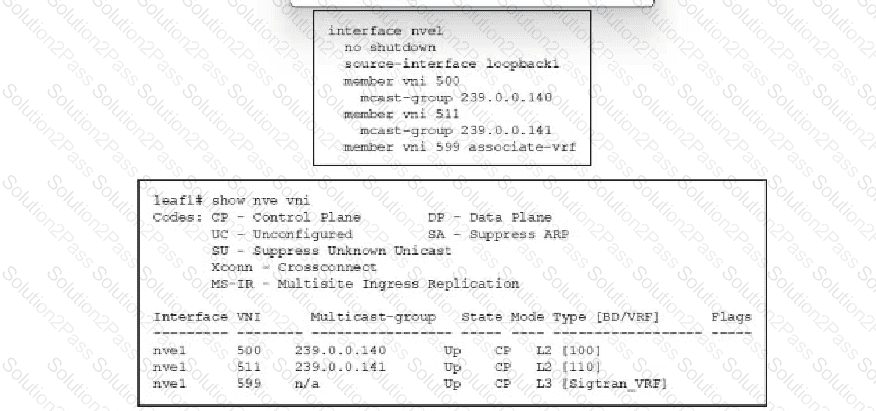
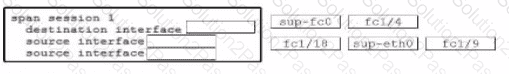
Refer to the exhibit. An engineer must capture Fibre Channel traffic from the server and the supervisor to the Cisco MDS 9000 Series Switch fabric. The traffic must be forwarded to the analyzer Drag and drop the code snippets from the right onto the blanks in the code on the left to complete the configuration. Not all code snippets are used.
A customer asks an engineer to develop a framework that will be used to replace the process of the manual device configuration of Cisco NX-OS devices The engineer plans to use the programmatic
interface that meets these requirements:
The development team is familiar with Windows-based scripting environment using PowerShell.
The customer’s secunty requirements mandate the use of HTTPS transport.
Which solution must be used to meet these requirements?
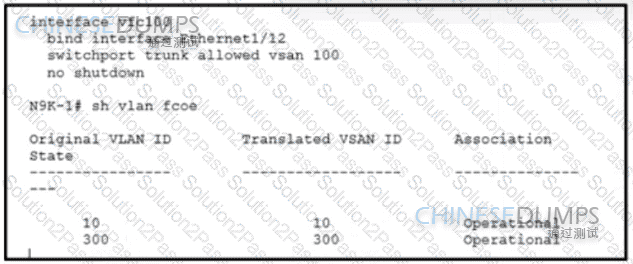
Refer to the exhibit. An engineer configures FCoE in a newly installed data center Which configuration must be applied to activate VSAN 100 on VFC 100?
DNS server with IP address 192.168.1.1 is deployed in a data center A network engineer must configure a Cisco UCS Fabric Interconnect to use this DNS. Which configuration should be applied?
An engineer must configure a user role interface policy on a Cisco Nexus 9000 Series Switch. The role must prevent access to interface FC3/2 but allow access to interface FC3/1. Which
set of actions must be taken to accomplish this goal?
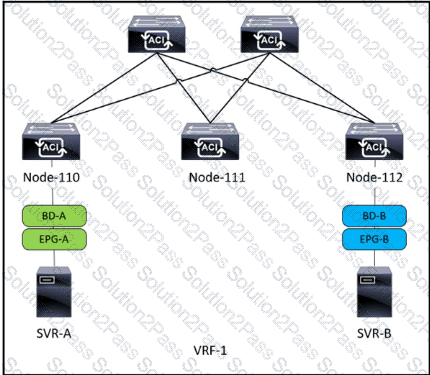
Refer to the exhibit. SVR-A in EPG-A/BD-A fails to reach SVR-B in EPG-B/BD-B. Which two conditions should be verified to analyze the traffic between the two EPGs? (Choose two.)
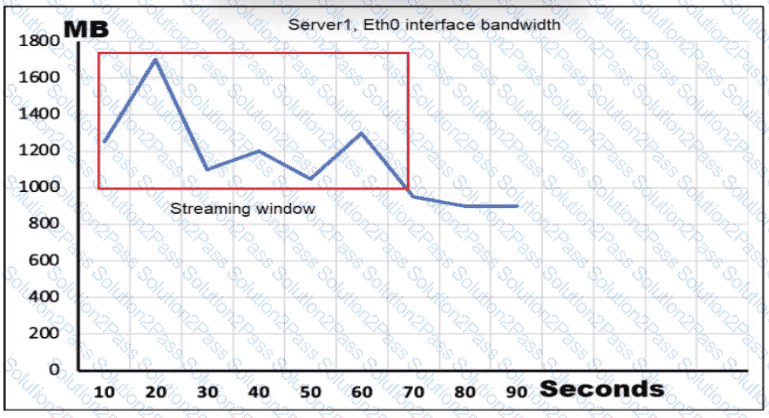
Refer to the exhibit. Server1 is connected to a Cisco Nexus 9000 Series Switch via a 1-Gb pod channel. The storm control is applied to the Eth0 device with a zero percent value What does the switch do to traffic that traverses the switch interfaces during the streaming window that exceeds the bandwidth of the interfaces?