PT0-003 CompTIA PenTest+ Exam Free Practice Exam Questions (2026 Updated)
Prepare effectively for your CompTIA PT0-003 CompTIA PenTest+ Exam certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
Which of the following is within the scope of proper handling and most crucial when working on a penetration testing report?
During a penetration test, the tester wants to obtain public information that could be used to compromise the organization ' s cloud infrastructure. Which of the following is the most effective resource for the tester to use for this purpose?
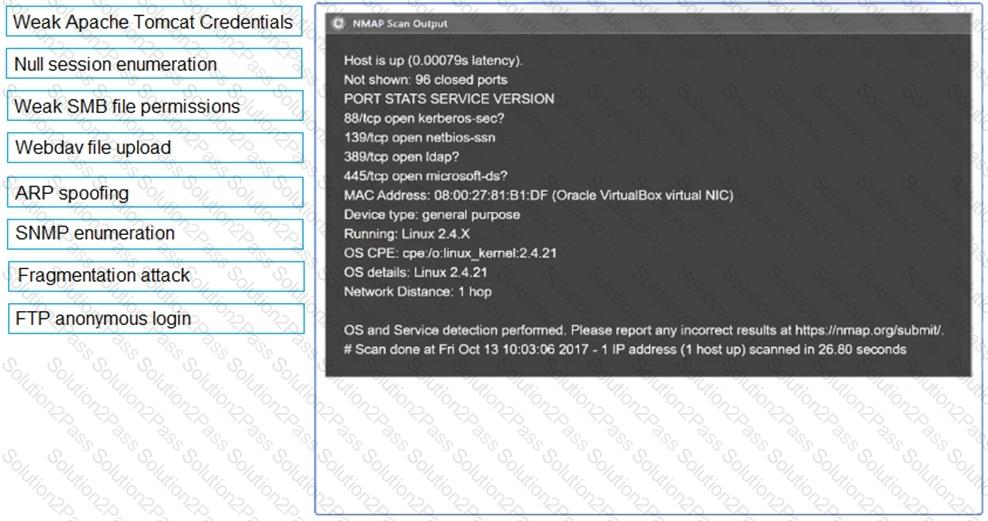
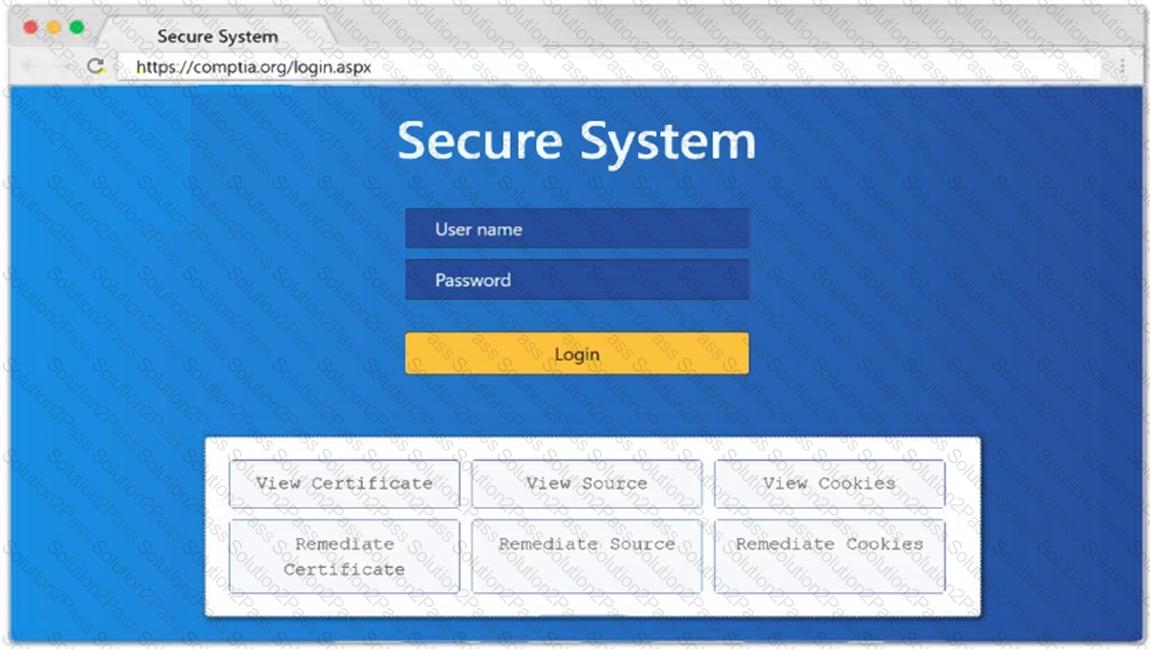
SIMULATION
Using the output, identify potential attack vectors that should be further investigated.
Which of the following activities should be performed to prevent uploaded web shells from being exploited by others?
Which of the following is the most efficient way to infiltrate a file containing data that could be sensitive?
A company ' s incident response team determines that a breach occurred because a penetration tester left a web shell. Which of the following should the penetration tester have done after the engagement?
A penetration tester discovers evidence of an advanced persistent threat on the network that is being tested. Which of the following should the tester do next?
A penetration tester is getting ready to conduct a vulnerability scan as part of the testing process. The tester will evaluate an environment that consists of a container orchestration cluster. Which of the following tools should the tester use to evaluate the cluster?
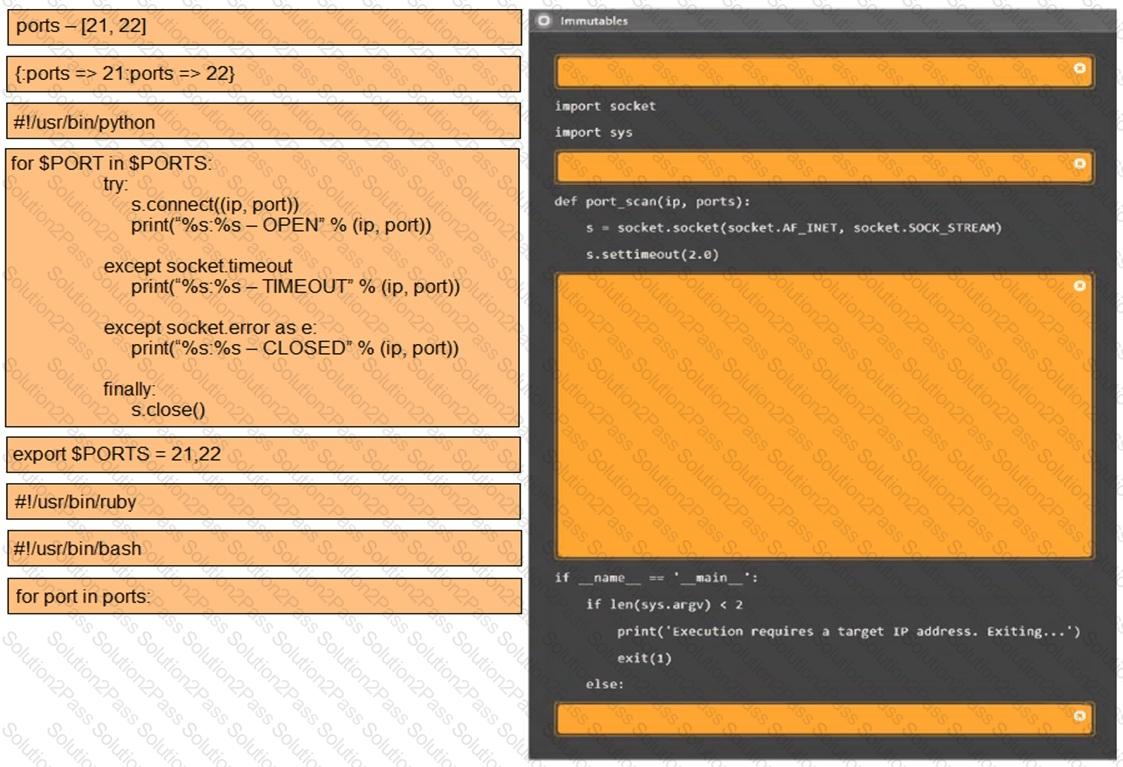
A penetration tester cannot use Nmap and must perform port discovery and banner grabbing for potential vulnerable SSH services. Given the following script:
#!/usr/bin/bash
ip_address = " 192.168.5. "
...
for i in {1..254}
do
--missing command--
done
...
Which of the following commands will best help the tester achieve this objective?
A company wants to perform a BAS (Breach and Attack Simu-lation) to measure the efficiency of the corporate security controls. Which of the following would most likely help the tester with simple command examples?
Testing and reporting activities are complete. A penetration tester needs to verify that exploited systems have been restored to preengagement conditions. Which of the following would be most appropriate for the tester to do?
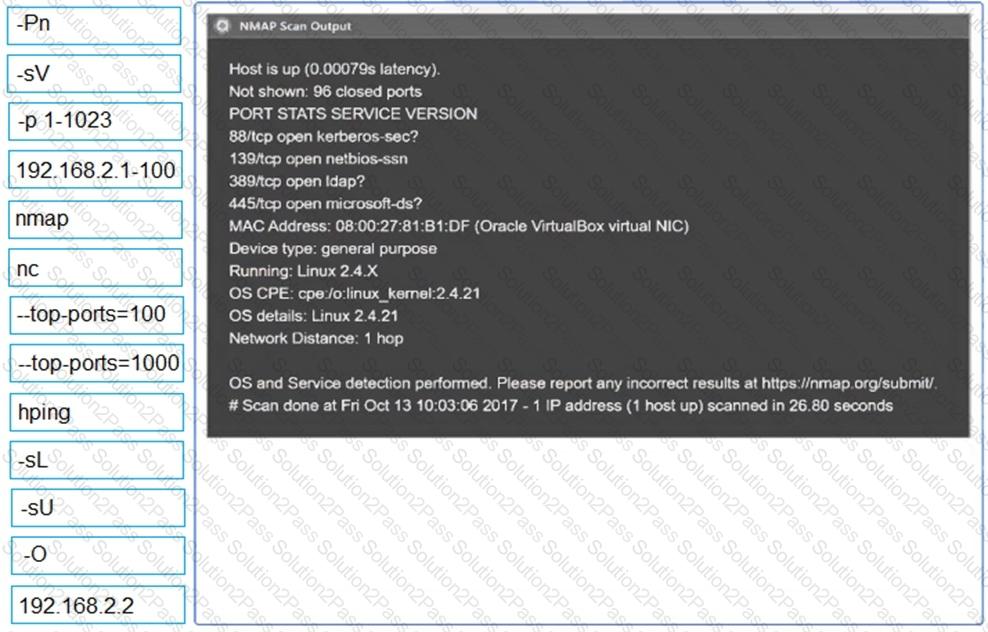
A penetration tester needs to confirm the version number of a client ' s web application server. Which of the following techniques should the penetration tester use?
A penetration tester established an initial compromise on a host. The tester wants to pivot to other targets and set up an appropriate relay. The tester needs to enumerate through the compromised host as a relay from the tester ' s machine. Which of the following commands should the tester use to do this task from the tester ' s host?
A penetration tester wants to gather the names of potential phishing targets who have access to sensitive data. Which of the following would best meet this goal?
A penetration tester uses the Intruder tool from the Burp Suite Community Edition while assessing a web application. The tester notices the test is taking too long to complete. Which of the following tools can the tester use to accelerate the test and achieve similar results?
During a vulnerability assessment, a penetration tester configures the scanner sensor and performs the initial vulnerability scanning under the client ' s internal network. The tester later discusses the results with the client, but the client does not accept the results. The client indicates the host and assets that were within scope are not included in the vulnerability scan results. Which of the following should the tester have done?
A penetration testing team needs to determine whether it is possible to disrupt the wireless communications for PCs deployed in the client ' s offices. Which of the following techniques should the penetration tester leverage?
A penetration tester obtains a regular domain user ' s set of credentials. The tester wants to attempt a dictionary attack by creating a custom word list based on the Active Directory password policy. Which of the following tools should the penetration tester use to retrieve the password policy?
During a red-team exercise, a penetration tester obtains an employee ' s access badge. The tester uses the badge ' s information to create a duplicate for unauthorized entry. Which of the following best describes this action?
During an assessment, a penetration tester plans to gather metadata from various online files, including pictures. Which of the following standards outlines the formats for pictures, audio, and additional tags that facilitate this type of reconnaissance?
