SY0-701 CompTIA Security+ Exam 2026 Free Practice Exam Questions (2026 Updated)
Prepare effectively for your CompTIA SY0-701 CompTIA Security+ Exam 2026 certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
A security engineer receives reports of unauthorized devices on the organization ' s network. Which of the following best describes a secure and effective way to mitigate the risks?
A systems administrator is auditing all company servers to ensure. They meet the minimum security baseline While auditing a Linux server, the systems administrator observes the /etc/shadow file has permissions beyond the baseline recommendation. Which of the following commands should the systems administrator use to resolve this issue?
A company performs risk analysis on its equipment and estimates it will experience about ten incidents over a five-year period. Which of the following is the correct ARO for the equipment?
Which of the following technologies assists in passively verifying the expired status of a digital certificate?
A company ' s accounting department receives an urgent payment message from the company ' s bank domain with instructions to wire transfer funds. The sender requests that the transfer be completed as soon as possible. Which of the following attacks is described?
Which of the following would be the most appropriate way to protect data in transit?
Which of the following is the first step to take when creating an anomaly detection process?
A company needs to determine whether authentication weaknesses in a customer-facing web application exist. Which of the following is the best technique to use?
A university employee logged on to the academic server and attempted to guess the system administrators ' log-in credentials. Which of the following security measures should the university have implemented to detect the employee ' s attempts to gain access to the administrators ' accounts?
Which of the following should a security administrator adhere to when setting up a new set of firewall rules?
A program manager wants to ensure contract employees can only use the company’s computers Monday through Friday from 9 a.m. to 5 p.m. Which of the following would best enforce this access control?
An organization authorizes system deployment on the network after reducing the number of Category 1 vulnerabilities to zero. Which of the following is this scenario an example of?
A newly appointed board member with cybersecurity knowledge wants the board of directors to receive a quarterly report detailing the number of incidents that impacted the organization. The systems administrator is creating a way to present the data to the board of directors. Which of the following should the systems administrator use?
A security administrator needs to reduce the attack surface in the company ' s data centers. Which of the following should the security administrator do to complete this task?
Which of the following is prevented by proper data sanitization?
An administrator must implement a solution that provides security and network connectivity between two companies. Which of the following infrastructure solutions is the best for this purpose?
An accounting clerk sent money to an attacker ' s bank account after receiving fraudulent instructions over the phone to use a new account. Which of the following would most likely prevent this activity in the future?
A security administrator wants to determine if the company ' s social engineering training is effective. Which of the following should the administrator do to complete this task?
A database administrator is updating the company ' s SQL database, which stores credit card information for pending purchases. Which of the following is the best method to secure the data against a potential breach?
Which of the following is a preventive physical security control?
A new employee logs in to the email system for the first time and notices a message from human resources about onboarding. The employee hovers over a few of the links within the email and discovers that the links do not correspond to links associated with the company. Which of the following attack vectors is most likely being used?
Which of the following steps in the risk management process involves establishing the scope and potential risks involved with a project?
An administrator notices that several users are logging in from suspicious IP addresses. After speaking with the users, the administrator determines that the employees were not logging in from those IP addresses and resets the affected users’ passwords. Which of the following should the administrator implement to prevent this type of attack from succeeding in the future?
An organization is evaluating the cost of licensing a new solution to prevent ransomware. Which of the following is the most helpful in making this decision?
Which of the following is the most common data loss path for an air-gapped network?
A company is using a legacy FTP server to transfer financial data to a third party. The legacy system does not support SFTP, so a compensating control is needed to protect the sensitive, financial data in transit. Which of the following would be the most appropriate for the company to use?
A malicious insider from the marketing team alters records and transfers company funds to a personal account. Which of the following methods would be the best way to secure company records in the future?
Which of the following are cases in which an engineer should recommend the decommissioning of a network device? (Select two).
A security analyst is reviewing logs and discovers the following:
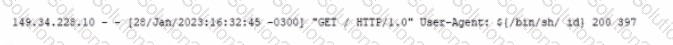
Which of the following should be used lo best mitigate this type of attack?
After reviewing the following vulnerability scanning report:
Server:192.168.14.6
Service: Telnet
Port: 23 Protocol: TCP
Status: Open Severity: High
Vulnerability: Use of an insecure network protocol
A security analyst performs the following test:
nmap -p 23 192.168.14.6 —script telnet-encryption
PORT STATE SERVICE REASON
23/tcp open telnet syn-ack
I telnet encryption:
| _ Telnet server supports encryption
Which of the following would the security analyst conclude for this reported vulnerability?
