XK0-006 CompTIA Linux+ V8 Exam Free Practice Exam Questions (2026 Updated)
Prepare effectively for your CompTIA XK0-006 CompTIA Linux+ V8 Exam certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
Which of the following is the main reason for setting up password expiry policies?
Which of the following describes what Ansible is used for in the context of IT infrastructure?
The development team asks a Linux administrator to help diagnose a connectivity issue that is occurring with a newly developed software. The Linux administrator reviews the following output:
$ wget -vvv https://api.newapp.comptia.org/v2/health
Resolving proxy.comptia.org (proxy.comptia.org)... connected.
ERROR: The certificate of ' api.newapp.comptia.org ' is not trusted.
ERROR: The certificate of ' api.newapp.comptia.org ' does not have a known issuer.
Which of the following actions is the best way to resolve the issue?
Which of the following utilities can securely delete a Linux directory from a filesystem and ensure it cannot be recovered?
A Linux user needs to authenticate to a Windows Active Directory domain. Which of the following configuration files contains the domain configuration details?
Which of the following describes PEP 8?
Which of the following describes the method of consolidating system events to a single location?
A systems administrator is restoring data from a backup. While analyzing the file format, the administrator sees the following output:
data: 7-zip archive data, version 0.4
Which of the following commands should the administrator use to help extract the data?
An administrator logs in to a Linux server and notices the clock is 37 minutes fast. Which of the following commands will fix the issue?
An administrator is trying to terminate a process that is not responding. Which of the following commands should the administrator use in order to force the termination of the process?
A Linux administrator just finished setting up passwordless SSH authentication between two nodes. However, upon test validation, the remote host prompts for a password. Given the following logs:
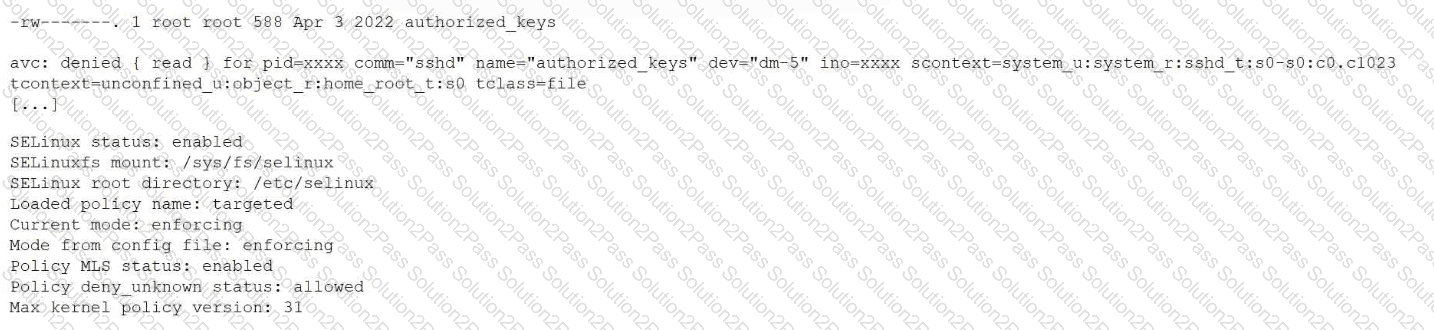
Which of the following is the most likely cause of the issue?
An administrator wants to search a file named myFile and look for all occurrences of strings containing at least five characters, where characters two and five are i, but character three is not b. Which of the following commands should the administrator execute to get the intended result?
A Linux administrator needs to compare two files and provide the output in the following format:
2,3d1
< Line 2
< Line 3
4a3
Line 5
Which of the following commands should the administrator use to perform the task?
Which of the following commands should a Linux administrator use to determine the version of a kernel module?
Which of the following best describes PEP 8?
A technician wants to temporarily use a Linux virtual machine as a router for the network segment 10.10.204.0/24. Which of the following commands should the technician issue? (Select three).
Which of the following describes how a user ' s public key is used during SSH authentication?
A systems administrator needs to integrate a new storage array into the company ' s existing storage pool. The administrator wants to ensure that the server is able to detect the new storage array. Which of the following commands should the administrator use to ensure that the new storage array is presented to the systems?
Users cannot access a server after it has been restarted. At the server console, the administrator runs the following commands;
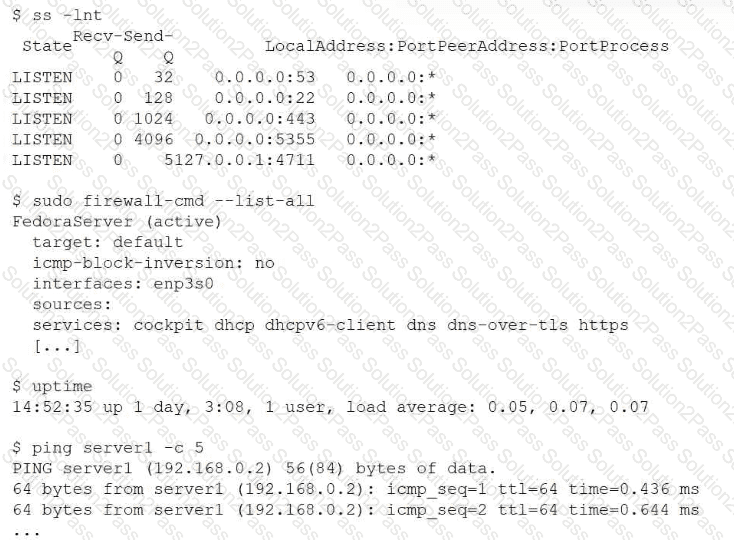
Which of the following is the cause of the issue?
Which of the following commands can be used to display real-time running processes on a Linux system?
