212-82 ECCouncil Certified Cybersecurity Technician (CCT) Free Practice Exam Questions (2026 Updated)
Prepare effectively for your ECCouncil 212-82 Certified Cybersecurity Technician (CCT) certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
As the IT security manager for a burgeoning e-commerce company, you're keen on implementing a formal risk management framework to proactively tackle security risks associated with the company's rapid online expansion. Given your focus one-commerce and the need for scalability, which risk management framework is likely the most relevant?
Johnson, an attacker, performed online research for the contact details of reputed cybersecurity firms. He found the contact number of sibertech.org and dialed the number, claiming himself to represent a technical support team from a vendor. He warned that a specific server is about to be compromised and requested sibertech.org to follow the provided instructions. Consequently, he prompted the victim to execute unusual commands and install malicious files, which were then used to collect and pass critical Information to Johnson's machine. What is the social engineering technique Steve employed in the above scenario?
Anderson, a security engineer, was Instructed to monitor all incoming and outgoing traffic on the organization's network to identify any suspicious traffic. For this purpose, he employed an analysis technique using which he analyzed packet header fields such as IP options, IP protocols, IP fragmentation flags, offset, and identification to check whether any fields are altered in transit.
Identify the type of attack signature analysis performed by Anderson in the above scenario.
Camden, a network specialist in an organization, monitored the behavior of the organizational network using SIFM from a control room. The SIEM detected suspicious activity and sent an alert to the camera. Based on the severity of the incident displayed on the screen, Camden made the correct decision and immediately launched defensive actions to prevent further exploitation by attackers.
Which of the following SIEM functions allowed Camden to view suspicious behavior and make correct decisions during a security incident?
Kason, a forensic officer, was appointed to investigate a case where a threat actor has bullied certain children online. Before proceeding legally with the case, Kason has documented all the supporting documents, including source of the evidence and its relevance to the case, before presenting it in front of the jury.
Which of the following rules of evidence was discussed in the above scenario?
A disgruntled employee transferred highly confidential tender data of upcoming projects as an encoded text. You are assigned to decode the text file snitch.txt located in the Downloads folder of the Attacker Machined and determine the value of the greenfarm project in dollars. Hint 1: All the cryptography tools are located at "Z:\CCT-Tools\CCT Module 14 Cryptography". Hint 2: If required, you can use sniffer@123 as the password to decode the file. (Practical Question)
Kaison. a forensic officer, was investigating a compromised system used for various online attacks. Kaison initiated the data acquisition process and extracted the data from the systems DVD-ROM. Which of the following types of data did Kaison acquire in the above scenario?
A software team at an MNC was involved in a project aimed at developing software that could detect the oxygen levels of a person without physical contact, a helpful solution for pandemic situations. For this purpose, the team used a wireless technology that could digitally transfer data between two devices within a short range of up to 5 m and only worked in the absence of physical blockage or obstacle between the two devices, identify the technology employed by the software team in the above scenario.
Wilson, a security specialist in an organization, was instructed to enhance its cloud network security. To achieve this, Wilson deployed a network routing solution that established and managed communication between the on-premises consumer network and VPCs via a centralized unit. Identity the method used by Wilson to achieve cloud network security in this scenario.
Charlie, a security professional in an organization, noticed unauthorized access and eavesdropping on the WLAN. To thwart such attempts, Charlie employed an encryption mechanism that used the RC4 algorithm to encrypt information in the data link layer. Identify the type of wireless encryption employed by Charlie in the above scenario.
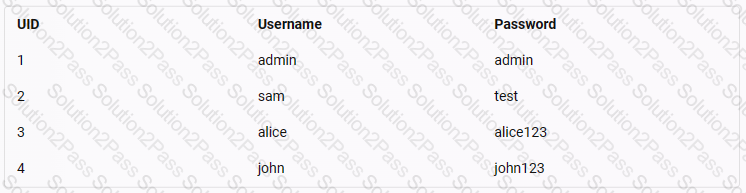
A web application, www.moviescope.com. hosted on your tarqet web server is vulnerable to SQL injection attacks. Exploit the web application and extract the user credentials from the moviescope database. Identify the UID (user ID) of a user, John, in the database. Note: Vou have an account on the web application, and your credentials are samAest.
(Practical Question)
As a cybersecurity technician, you were assigned to analyze the file system of a Linux image captured from a device that has been attacked recently. Study the forensic image'Evidenced.img" in the Documents folder of the "Attacker Machine-1" and identify a user from the image file. (Practical Question)
Zion belongs to a category of employees who are responsible for implementing and managing the physical security equipment installed around the facility. He was instructed by the management to check the functionality of equipment related to physical security. Identify the designation of Zion.
RevoMedia, a digital marketing agency, often conducts client presentations off-site. The agency’s team uses mobile devices to connect to various networks and display content. Withthe rising threat landscape, it wants to adopt the most secure method for connecting its mobile devices to unfamiliar networks. Which of the following should RevoMedia adopt?
Rhett, a security professional at an organization, was instructed to deploy an IDS solution on their corporate network to defend against evolving threats. For this purpose, Rhett selected an IDS solution that first creates models for possible intrusions and then compares these models with incoming events to make detection decisions.
Identify the detection method employed by the IDS solution in the above scenario.
Leo has walked to the nearest supermarket to purchase grocery. At the billing section, the billing executive scanned each product's machine-readable tag against a readable machine that automatically reads the product details, displays the prices of the individual product on the computer, and calculates the sum of those scanned items. Upon completion of scanning all the products, Leo has to pay the bill.
Identify the type of short-range wireless communication technology that the billing executive has used in the above scenario.
Richards, a security specialist at an organization, was monitoring an IDS system. While monitoring, he suddenly received an alert of an ongoing intrusion attempt on the organization's network. He immediately averted the malicious actions by implementing the necessary measures.
Identify the type of alert generated by the IDS system in the above scenario.
Alex, a certified security professional, works for both aggressor and defender teams. His team's main responsibility involves enhancing protection and boosting the security standards of the organization. Identify Alex's team in this scenario.
An attacker with malicious intent used SYN flooding technique to disrupt the network and gain advantage over the network to bypass the Firewall. You are working with a security architect to design security standards and plan for your organization. The network traffic was captured by the SOC team and was provided to you to perform a detailed analysis. Study the Synflood.pcapng file and determine the source IP address.
Note: Synflood.pcapng file is present in the Documents folder of Attacker-1 machine.
MediData, a leading healthcare data analytics firm based in the US, has made significant strides in advance health diagnostics using Al. With a vast repository of patient data and seeing the potential market In Europ MediData plans to expand its services there. However, the leadership is wary. Europe's stringent data protects regulations require companies to adapt their data processing practices. The legal team at MediData is task; with ensuring compliance and minimizing potential litigation or penalties. As MediData plans its Europe; expansion, which regulatory framework should it be most concerned with?