FCSS_EFW_AD-7.6 Fortinet NSE 7 - Enterprise Firewall 7.6 Administrator Free Practice Exam Questions (2026 Updated)
Prepare effectively for your Fortinet FCSS_EFW_AD-7.6 Fortinet NSE 7 - Enterprise Firewall 7.6 Administrator certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
Based on the TLS handshake shown, what can be inferred about the client?
Which two options integrate an additional FortiGate for scaling?
How will configuring set tcp-mss-sender and set tcp-mss-receiver in a firewall policy affect the size and handling of TCP packets in the network?
An administrator is setting up an ADVPN configuration and wants to ensure that peer IDs are not exposed during VPN establishment.
Which protocol can the administrator use to enhance security?
How do you resolve object conflicts when importing a policy package?
A company that acquired multiple branches across different countries needs to install new FortiGate devices on each of those branches. However, the IT staff lacks sufficient knowledge to implement the initial configuration on the FortiGate devices.
Which three approaches can the company take to successfully deploy advanced initial configurations on remote branches? (Choose three.)
Refer to the exhibit.
An administrator is deploying a hub and spokes network and using OSPF as dynamic protocol.
Which configuration is mandatory for neighbor adjacency?
Refer to the exhibit, which shows a network diagram showing the addition of site 2 with an overlapping network segment to the existing VPN IPsec connection between the hub and site 1.
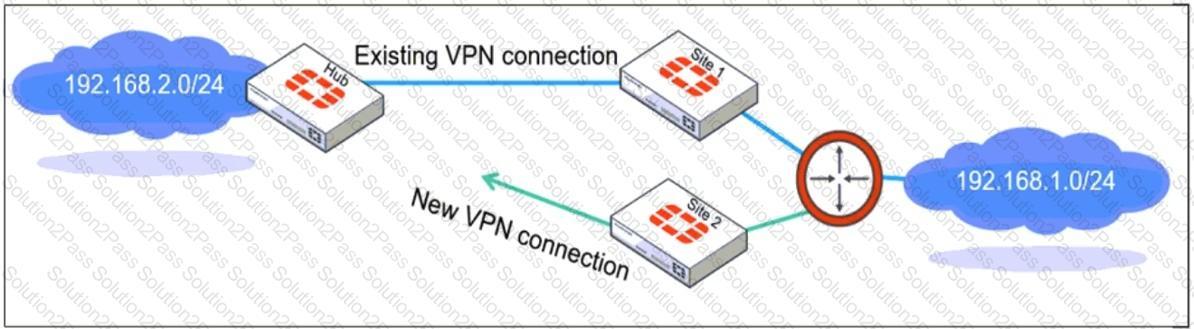
Which IPsec phase 2 configuration must an administrator make on the FortiGate hub to enable equal-cost multi-path (ECMP) routing when multiple remote sites connect with overlapping subnets?
Refer to the exhibit, which contains a partial command output.
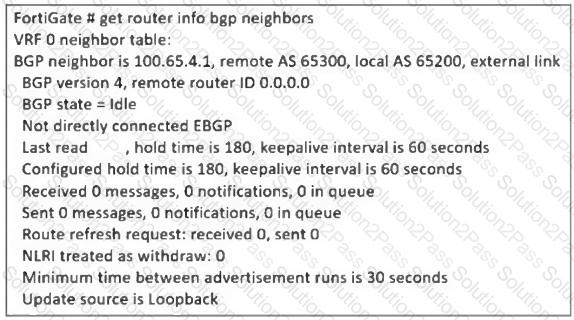
The administrator has configured BGP on FortiGate. The status of this new BGP configuration is shown in the exhibit.
What configuration must the administrator consider next?
Which two approaches facilitate efficient ADVPN deployment?
How can you ensure FortiGate can analyze encrypted HTTPS traffic?
Refer to the exhibit, which shows a hub and spokes deployment.
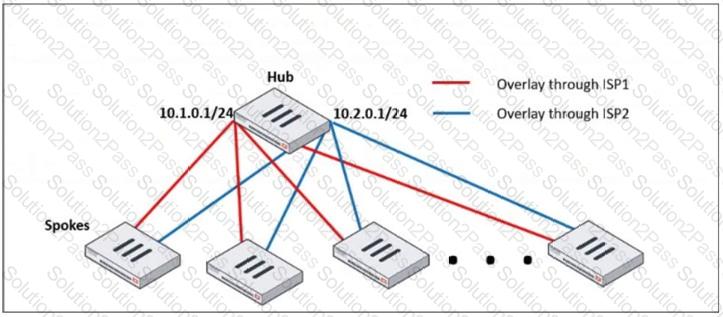
An administrator is deploying several spokes, including the BGP configuration for the spokes to connect to the hub.
Which two commands allow the administrator to minimize the configuration? (Choose two.)
To secure your enterprise network traffic, which step does FortiGate perform first, when handling the first packets of a session? (Choose one answer)
An administrator wants to scale the IBGP sessions and optimize the routing table in an IBGP network.
Which parameter should the administrator configure?
Refer to the exhibit, which shows the ADVPN network topology and partial BGP configuration.
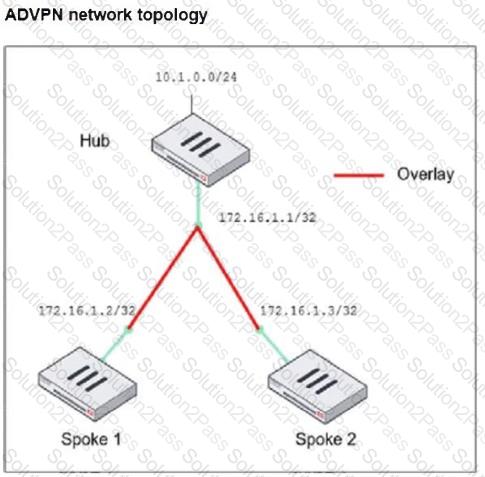
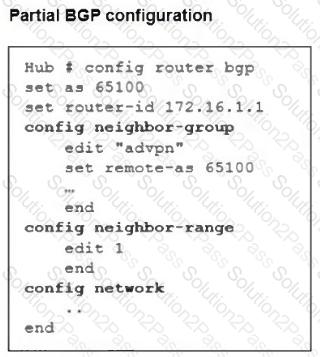
Which two parameters must an administrator configure in the config neighbor range for spokes shown in the exhibit? (Choose two.)
An administrator is checking an enterprise network and sees a suspicious packet with the MAC address e0:23:ff:fc:00:86.
What two conclusions can the administrator draw? (Choose two.)
How should you adjust MTU values to resolve encapsulation issues?
Refer to the exhibit, which shows the FortiGuard Distribution Network of a FortiGate device.
FortiGuard Distribution Network on FortiGate
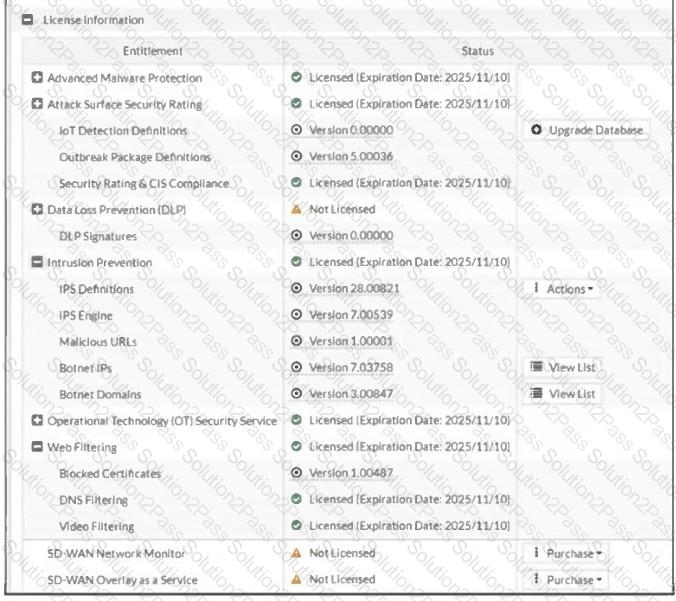
An administrator is trying to find the web filter database signature on FortiGate to resolve issues with websites not being filtered correctly in a flow-mode web filter profile.
Why is the web filter database version not visible on the GUI, such as with IPS definitions?
Which three approaches can successfully deploy advanced initial configurations?
Which two options should you consider to scale performance using an additional FortiGate?
