HPE6-A68 HP Aruba Certified ClearPass Professional (ACCP) 6.7 Free Practice Exam Questions (2026 Updated)
Prepare effectively for your HP HPE6-A68 Aruba Certified ClearPass Professional (ACCP) 6.7 certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
When is the RADIUS server certificate used? (Select two.)
Which components of a ClearPass is mandatory?
What is the purpose of RADIUS CoA (RFC 3576)?
Refer to the exhibit.
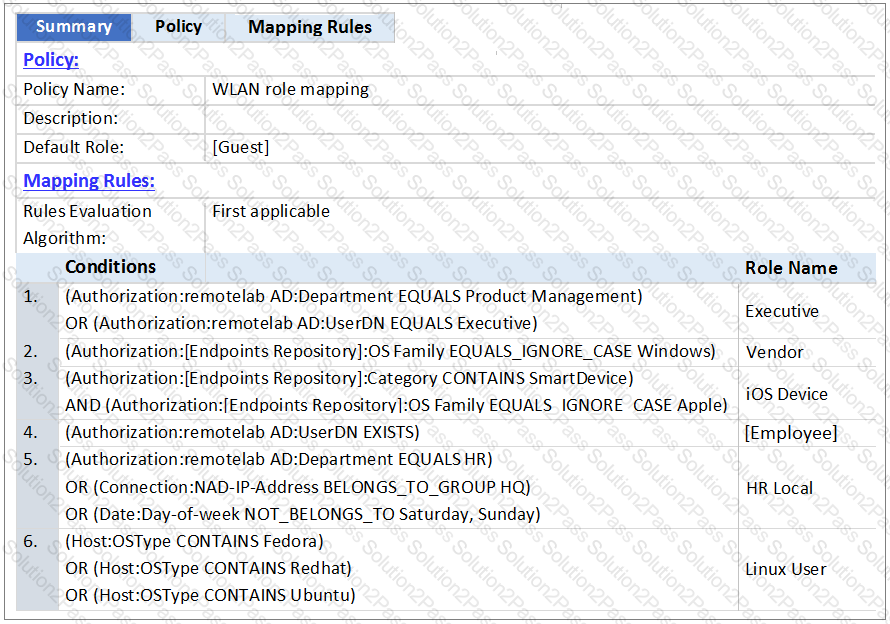
An AD user’s department attribute value is configured as “Product Management”. The user connects on Monday to a NAD that belongs to the Device Group HQ.
Which role is assigned to the user in ClearPass?
A customer wants all guests who access a company’s guest network to have their accounts approved by the receptionist, before they are given access to the network.
How should the network administrator set this up in ClearPass? (Select two.)
Refer to the exhibit.
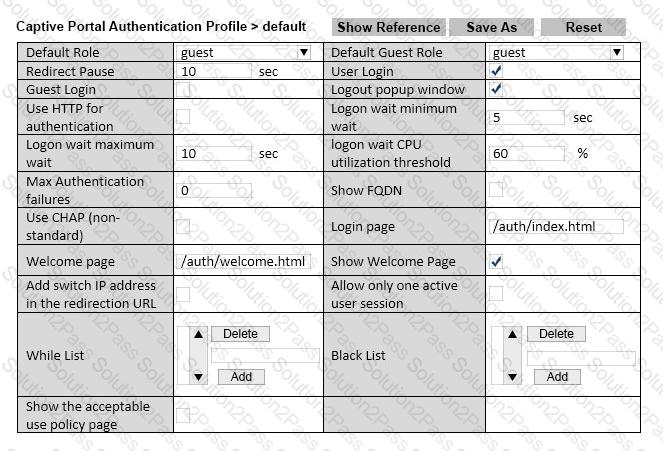
Based on the information shown, which field in the Captive Portal Authentication profile should be changed so that guest users are redirected to a page on ClearPass when they connect to the Guest SSID?
Refer to the exhibit.
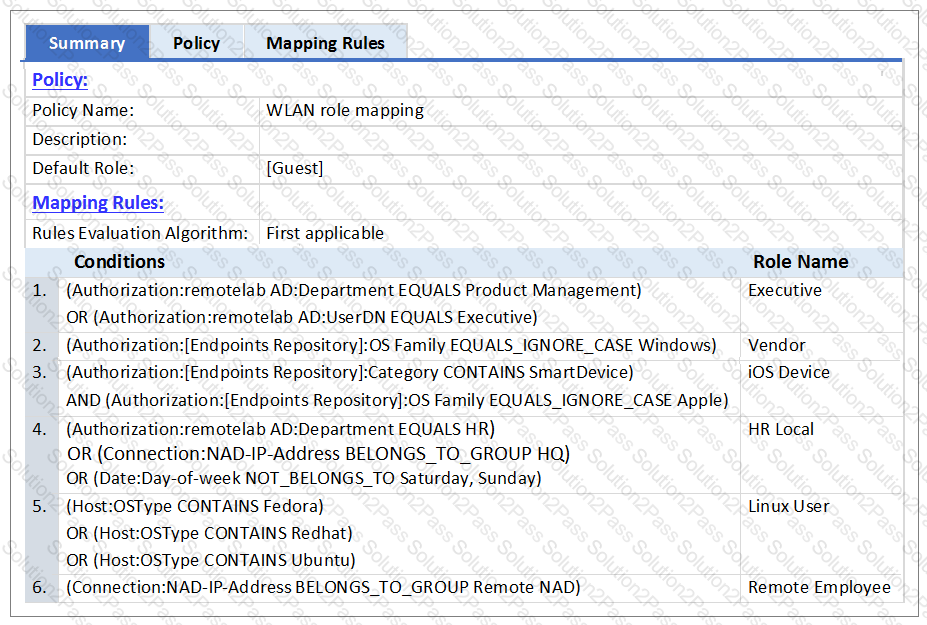
An AD user’s department attribute value is configured as “QA”. The user authenticates from a laptop running MAC OS X.
Which role is assigned to the user in ClearPass?
Refer to the exhibit.

What is the purpose of the ‘Clock Skew Allowance’ setting? (Select two.)
An Android device goes through the single-SSID Onboarding process and successfully connects using EAP-TLS to the secure network.
What is the order in which services are triggered?
Why is a terminate session enforcement profile used during posture checks with 802.1x authentication?
Refer to the exhibit.
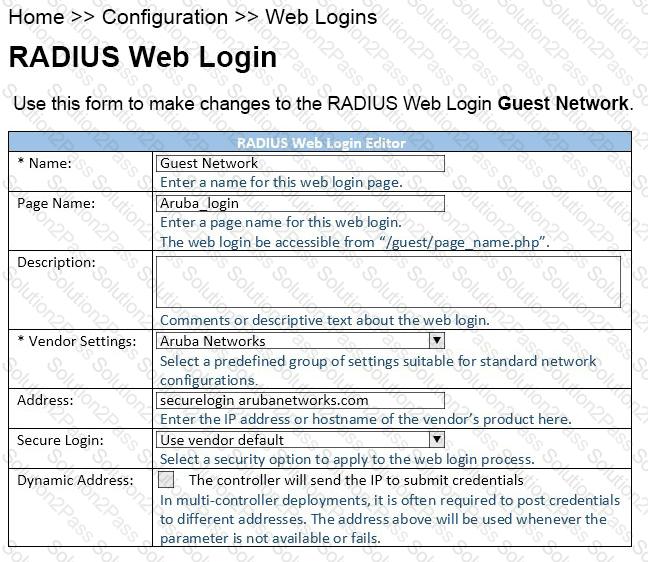
When configuring a Web Login Page in ClearPass Guest, the information shown is displayed.
What is the Address field value ‘securelogin.arubanetworks.com’ used for?
Which steps are required to use ClearPass as a TACACS+ Authentication server for a network device? (Select two.)
Which database in the Policy Manager contains the device attributes derived by profiling?
What does Authorization allow users to do in a Policy Service?
