H12-811_V2.0 Huawei HCIA-Datacom V2.0 Free Practice Exam Questions (2026 Updated)
Prepare effectively for your Huawei H12-811_V2.0 HCIA-Datacom V2.0 certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
According to the following routing table, it can be inferred that the IP address of VLANIF 2 on R1 is 10.0.12.1/24.
[R1] display ip routing-table
Proto: Protocol Pre: Preference
Route Flags: R - relay, D - download to fib, T - to vpn-instance, B - black hole route
Routing Table : public
Destinations : 10 Routes : 10
Destination/Mask Proto Pre Cost Flags NextHop Interface
10.0.12.0/24 Direct 0 0 D 10.0.12.1 Vlanif2
10.0.12.1/32 Direct 0 0 D 127.0.0.1 Vlanif2
10.0.12.255/32 Direct 0 0 D 127.0.0.1 Vlanif2
10.0.21.0/24 Direct 0 0 D 10.0.21.1 Vlanif3
10.0.21.1/32 Direct 0 0 D 127.0.0.1 Vlanif3
10.0.21.255/32 Direct 0 0 D 127.0.0.1 Vlanif3
R1 has four static routes, each of which has a reachable next hop. Given the following static route configuration, what is the next hop of the route to 20.0.0.0/30 in R1’s routing table?
[R1] ip route-static 20.0.0.0 30 10.1.1.2
[R1] ip route-static 20.0.0.0 30 10.1.2.2 preference 7 0
[R1] ip route-static 20.0.0.0 30 10.1.3.2 preference 50
[R1] ip route-static 20.0.0.0 30 10.1.4.2 preference 100
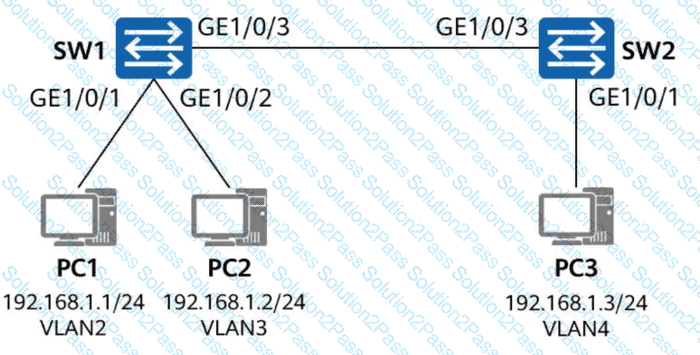
On the network shown in the figure, GE1/0/1 and GE1/0/2 of SW1 are access interfaces, and their PVIDs are VLAN 2 and VLAN 3 respectively. GE1/0/1 of SW2 is also an access interface, and its PVID is VLAN 4. Which of the following configurations on SW1 and SW2 can ensure that data packets sent from PC1 and PC2 can reach PC3?
Both SNMP Trap and Inform Request are used by managed devices to send alarms to the NMS. Inform Request requires an acknowledgment from the NMS, whereas Trap does not.
PC1 and PC2 are connected to the same switch, but they cannot learn each other’s ARP information. This may be caused by incorrect VLAN configuration on the switch.
You can enter a question mark (?) in the CLI of a Huawei switch to obtain online help. Which of the following statements is true about the meaning of < cr > in the output of the command sysname SW1?
[HUAWEI] sysname SW1?
< cr >
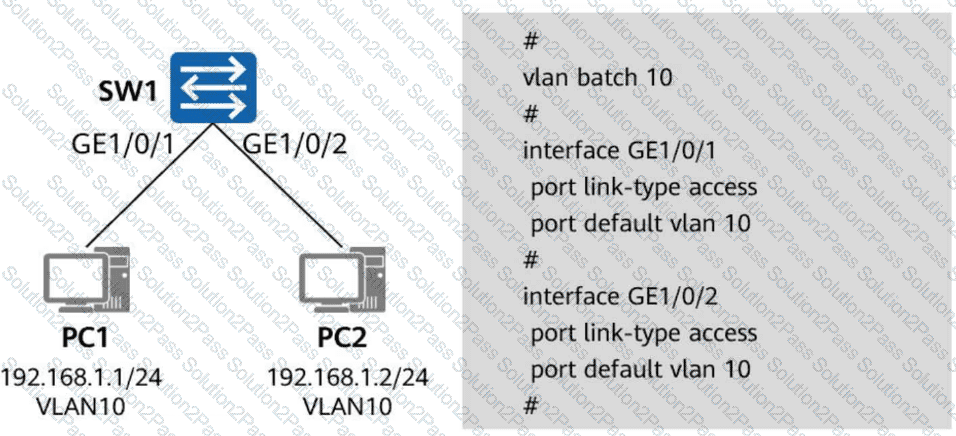
In the figure, both PC1 and PC2 belong to VLAN 10. Interface GE1/0/1 on SW1 is a trunk interface with the default PVID, and interface GE1/0/2 on SW1 is an access interface in VLAN 10. Which of the following statements are true about the forwarding of data frames between PC1 and PC2? (Select all that apply)
Which of the following commands can be used to check OSPF routes in the global routing table?
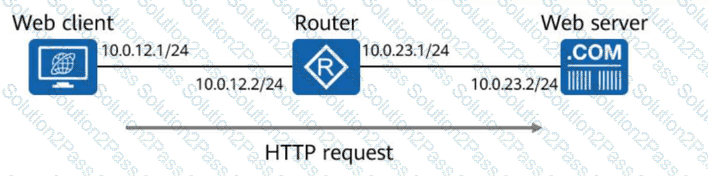
In the figure, a web client sends an HTTP request to a web server, and the router in between performs operations on the HTTP request. Which of the following statements are false about the router’s operations? (Select all that apply)
The following command output is displayed on R1:
[R1] display aaa configuration
Domain Name Delimiter : @
Domainname parse direction : Left to right
Domainname location : After-delimiter
Administrator user default domain : default_admin
Normal user default domain : default
Domain : total: 256 used: 3
Authentication-scheme : total: 32 used: 2
Accounting-scheme : total: 32 used: 1
Authorization-scheme : total: 32 used: 2
Service-scheme : total: 256 used: 0
Recording-scheme : total: 32 used: 0
Local-user : total: 512 used: 2
Remote-admin-user block retry-interval : 5 Min(s)
Remote-admin-user block retry-time : 3
Remote-admin-user block time : 5 Min(s)
Session timeout invalid enable : No
Which of the following statements is false?
On a switched network where STP is enabled on all devices, when a downstream device detects a topology change, it continuously sends configuration BPDUs to the upstream device until the root bridge is informed of the topology change.
In Layer 3 in-path WLAN networking, the WAC and Fit APs are connected at Layer 3. APs can obtain the WAC’s address through broadcast or DHCP.
With the development of data centers, a large number of services are deployed on virtual machines (VMs). The original VLAN isolation solution cannot achieve isolation between so many VMs. VXLAN uses VXLAN Network Identifiers (VNIs) to provide a larger range than VLAN IDs, so that a larger number of VMs can be isolated.
Secure Shell (SSH) is a protocol that uses encryption and authentication mechanisms to implement network services, such as secure access and file transfer, securely over an insecure network. Which of the following protocols use SSH? (Select all that apply)
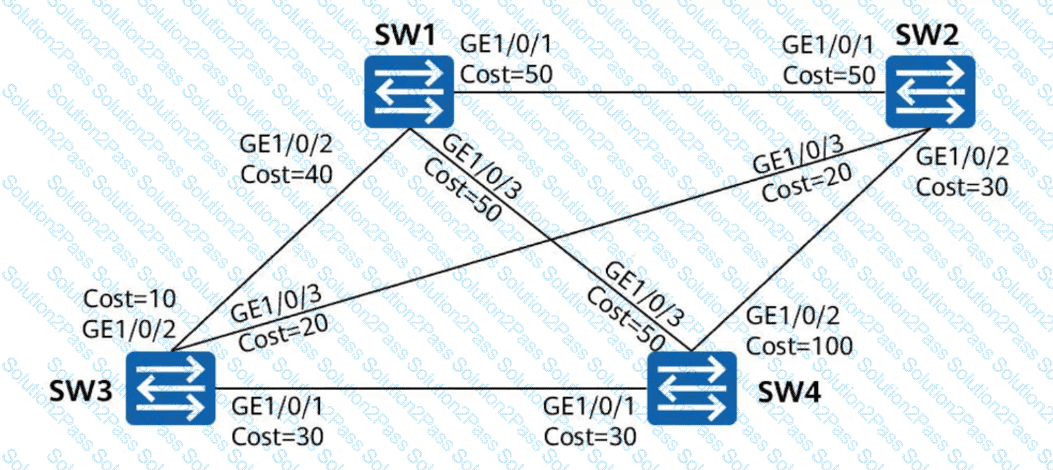
On the switched network shown in the figure, STP is enabled on all devices. SW1 is the root bridge. The port costs are shown in the figure. Other parameters retain the default values. After the network is stable, which of the following paths is used by SW1 to send traffic to SW4?
When a Huawei network device functions as an FTP server, which of the following are possible causes of an FTP client failing to log in to the FTP server? (Select all that apply)
DAD enables a node to detect whether an IPv6 address is already in use by another node before assigning it to an interface. This ensures that duplicate unicast addresses do not exist on a network. Which of the following packets are used for DAD? (Select all that apply)
The essence of communication is the transmission and exchange of information between two or more points. The three elements of communication are the sender, content, and transmission channel of the information. The receiver of the information is not included among these elements.
