H12-821_V1.0 Huawei HCIP-Datacom-Core Technology V1.0 Free Practice Exam Questions (2026 Updated)
Prepare effectively for your Huawei H12-821_V1.0 HCIP-Datacom-Core Technology V1.0 certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
Which of the following attacks is not the network layer attack?
Which of the following statements regarding the OSPF protocol is false?
Which of the following routing protocols support the default route through command configuration?
On an IS-IS network, each router can generate LSPs. Which of the following events trigger the generation of a new LSP?
In an MST region, MSTP independently calculates an MSTI for each VLAN based on mappings between VLANs and MSTIs.
Which of the following statements is false about the characteristics of MSTIs?
An ACL can be used to match routes or data, but cannot be used to match both the IP address prefix length and mask length.
According to BGP route selection rules, the route with the higher Local_Pref is preferred.
On an office network of an enterprise, OSPF is enabled on two directly connected routers. During adjacency establishment, the state machine stays in the 2-way state. Which of the following statements are not possible causes?
On the campus OSPF network shown in the following figure, the interfaces connecting the five routers are GE interfaces, and their costs are not changed. The import-route command is run on R1. After the network converges, the route to the server at 192.168.1.0/24 is queried on R2. Which of the following is the cost of this route?
The traffic limiting policy feature only supports the number of connections initiated by the specified IP or the number of connections received.
Four routers run ISIS and have established adjacencies. The area IDs and router levels are marked in the following figure. If route leaking is configured on R3, which of the following is the cost of the route from R4 to 10.0.2.2/32?
Security policy is the core feature of firewalls. Only valid traffic that complies with security policies can be forwarded by firewalls. Which of the following statements are true about security policy matching rules?
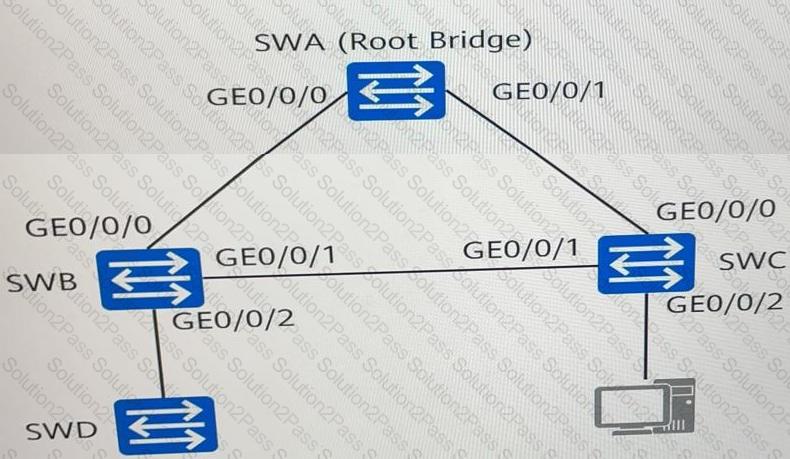
As shown in the figure, SWA, SWB, SWC, and SWD run the Rapid Spanning Tree Protocol (RSTP). Which of the following statements are true?
In IPv6, to communicate with a destination host, a host must obtain the link-layer address of the destination host through ARP.
Which of the following protocols are multi-channel protocols?
There are two types of routing entries on a PIM network. (S, G) routing entries are used to set up on a PIM network and are applicable to both PIM-DM and PIM-SM networks.
Which of the following statements regarding the BGP error display of a router false?
An OSPF AS-external LSA describes a route to an AS external network. When the field in the LSA is 0.0.0.0, the traffic destined for the external network is sent to the ASBR that imports this external route. (Enter the acronym in uppercase.)
Route attributes are specific descriptions of routes. BGP route attributes can be classified into four types. Which of the following are well-known discretionary attributes?
This configuration is part of RTA configuration. Which of the following statements regarding the configuration are true?
[RTA] ospf 100
[RTA-ospf-100]silent-interface GigabitEthernet 1/0/0
