H12-891_V1.0 Huawei HCIE-Datacom V1.0 Free Practice Exam Questions (2026 Updated)
Prepare effectively for your Huawei H12-891_V1.0 HCIE-Datacom V1.0 certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
Which of the following statements about OPS (Open Programmability System) application scenarios is incorrect?
Which of the following channels are involved in the Huawei SD-WAN Solution?
With telemetry, certain data can be sampled based on specific sampling paths. Which of the following sampling paths are supported by telemetry?
As shown in the figure, what is known about the default routes on R4?
Routing Table on R4:
< R4 > display ip routing-table protocol isis
Destination/Mask Proto Pre Cost Flags NextHop Interface
0.0.0.0/0 ISIS-L1 15 10 D 10.1.24.1 GigabitEthernet0/0/1
ISIS-L1 15 10 D 10.1.34.1 GigabitEthernet0/0/0
172.16.1.2/32 ISIS-L1 15 10 D 10.1.24.1 GigabitEthernet0/0/1
172.16.1.3/32 ISIS-L1 15 10 D 10.1.34.1 GigabitEthernet0/0/0
To prevent hackers from attacking user devices or networks using MAC addresses, you can configure MAC addresses of untrusted users as blackhole MAC addresses to filter out such invalid MAC addresses. When receiving a packet whose source or destination MAC address is a blackhole MAC address on a device, the device discards the packet.
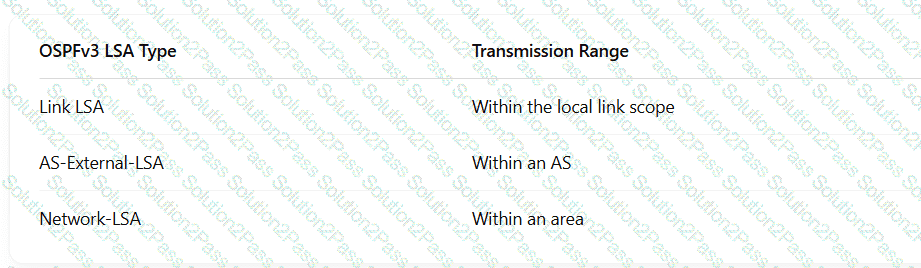
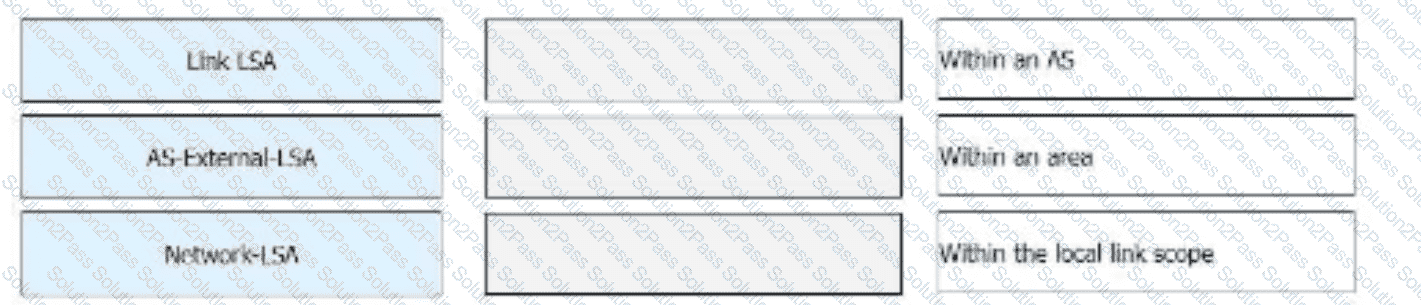
Drag the OSPFv3 LSAs to map them to their corresponding transmission ranges.
The ________ command can be run to completely isolate Layer 2 and Layer 3 of different interfaces in a VLAN. (Use lowercase letters to supplement the command, which cannot be abbreviated.)
A network administrator runs the display telemetry subscription command on a device to check telemetry subscription information. The command output is as follows. Which of the following statements is incorrect?
[~CE] display telemetry subscription
Sub name : Sub1
Sensor group:
Sensor-name Sample-interval(ms) State
Sensor1 1000 RESOLVED
Destination group:
Dest-name Dest-IP Dest-port State Vpn-name Protocol
Dest1 192.168.56.1 20030 RESOLVED - GRPC
Sub state : PASSIVE
Total subscription number is : 1
On traditional campus networks, network admission control (NAC), VLAN, and ACL technologies are used to control users ' network access rights. This results in heavy network O & M workload. Which of the following improvements does the free mobility solution of iMaster NCE-Campus make to traditional campus networks in terms of policy management and control?
OSPF is a mature protocol and is unlikely to have route computation errors in a regular networking environment under correct configurations. Which of the following statements are correct about the possible causes preventing an OSPF neighbor relationship from entering Full state?
Which of the following is the drop probability of packets exceeding the upper threshold in WRED?
In the admission design for large- and medium-sized campus networks, which of the following authentication modes can be used for PCs connected to IP phones?
When you configure a virtualized campus network on iMaster NCE-Campus and enable external networks to connect to the Internet, iMaster NCE-Campus will automatically deliver a specific route to direct traffic to the corresponding external network.
The Ingress VTEP performs both Layer 2 and Layer 3 table lookup for packet forwarding. The forwarding mode is ______ IRB forwarding. (Capitalize the first letter.)
VLAN-based MAC address flapping detection is configured. If MAC address flapping occurs, actions to be taken on an interface can be configured as required. Which of the following actions cannot be configured?
The naming of SRv6 instructions complies with certain rules. You can quickly determine the function of an instruction based on the instruction name. Which of the following statements about the keywords in SRv6 instruction names are correct? (Select all that apply)
Which of the following statements about GRE is incorrect?
Which of the following operations is not involved in the middle phase of a migration?
During telemetry static subscription, the NMS delivers subscription configuration to devices for data sampling. Which of the following statements is incorrect about the sampling path huawei-debug:debug/cpu-infos/cpu-info?
Which of the following is the mapping between VNIs and BDs in VXLAN implementation?