H12-891_V1.0 Huawei HCIE-Datacom V1.0 Free Practice Exam Questions (2026 Updated)
Prepare effectively for your Huawei H12-891_V1.0 HCIE-Datacom V1.0 certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
On a small- or medium-sized campus network deployed based on the Huawei CloudCampus Solution, an AR functioning as the egress gateway supports web-based network management, registration center query, and DHCP Option 148-based deployment, but does not support CLI-based deployment.
For telemetry data push, data can be transferred between devices and collectors using the TLS protocol. TLS must be configured for data encryption if data is pushed based on gRPC.
In the LDP session establishment process, the initiator sends an Initialization message for parameter negotiation. Which message will be sent by the responder if it does not accept negotiation parameters?
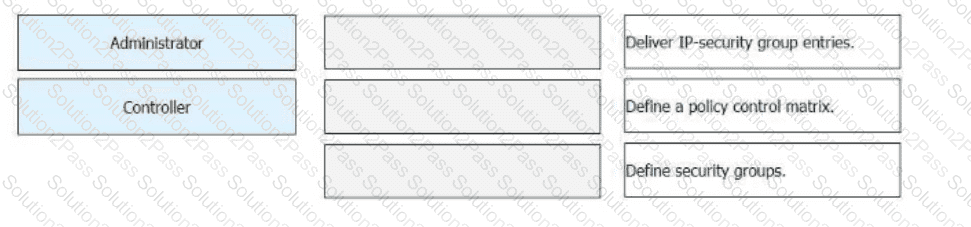
Free mobility is deployed on a campus network through iMaster NCE-Campus. During this deployment, which of the following steps are performed by administrators and which are automatically performed by iMaster NCE-Campus? Drag the administrators and iMaster NCE-Campus icons on the left to the corresponding steps on the right.
NETCONF provides a set of mechanisms for managing network devices. NETCONF operations take place on a configuration datastore of network devices. Which of the following statements is incorrect about the configuration datastore?
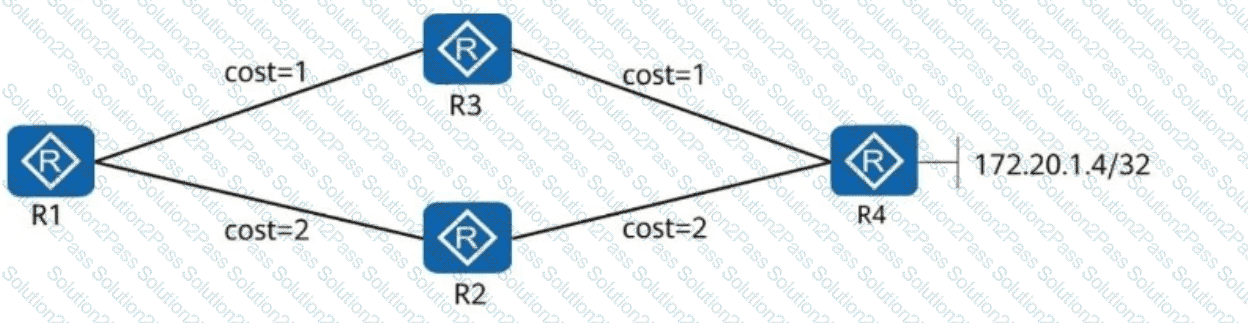
In the following figure, R1, R2, R3, and R4 all belong to OSPF area 0. The link costs are marked in the figure. The Loopback0 addresses of R1, R2, R3, and R4 are advertised to OSPF. R1, R2, and R3, which are R4 clients, use Loopback0 to establish an iBGP peer relationship with R4. The directly connected network segment 172.20.1.4/32 of R4 is advertised to BGP. Which of the following statements are correct about the direction of traffic from R1 to 172.20.1.4/32?
Which of the following statements is correct about the differences between NSR and NSF?
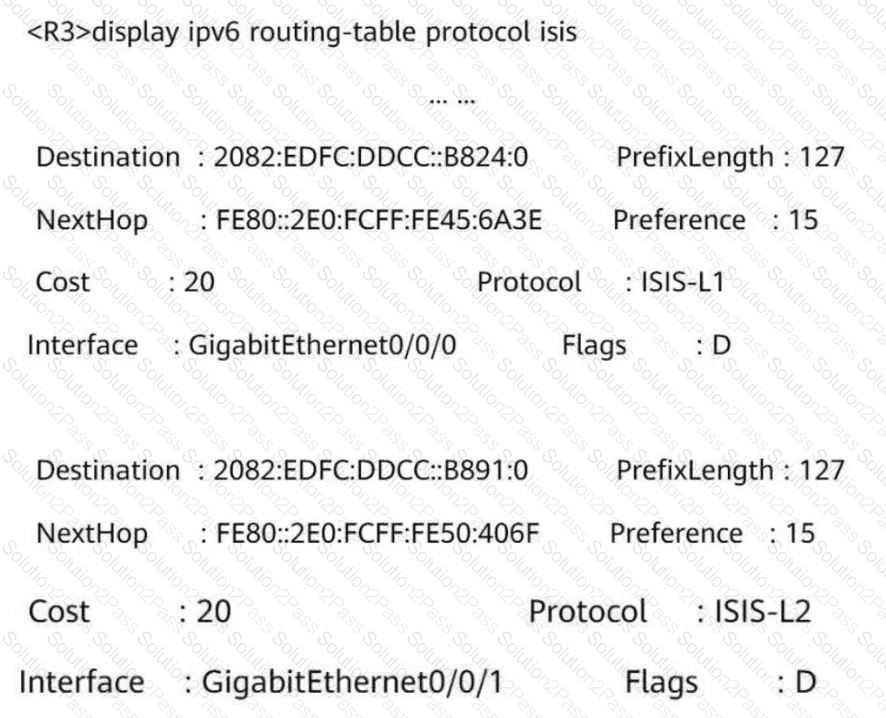
What can be determined from the following figure?
When MPLS/BGP IP VPN is deployed, which of the following statements is incorrect about BGP route exchange between PEs and CEs?
New IS-IS TLVs are used to carry IPv6 addresses and reachability information to support IPv6 route processing and calculation.
As shown in the figure, SW1 and SW2 use asymmetric IRB (Integrated Routing and Bridging) forwarding, and PC1 and PC2 communicate with each other. Which of the following is the destination MAC address of the original data frame in the packet sent from VTEP1 to VTEP2?
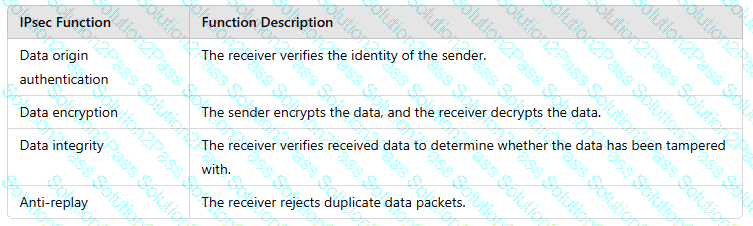
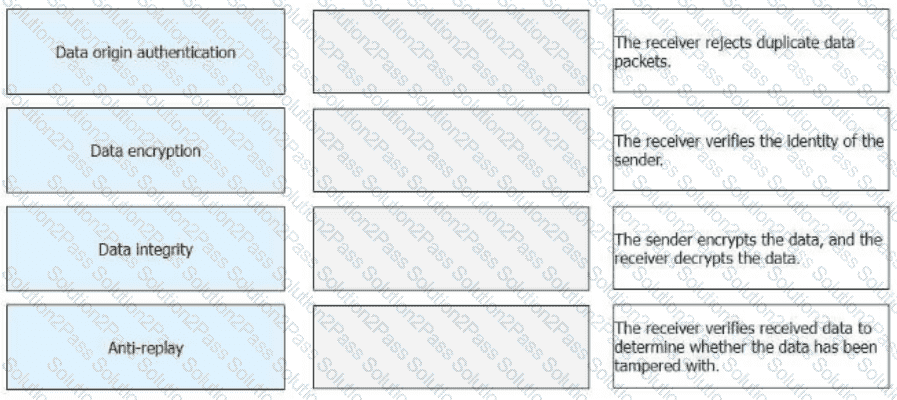
Drag the IPsec functions on the left to the corresponding function description on the right.
Which of the following languages is integrated into the OPS?
In the Huawei SD-WAN Solution, which of the following routing protocols is used to advertise VPN routes between CPEs?
The naming of SRv6 instructions complies with certain rules. You can quickly determine the function of an instruction based on the instruction name. Which of the following statements about the keywords in SRv6 instruction names are correct?
SSH connections are usually established based on TCP/IP connections. In specific cases, SSH connections can be established based on UDP connections.
Which of the following statements are correct about authentication points and policy enforcement points in Huawei ' s free mobility solution?
/ifm/interfaces/interface in Huawei Open Programmability System (OPS) is the URL used to identify a device ' s managed object.
When configuring a static VXLAN tunnel, you need to manually configure the _____, VTEP IP address, and ingress replication list. (Enter only uppercase letters.)
A 32-bit MPLS header consists of a 20-bit label used for packet forwarding, a 3-bit EXP field that identifies the IP packet priority, a 1-bit bottom-of-stack flag that identifies the last label, and an 8-bit TTL field. Which statement regarding the TTL field is correct?