CC ISC CC - Certified in Cybersecurity Free Practice Exam Questions (2026 Updated)
Prepare effectively for your ISC CC CC - Certified in Cybersecurity certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
What is the focus of disaster recovery planning after a data center outage?
What is the first step in incident response planning?
The common term for systems that control temperature and humidity in a data center is:
Faking the sender address of a transmission to gain illegal entry is called:
Example of token-based authentication:
Exhibit.
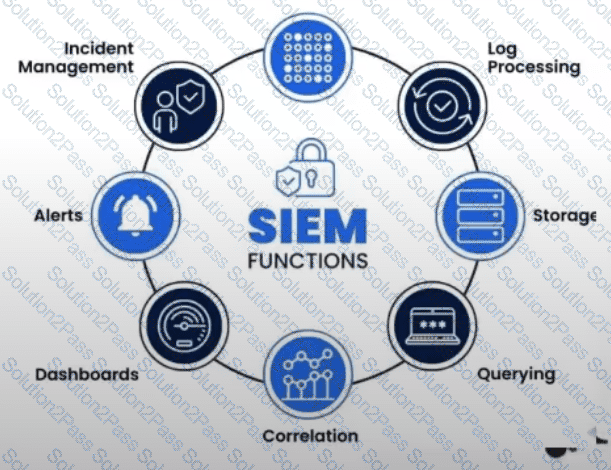
What is the purpose of a Security Information and Event Management (SIEM) system?
How do you distinguish authentication and identification?
Which OSI layer associates MAC addresses with network devices?
Permitting authorized access while preventing improper disclosure.
A structured approach used to oversee and manage risk for an enterprise is called:
Which element of the security policy framework includes recommendations that are NOT binding?
Who should participate in creating a Business Continuity Plan?
Which one of the following cryptographic algorithms does NOT depend upon the prime factorization problem?
What is the difference between a hub and a switch?
Which type of malware encrypts a user’s files and demands payment?
An unusual occurrence in a system or network is best described as:
A system crash results in loss of data. What term best describes this?
Methods or mechanisms used to gain unauthorized access are called:
Which approach involves a continuous cycle of identifying, assessing, prioritizing, and mitigating cybersecurity risks?
A CISO documents a policy establishing acceptable cloud use for all staff. This is an example of:
