CRISC Isaca Certified in Risk and Information Systems Control Free Practice Exam Questions (2025 Updated)
Prepare effectively for your Isaca CRISC Certified in Risk and Information Systems Control certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2025, ensuring you have the most current resources to build confidence and succeed on your first attempt.
It was discovered that a service provider's administrator was accessing sensitive information without the approval of the customer in an Infrastructure as a Service (laaS) model. Which of the following would BEST protect against a future recurrence?
The BEST key performance indicator (KPI) to measure the effectiveness of a backup process would be the number of:
Which of the following is the BEST way to assess the effectiveness of an access management process?
A risk practitioner has been asked to evaluate a new cloud-based service to enhance an organization's access management capabilities. When is the BEST time for the risk practitioner to provide opinions on control strength?
Which of the following BEST protects organizational data within a production cloud environment?
The GREATEST benefit of including low-probability, high-impact events in a risk assessment is the ability to:
A risk practitioner is summarizing the results of a high-profile risk assessment sponsored by senior management. The BEST way to support risk-based decisions by senior management would be to:
Which of the following will provide the BEST measure of compliance with IT policies?
The PRIMARY benefit of selecting an appropriate set of key risk indicators (KRIs) is that they:
Which of the following is a business asset for an organization that runs only in a Software as a Service (SaaS) cloud computing environment?
Which of the following trends would cause the GREATEST concern regarding the effectiveness of an organization's user access control processes? An increase in the:
Which of the following provides the MOST insight into an organization's IT threat exposure?
Which of the following is a specific concern related to machine learning algorithms?
A business unit has implemented robotic process automation (RPA) for its
repetitive back-office tasks. Which of the following should be the risk
practitioner's GREATEST concern?
Which of the following is the BEST approach when a risk treatment plan cannot be completed on time?
Which of the following will BEST help to ensure the continued effectiveness of the IT risk management function within an organization experiencing high employee turnover?
Which of the following is MOST important when identifying an organization's risk exposure associated with Internet of Things (loT) devices?
Which of the following is the MOST significant benefit of using quantitative risk analysis instead of qualitative risk analysis?
Which of the following BEST reduces the likelihood of employees unintentionally disclosing sensitive information to outside parties?
An organization recently implemented an automated interface for uploading payment files to its banking system to replace manual processing. Which of the following elements of the risk register is MOST appropriate for the risk practitioner to update to reflect the improved control?
Which of the following is the GREATEST benefit of using IT risk scenarios?
Which of the following BEST mitigates the risk associated with inadvertent data leakage by users who work remotely?
Which of the following is the MOST important driver of an effective enterprise risk management (ERM) program?
Continuous monitoring of key risk indicators (KRIs) will:
After undertaking a risk assessment of a production system, the MOST appropriate action is fcr the risk manager to
An organization is increasingly concerned about loss of sensitive data and asks the risk practitioner to assess the current risk level. Which of the following should the risk practitioner do FIRST?
What should be the PRIMARY objective of updating a risk awareness program in response to a steady rise in cybersecurity threats across the industry?
Which of the following would be the BEST way to help ensure the effectiveness of a data loss prevention (DLP) control that has been implemented to prevent the loss of credit card data?
A department has been granted an exception to bypass the existing approval process for purchase orders. The risk practitioner should verify the exception has been approved by which of the following?
Which of the following is MOST important when developing key risk indicators (KRIs)?
Which of the following is the ULTIMATE objective of utilizing key control indicators (KCIs) in the risk management process?
Which of the following is the FIRST step in risk assessment?
An IT operations team implements disaster recovery controls based on decisions from application owners regarding the level of resiliency needed. Who is the risk owner in this scenario?
Which of the following describes the relationship between risk appetite and risk tolerance?
Which of the following key risk indicators (KRIs) provides the BEST insight into the risk associated with IT systems being unable to meet the required availability service level in the future?
When defining thresholds for control key performance indicators (KPIs). it is MOST helpful to align:
Which of the following will BEST support management reporting on risk?
An organization has established workflows in its service desk to support employee reports of security-related concerns. Which of the following is the MOST efficient approach to analyze these concerns?
Deviation from a mitigation action plan's completion date should be determined by which of the following?
Which of the following is the MOST important responsibility of a risk owner?
Which of the following controls would BEST reduce the likelihood of a successful network attack through social engineering?
A poster has been displayed in a data center that reads. "Anyone caught taking photographs in the data center may be subject to disciplinary action." Which of the following control types has been implemented?
A global organization is considering the transfer of its customer information systems to an overseas cloud service provider in the event of a disaster. Which of the following should be the MOST important risk consideration?
A business is conducting a proof of concept on a vendor’s AI technology. Which of the following is the MOST important consideration for managing risk?
Which of the following is the FIRST step in managing the security risk associated with wearable technology in the workplace?
Which of the following is the BEST way to support communication of emerging risk?
Who is ULTIMATELY accountable for risk treatment?
A multinational company needs to implement a new centralized security system. The risk practitioner has identified a conflict between the organization's data-handling policy and local privacy regulations. Which of the following would be the BEST recommendation?
When of the following standard operating procedure (SOP) statements BEST illustrates appropriate risk register maintenance?
Which of the following is the MOST important objective of regularly presenting the project risk register to the project steering committee?
Which of the following is the MOST important topic to cover in a risk awareness training program for all staff?
Who is MOST important lo include in the assessment of existing IT risk scenarios?
Which of the following provides the MOST useful information for developing key risk indicators (KRIs)?
Management has noticed storage costs have increased exponentially over the last 10 years because most users do not delete their emails. Which of the following can BEST alleviate this issue while not sacrificing security?
A risk heat map is MOST commonly used as part of an IT risk analysis to facilitate risk:
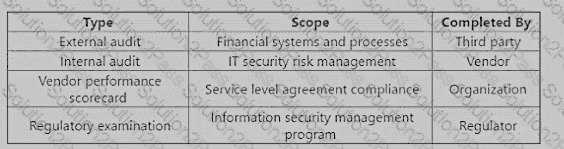
After a high-profile systems breach at an organization s key vendor, the vendor has implemented additional mitigating controls. The vendor has voluntarily shared the following set of assessments:
Which of the assessments provides the MOST reliable input to evaluate residual risk in the vendor's control environment?
Which of the following BEST enables the timely detection of changes in the security control environment?
Which of the following provides the MOST useful information to trace the impact of aggregated risk across an organization's technical environment?
The PRIMARY purpose of vulnerability assessments is to:
Which of the following is the BEST course of action when risk is found to be above the acceptable risk appetite?
