JN0-650 Juniper Enterprise Routing and Switching - Professional (JNCIP-ENT) Free Practice Exam Questions (2026 Updated)
Prepare effectively for your Juniper JN0-650 Enterprise Routing and Switching - Professional (JNCIP-ENT) certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
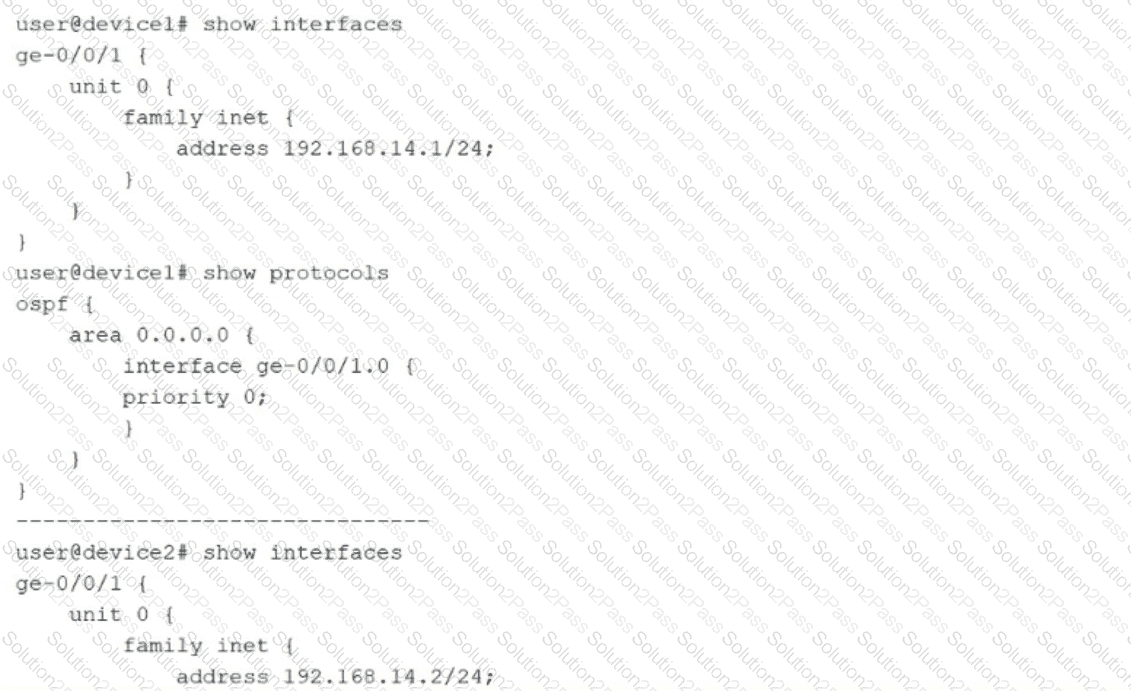
Exhibit.
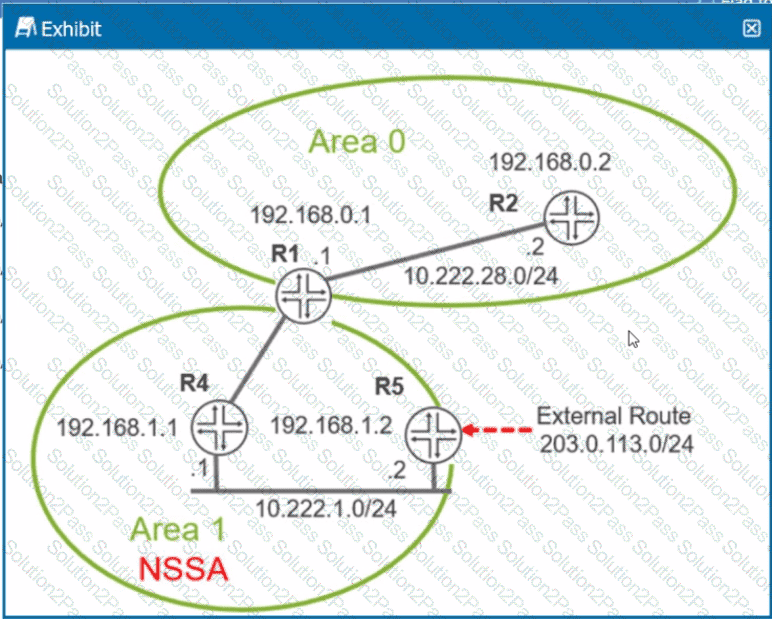
Referring to the exhibit, which two statements are correct? (Choose two.)
Exhibit
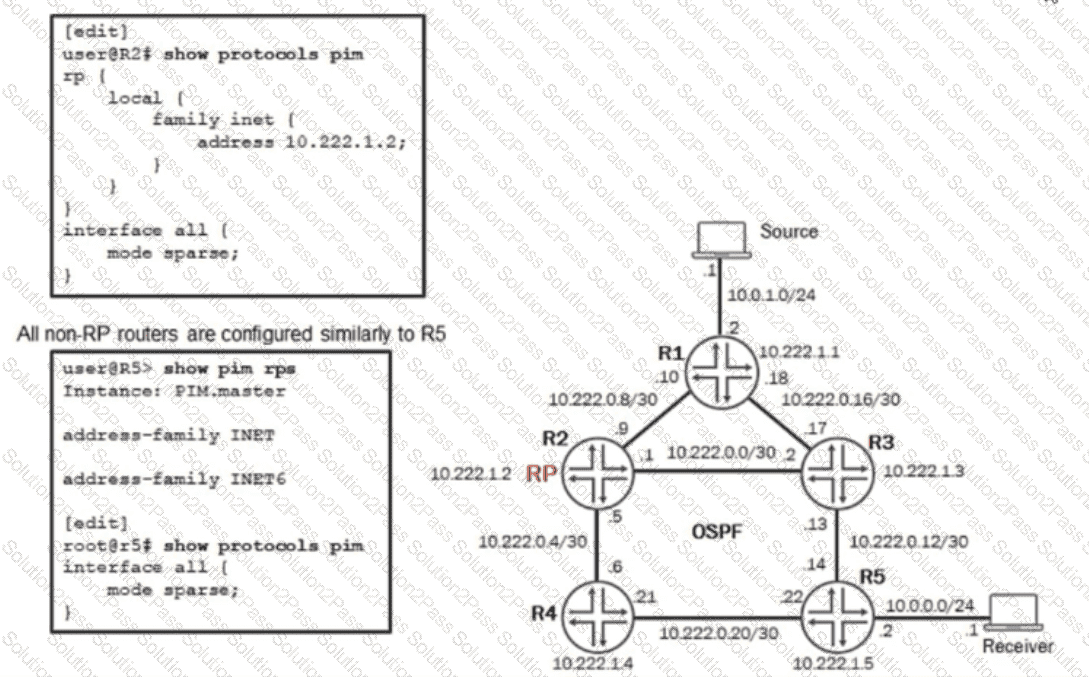
You need to configure the non-RP routers in your network to dynamically learn the location of the RP using standard protocols only. You have already applied the configuration shown in the exhibit, but the routers have not learned the location of the RP.
Which additional step must you take to fulfill these requirements?
You want to validate a recursive lookup for an EVPN route designation. Which route table query will accomplish this task?
You must implement EVPN signaling on an EX Series device that is configured with both underlay and overlay networks. Which network protocol accomplishes this task?
Which two statements are correct about multicast routing tables? (Choose two.)
Your Layer 2 network uses 802.1X to authenticate user devices connecting to the network. You are asked to include a new Layer 2 interface connection from the conference room in your network. You must ensure that only a single device is allowed to authenticate on this port at one time to avoid users from being able to plug in a rogue switch to this port.
In this scenario, which 802.1X method would you use for the new interface?
Which statement about LLDP and LLDP-MED operations on EX Series devices is correct?
Exhibit.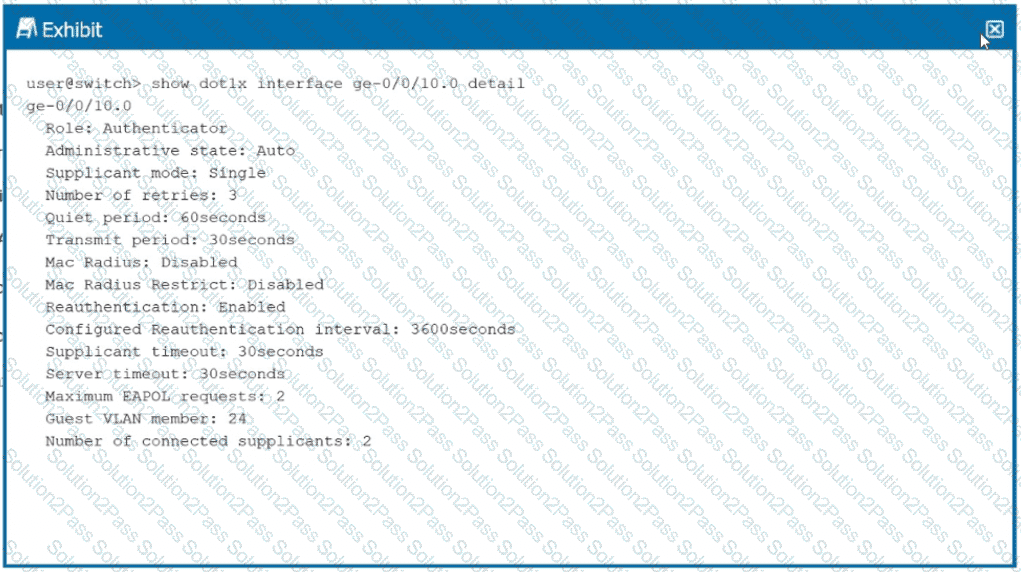
You want to limit port access to only one device at a time.
Referring to the exhibit, which configuration change will accomplish this task?
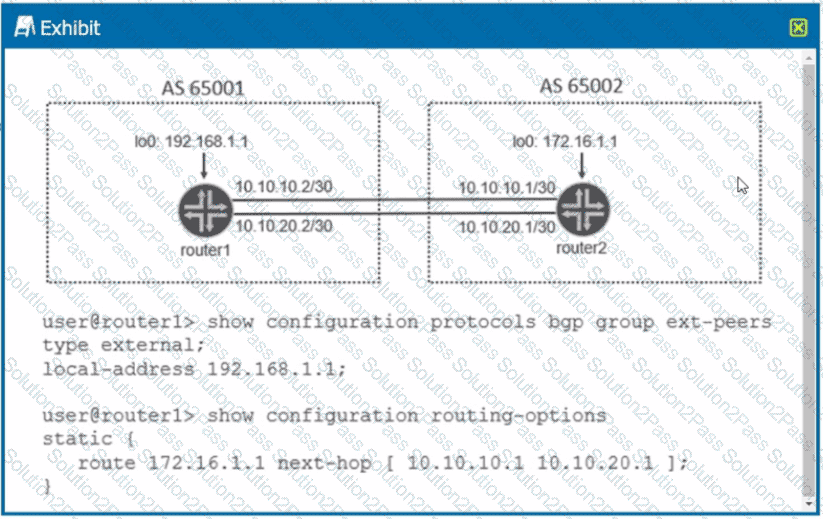
Exhibit
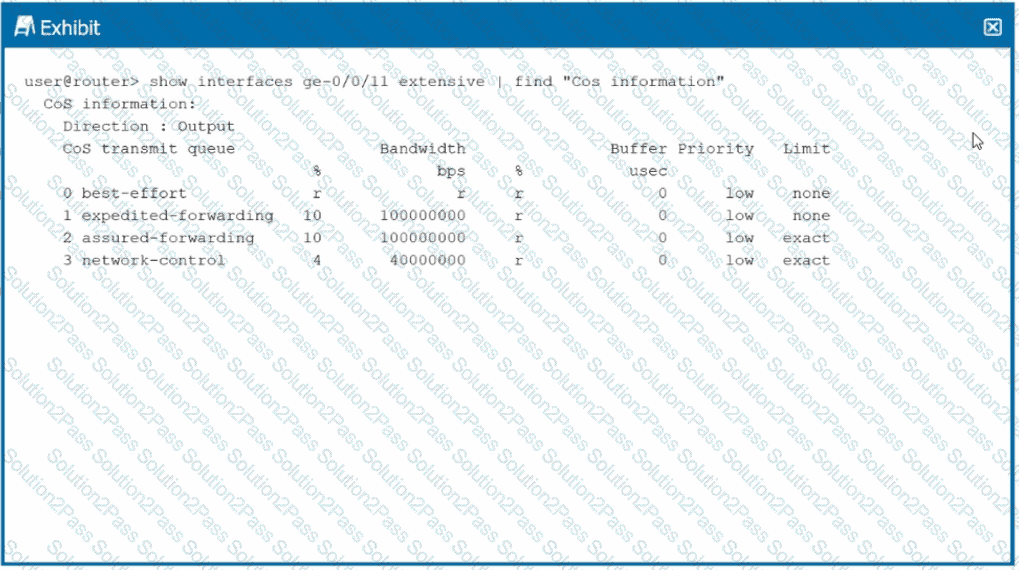
Referring to the exhibit, which two statements are correct? (Choose two.)
Exhibit.
Referring to the exhibit, which statement is correct?
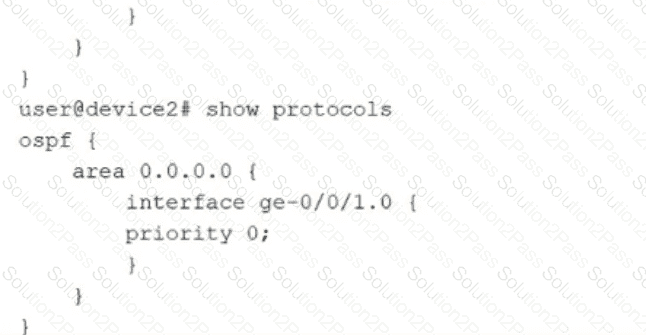
Exhibit.
Referring to the exhibit, what is required for the BGP peering to establish?
When configuring OSPF. what is the purpose of adding the secondary command to an OSPF interface?
According to IETF standards, which two statements are correct about EVPN/VXLAN deployments? (Choose two.)
Exhibit
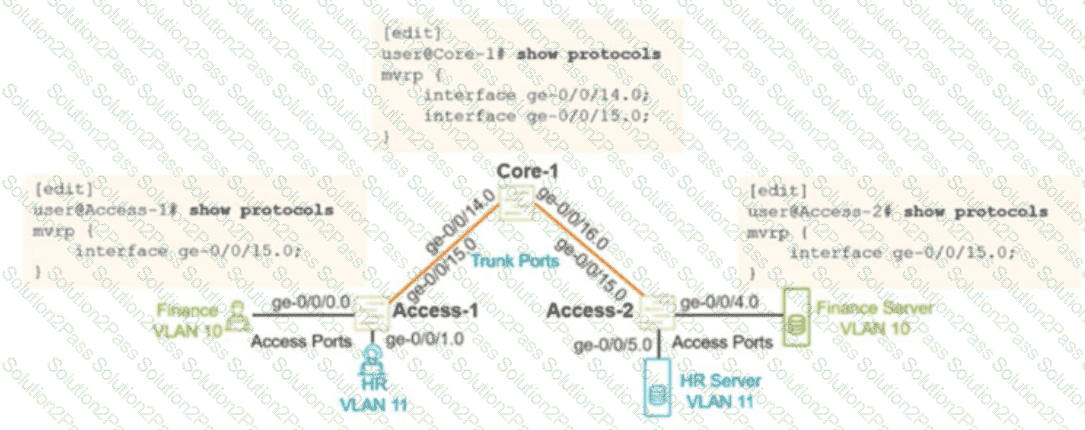
You configured MVRP in your Layer 2 network using the configuration shown in the exhibit. You verified that the appropnate VLANs are configured and applied on the two access switches. You are using RSTP as your loop prevention mechanism. Unfortunately, the users are not able to communicate with their corresponding server attached to the Access-2 switch.
In this scenario, what should you do to solve this problem?
Click the Exhibit button.
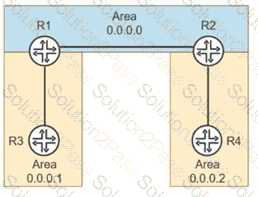
You are troubleshooting suboptimal routing in an enterprise OSPFv2 deployment:
-- R1 is an ABR between Area 0 and Area 1.
-- R2 is an ABR between Area 0 and Area 2.
-- R3 in Area 1 advertises a network that should be reachable by routers in Area 2.
-- The ABRs are connected in the backbone (Area 0).
On router R2, the show ospf database does not display router LSAs or network LSAs from Area 1, but an interarea route to R3’s network exists in the routing table. R2 does not have Type-1 or Type-2 LSAs from Area 1 in its OSPF database.
Referring to the exhibit, which statement is correct?
Which two statements correctly describe how EX Series switches use captive portal for Layer 2 authentication? (Choose two.)
You have created a private community VLAN called RND The private community VLAN works fine within switch S1, but traffic in the private RND community VLAN does not reach VLAN members connected to switch S2.
Which statement is correct in this scenario?
You are asked to establish authentication for users connecting to the corporate network. You must ensure that only corporate devices that are identified by MAC addresses are allowed to authenticate and connect Authentication must be handled by a centralized database.
Which authentication method would you implement in this scenario?
What causes IBGP route flapping in enterprise networks?
Your existing enterprise network uses OSPFv3 on Juniper devices. You need to extend the networking into a new building, and it needs to be in its own OSPF area. Your team is debating about making the area a stub
Which two statements are correct in this scenario? (Choose two.)
