SC-200 Microsoft Security Operations Analyst Free Practice Exam Questions (2026 Updated)
Prepare effectively for your Microsoft SC-200 Microsoft Security Operations Analyst certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
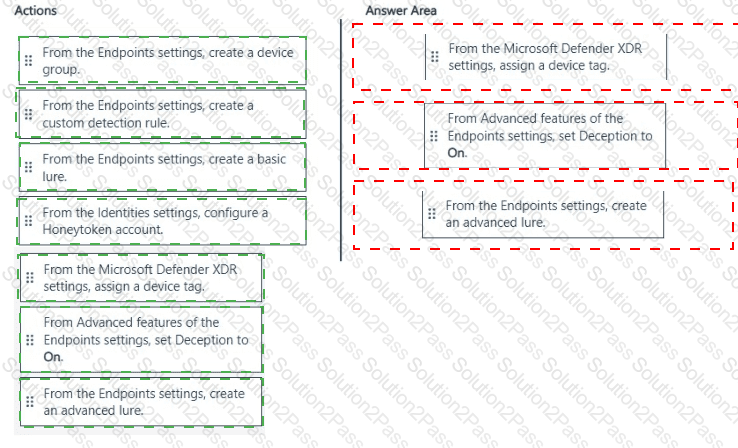
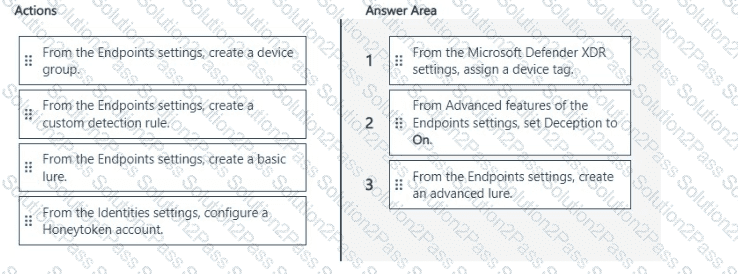
You have a Microsoft 365 subscription. The subscription contains 500 Windows 11 devices that are onboarded to Microsoft Defender for Endpoint.
You need to perform the following actions in Microsoft Defender XDR:
• For your company ' s finance department, populate random endpoints with fake cached credentials.
• Ensure That an incident is created in Microsoft Defender XDR if an attacker attempts to use the fake cached credentials.
The solution must ensure that the fake cached credentials are planted only on endpoints of the finance department.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
NOTE: More than one order of answer choices is correct. You will receive credit for any of the correct orders you select.

You have a Microsoft Sentinel workspace.
You need to prevent a built-in Advance Security information Model (ASIM) parse from being updated automatically.
What are two ways to achieve this goal? Each correct answer presents a complete solution.
NOTE: Each correct selection is worth one point.
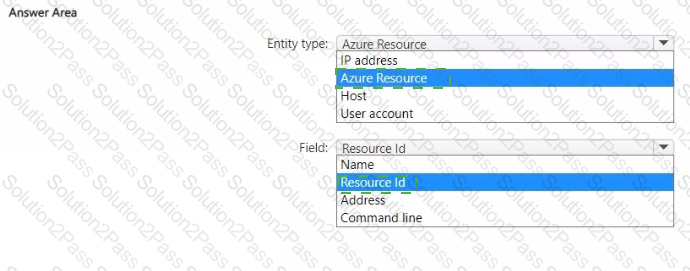
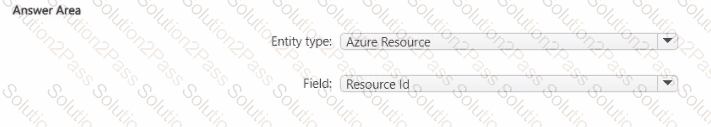
You have an Azure Storage account that will be accessed by multiple Azure Functions apps during the development of an application.
You need to hide Microsoft Defender for Cloud alerts for the storage account.
Which entity type and field should you use in a suppression rule? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.

You need to correlate data from the SecurityEvent Log Anarytks table to meet the Microsoft Sentinel requirements for using UEBA. Which Log Analytics table should you use?
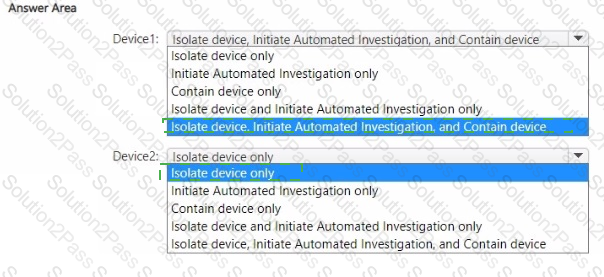
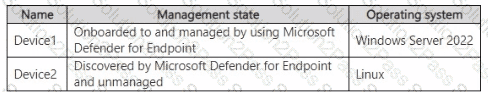
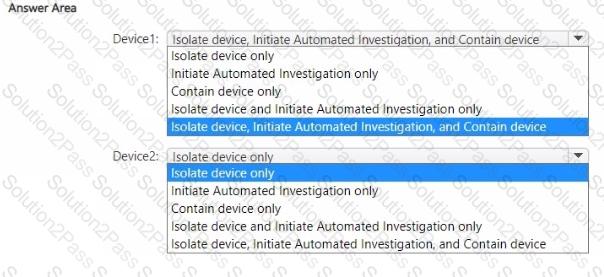
You have a Microsoft 365 E5 subscription that uses Microsoft Defender for Endpoint.
You have the on-premises devices shown in the following table.
You are preparing an incident response plan for devices infected by malware. You need to recommend response actions that meet the following requirements:
• Block malware from communicating with and infecting managed devices.
• Do NOT affect the ability to control managed devices.
Which actions should you use for each device? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
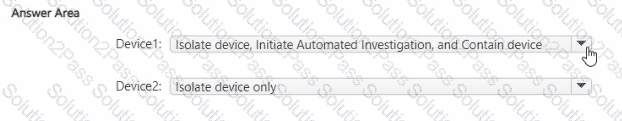
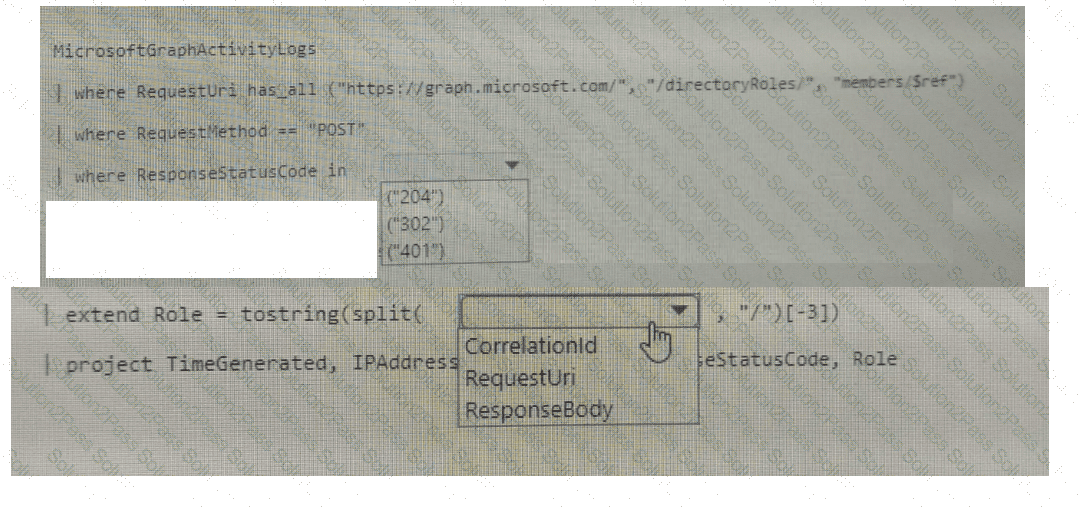
You have a Microsoft 365 E5 subscription that is linked to a Microsoft Entra tenant named contoso.com.
You need to query Microsoft Graph activity logs to identify changes to the roles in contoso.com.
How should you complete the KQL query? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Your company deploys the following services:
Microsoft Defender for Identity
Microsoft Defender for Endpoint
Microsoft Defender for Office 365
You need to provide a security analyst with the ability to use the Microsoft 365 security center. The analyst must be able to approve and reject pending actions generated by Microsoft Defender for Endpoint. The solution must use the principle of least privilege.
Which two roles should assign to the analyst? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point .
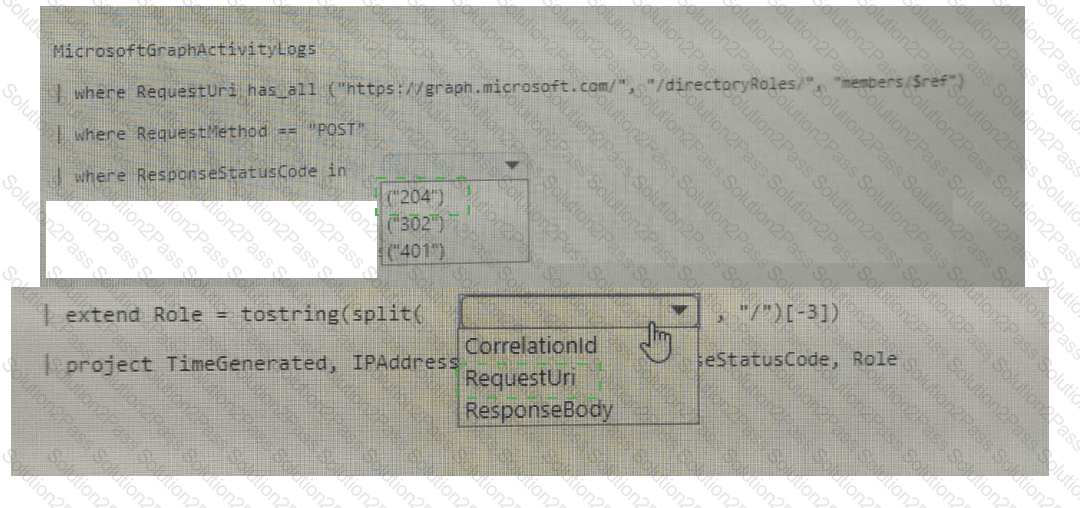
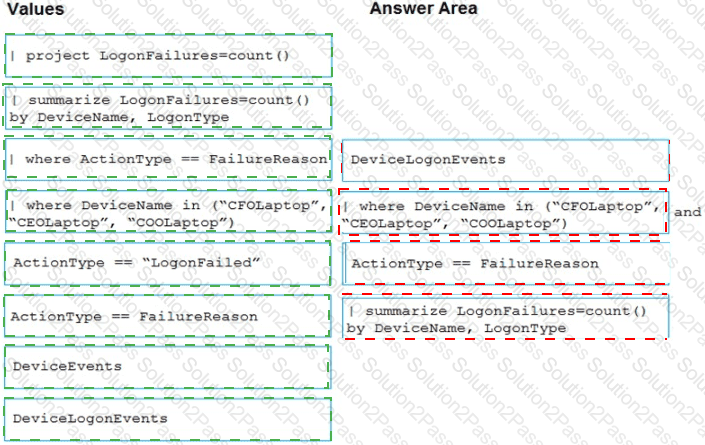
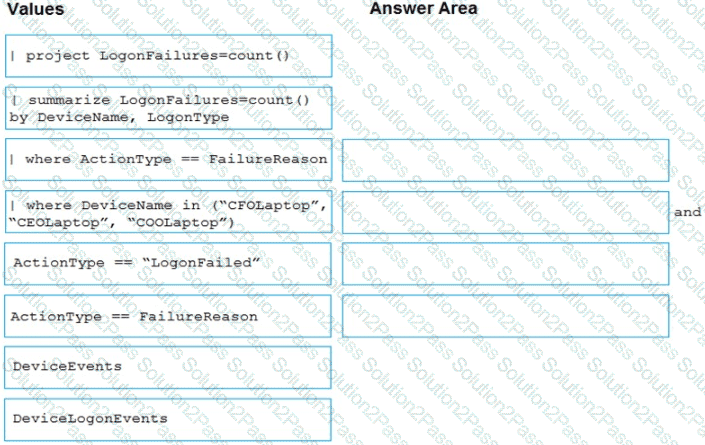
You are investigating an incident by using Microsoft 365 Defender.
You need to create an advanced hunting query to count failed sign-in authentications on three devices named CFOLaptop. CEOLaptop, and COOLaptop.
How should you complete the query? To answer, select the appropriate options in the answer area.
NOTE Each correct selection is worth one point
You use Azure Sentinel.
You need to use a built-in role to provide a security analyst with the ability to edit the queries of custom Azure Sentinel workbooks. The solution must use the principle of least privilege.
Which role should you assign to the analyst?
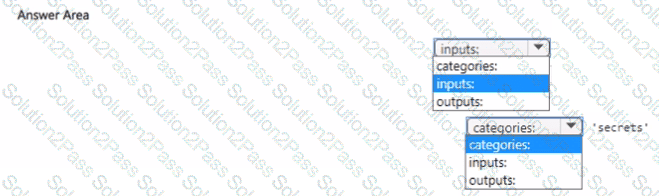
You have an Azure subscription named Sub1 and an Azure DevOps organization named AzDO1. AzDO1 uses Defender for Cloud and contains a project that has a YAML pipeline named Pipeline1.
Pipeline1 outputs the details of discovered open source software vulnerabilities to Defender for Cloud.
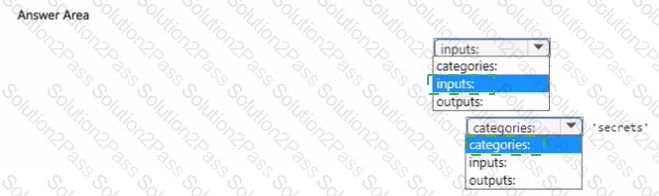
You need to configure Pipeline1 to output the results of secret scanning to Defender for Cloud,
What should you add to Pipeline1? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have a Microsoft 365 subscription that uses Microsoft Defender XDR.
You discover that when Microsoft Defender for Endpoint generates alerts for a commonly used executable file, it causes alert fatigue. You need to tune the alerts.
Which two actions can an alert tuning rule perform for the alerts?
Each correct answer presents a complete solution.
NOTE: Each correct selection is worth one point.
You have a custom Microsoft Sentinel workbook named Workbooks.
You need to add a grid to Workbook1. The solution must ensure that the grid contains a maximum of 100 rows.
What should you do?
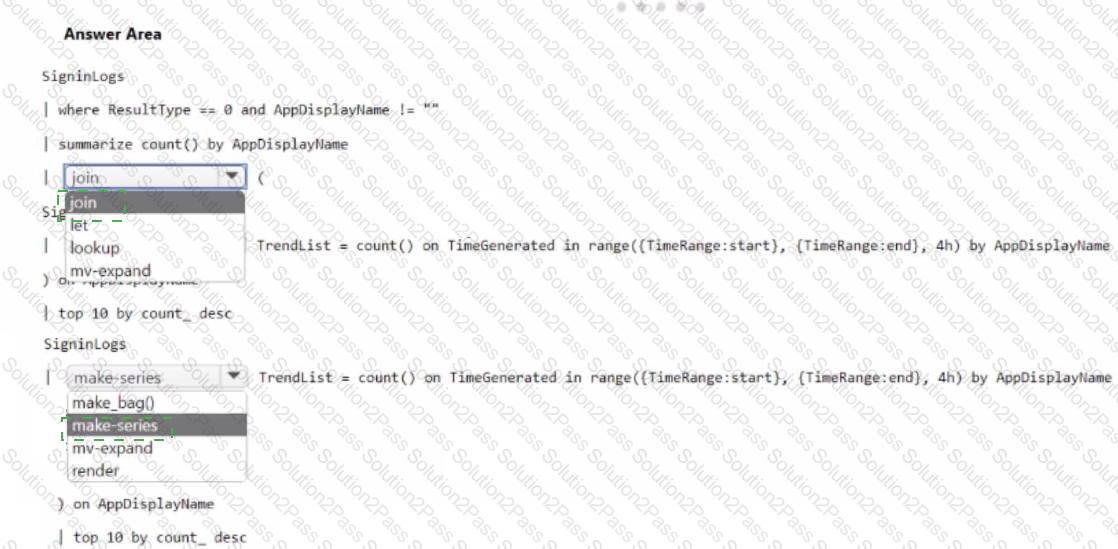
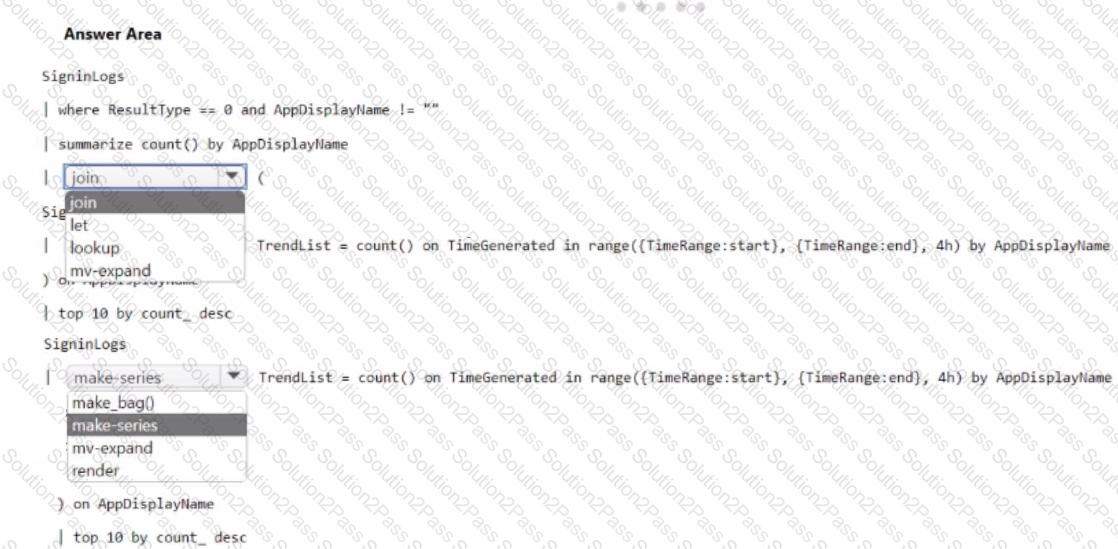
You have a Microsoft Sentinel workspace.
You need to configure a report visual for a custom workbook. The solution must meet the following requirements:
• The count and usage trend of AppDisplayName must be included
• The TrendList column must be useable in a sparkline visual,
How should you complete the KQL query? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have an Azure subscription that uses Microsoft Sentinel.
You detect a new threat by using a hunting query.
You need to ensure that Microsoft Sentinel automatically detects the threat. The solution must minimize administrative effort.
What should you do?
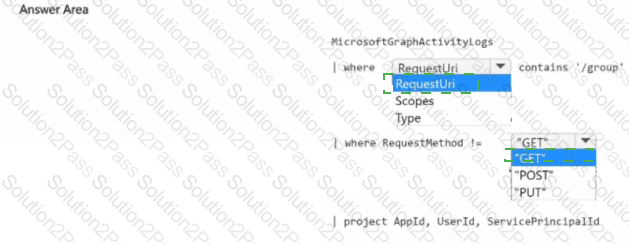
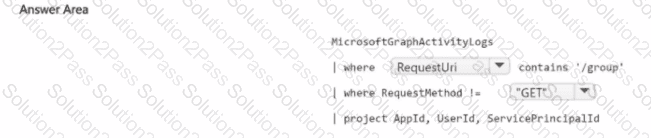
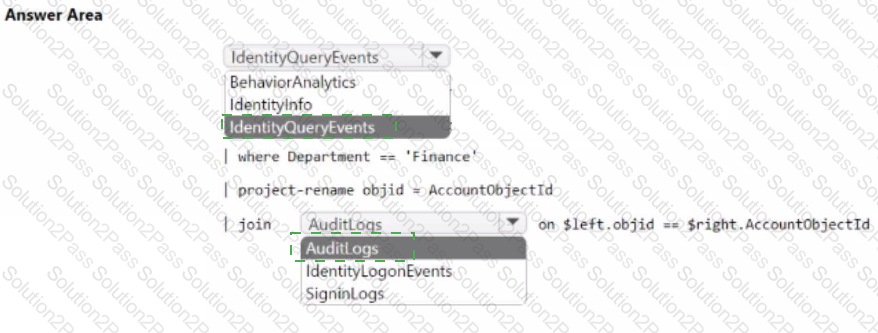
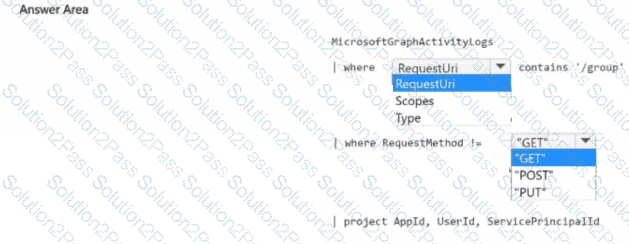
You have a Microsoft 365 subscription
You need to identify all the security principals that submitted requests to change or delete groups. How should you complete the KQL query? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
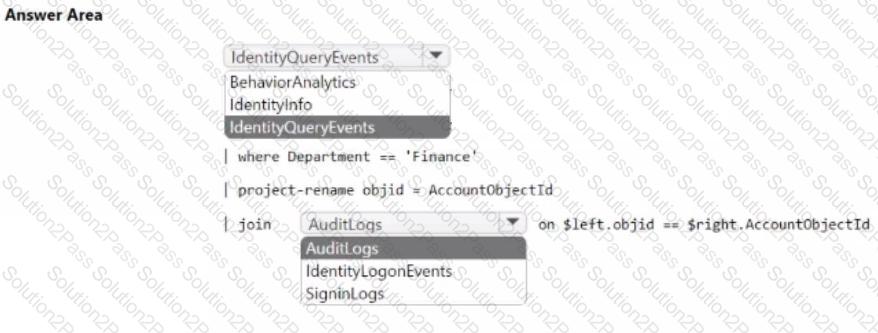
Your network contains an on-premises Active Directory Domain Services (AD DS) domain that syncs with Azure AD.
You have a Microsoft 365 E5 subscription that uses Microsoft Defender 365.
You need to identify all the interactive authentication attempts by the users in the finance department of your company.
How should you complete the KQL query? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have an Azure subscription that contains a virtual machine named VM1 and use s Azure Defender. Azure Defender has automatic provisioning enabled.
You need to create a custom alert suppression rule that will supress false positive alerts for suspicious use of PowerShell on VM1.
What should you do first?
You have an Azure subscription that has Azure Defender enabled for all supported resource types.
You need to configure the continuous export of high-severity alerts to enable their retrieval from a third-party security information and event management (SIEM) solution.
To which service should you export the alerts?
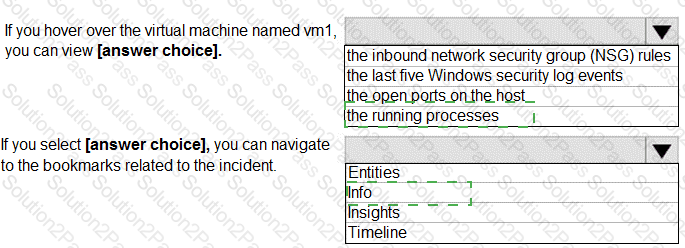
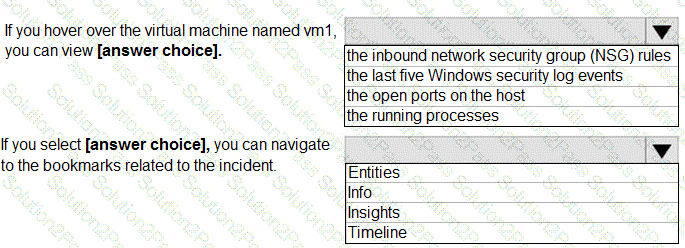
From Azure Sentinel, you open the Investigation pane for a high-severity incident as shown in the following exhibit.
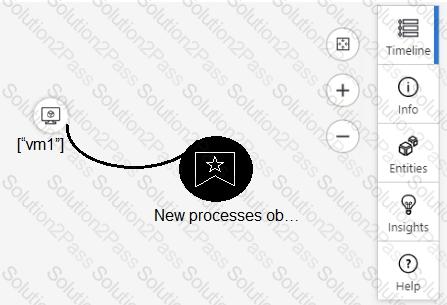
Use the drop-down menus to select the answer choice that complet es each statement based on the information presented in the graphic.
NOTE: Each correct selection is worth one point.
You use Azure Defender.
You have an Azure Storage account that contains sensitive information.
You need to run a PowerShell script if someone accesses the storage account fr om a suspicious IP address.
Which two actions should you perform? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.