ISO-IEC-27001-Lead-Auditor PECB Certified ISO/IEC 27001 2022 Lead Auditor exam Free Practice Exam Questions (2026 Updated)
Prepare effectively for your PECB ISO-IEC-27001-Lead-Auditor PECB Certified ISO/IEC 27001 2022 Lead Auditor exam certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
Total 418 questions
You received an email requiring you to send information such as name, email, and password in order to continue using your email account. If you do not send such
information, your email account will be disabled. What does this scenario present?
After completing Stage 1 and in preparation for a Stage 2 initial certification audit, the auditee informs the audit team leader that they wish to extend the audit scope to include two additional sites that have recently been acquired by the organisation.
Considering this information, what action would you expect the audit team leader to take?
In the context of a third-party certification audit, confidentiality is an issue in an audit programme. Select two options which correctly state the function of confidentiality in an audit
You are an ISMS audit team leader tasked with conducting a follow-up audit at a client's data centre. Following two days on-site you conclude that of the original 12 minor and 1 major nonconformities that prompted the follow-up audit, only 1 minor nonconformity still remains outstanding.
Select four options for the actions you could take.
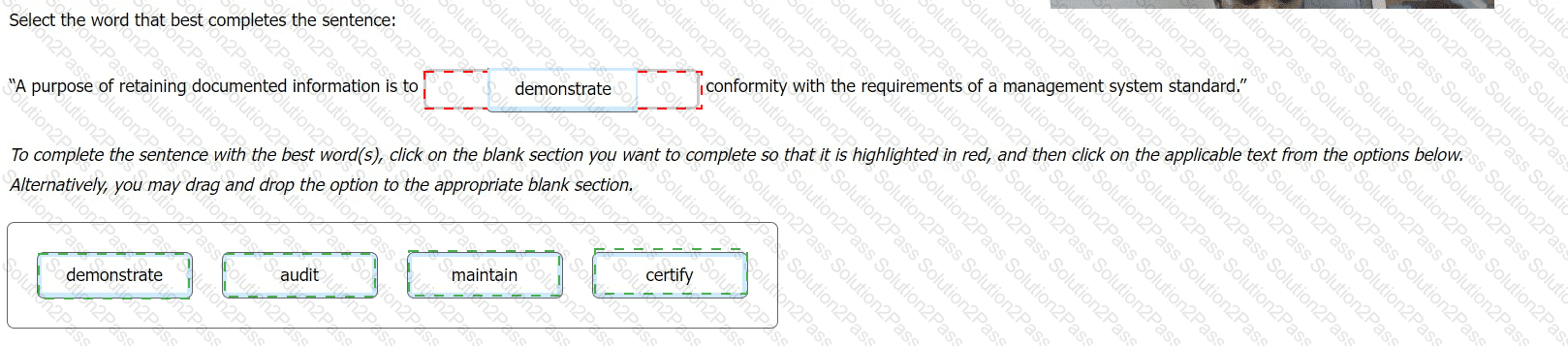
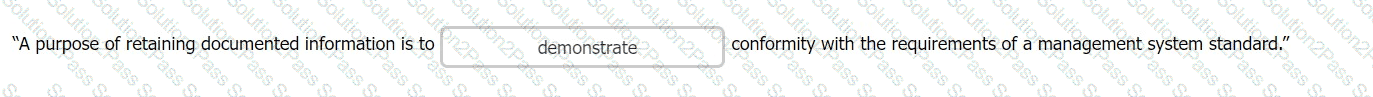
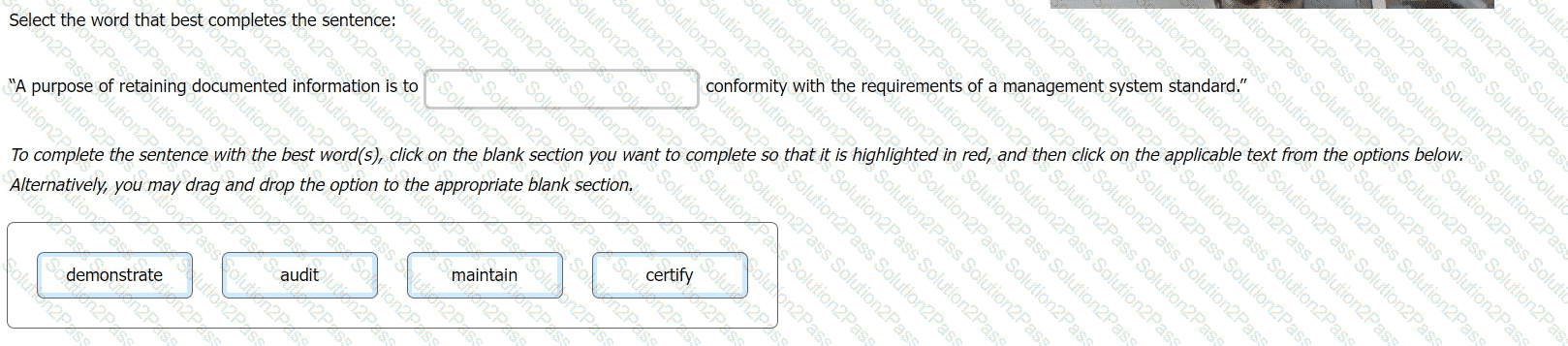
Select the word that best completes the sentence:
You are conducting a third-party surveillance audit when another member of the audit team approaches you seeking clarification. They have been asked to assess the organisation's application of control 5.7 - Threat Intelligence. They are aware that this is one of the new controls introduced in the 2022 edition of ISO/IEC 27001, and they want to make sure they audit the control correctly.
They have prepared a checklist to assist them with their audit and want you to confirm that their planned activities are aligned with the control's requirements.
Which three of the following options represent valid audit trails?
Which one of the following options best describes the purpose of a Stage 2 audit?
Question:
An organization is evaluating the materiality of different processes within its ISMS. It is assessing the direct expenses involved with personnel, third-party services, and general fees. Which factor of materiality is the company primarily considering?
You are carrying out your first third-party ISMS surveillance audit as an audit team leader. You are presently in the auditee's data centre with another member of your audit team and the organisation's guide.
You request access to a locked room protected by a combination lock and iris scanner. The room contains several rows of uninterruptable power supplies along with several data cabinets containing client-supplied
equipment, predominantly servers, and switches.
You note that there is a gas-based fire extinguishing system in place. A label indicates that the system requires testing every 6 months however the most recent test recorded on the label was carried out by the
manufacturer 12 months ago.
Based on the scenario above which two of the following actions would you now take?
Question
Which of the following is NOT a required element in the documentation template for quality review?
Scenario 2
Knight is an electronics company based in Northern California, the US that develops video game consoles. With over 300 employees globally, Knight is celebrating its fifth anniversary by launching the G-Console, a next-generation gaming system aimed at international markets. G-Console is considered to be the ultimate media machine of 2021, and it will give players the best gaming experience. The console pack will include a pair of VR headsets, two games, and other gifts.
Over the years, the company has developed a strong reputation for integrity, honesty, and respect toward their customers. Besides being a very customer-oriented company, Knight also gained wide recognition within the gaming industry because of its quality.
As one of the leading video game console developers in the world, Knight often finds itself a target for malicious activities. Therefore, it has implemented an information security management system (ISMS) based on ISO/IEC 27001, and its scope was communicated to employees of the company over a weekly meeting.
Recently, however, Knight experienced a security breach when hackers leaked proprietary information. In response, the incident response team (IRT) immediately began a thorough investigation of the system and the specifics of the incident. Initially, the IRT suspected that employees may have used weak passwords, allowing hackers to easily access their accounts. Upon further investigation, it was revealed that the hackers captured traffic from the file transfer protocol (FTP), which transmits data using clear-text passwords for authentication.
In light of this security incident, and following the IRT’s recommendations, Knight decided to replace the FTP with Secure Shell (SSH) protocol. This change ensures that any captured traffic is encrypted, significantly improving security.
After implementing these changes, Knight conducted a risk assessment to verify that the implementation of controls had minimized the risk of similar incidents. Based on the results of the risk assessment, they chose a risk treatment option to treat the risk.
Question
What does the IRT’s findings about FTP represent in terms of information security?
Scenario 4: Branding is a marketing company that works with some of the most famous companies in the US. To reduce internal costs. Branding has outsourced the software development and IT helpdesk operations to Techvology for over two years. Techvology. equipped with the necessary expertise, manages Branding's software, network, and hardware needs. Branding has implemented an information security management system (ISMS) and is certified against ISO/IEC 27001, demonstrating its commitment to maintaining high standards of information security. It actively conducts audits on Techvology to ensure that the security of its outsourced operations complies with ISO/IEC 27001 certification requirements.
During the last audit. Branding's audit team defined the processes to be audited and the audit schedule. They adopted an evidence based approach, particularly in light of two information security incidents reported by Techvology in the past year The focus was on evaluating how these incidents were addressed and ensuring compliance with the terms of the outsourcing agreement
The audit began with a comprehensive review of Techvology's methods for monitoring the quality of outsourced operations, assessing whether the services provided met Branding's expectations and agreed-upon standards The auditors also verified whether Techvology complied with the contractual requirements established between the two entities This involved thoroughly examining the terms and conditions in the outsourcing agreement to guarantee that all aspects, including information security measures, are being adhered to.
Furthermore, the audit included a critical evaluation of the governance processes Techvology uses to manage its outsourced operations and other organizations. This step is crucial for Branding to verify that proper controls and oversight mechanisms are in place to mitigate potential risks associated with the outsourcing arrangement.
The auditors conducted interviews with various levels of Techvology's personnel and analyzed the incident resolution records. In addition, Techvology provided the records that served as evidence that they conducted awareness sessions for the staff regarding incident management. Based on the information gathered, they predicted that both information security incidents were caused by incompetent personnel. Therefore, auditors requested to see the personnel files of the employees involved in the incidents to review evidence of their competence, such as relevant experience, certificates, and records of attended trainings.
Branding's auditors performed a critical evaluation of the validity of the evidence obtained and remained alert for evidence that could contradict or question the reliability of the documented information received. During the audit at Techvology, the auditors upheld this approach by critically assessing the incident resolution records and conducting thorough interviews with employees at different levels and functions. They did not merely take the word of Techvology's representatives for facts; instead, they sought concrete evidence to support the representatives' claims about the incident management processes.
Based on the scenario above, answer the following question:
Question:
Which auditing principle is explained in the last paragraph of Scenario 4?
Scenario 7: Webvue. headquartered in Japan, is a technology company specializing in the development, support, and maintenance of computer software. Webvue provides solutions across various technology fields and business sectors. Its flagship service is CloudWebvue, a comprehensive cloud computing platform offering storage, networking, and virtual computing services. Designed for both businesses and individual users. CloudWebvue is known for its flexibility, scalability, and reliability.
Webvue has decided to only include CloudWebvue in its ISO/IEC 27001 certification scope. Thus, the stage 1 and 2 audits were performed simultaneously Webvue takes pride in its strictness regarding asset confidentiality They protect the information stored in CloudWebvue by using appropriate cryptographic controls. Every piece of information of any classification level, whether for internal use. restricted, or confidential, is first encrypted with a unique corresponding hash and then stored in the cloud
The audit team comprised five persons Keith. Sean. Layla, Sam. and Tina. Keith, the most experienced auditor on the IT and information security auditing team, was the audit team leader. His responsibilities included planning the audit and managing the audit team. Sean and Layla were experienced in project planning, business analysis, and IT systems (hardware and application) Their tasks included audit planning according to Webvue’s internal systems and processes Sam and Tina, on the other hand, who had recently completed their education, were responsible for completing the day-to-day tasks while developing their audit skills
While verifying conformity to control 8.24 Use of cryptography of ISO/IEC 27001 Annex A through interviews with the relevant staff, the audit team found out that the cryptographic keys have been initially generated based on random bit generator (RBG) and other best practices for the generation of the cryptographic keys. After checking Webvue's cryptography policy, they concluded that the information obtained by the interviews was true. However, the cryptographic keys are still in use because the policy does not address the use and lifetime of cryptographic keys.
As later agreed upon between Webvue and the certification body, the audit team opted to conduct a virtual audit specifically focused on verifying conformity to control 8.11 Data Masking of ISO/IEC 27001 within Webvue, aligning with the certification scope and audit objectives. They examined the processes involved in protecting data within CloudWebvue. focusing on how the company adhered to its policies and regulatory standards. As part of this process. Keith, the audit team leader, took screenshot copies of relevant documents and cryptographic key management procedures to document and analyze the effectiveness of Webvue's practices.
Webvue uses generated test data for testing purposes. However, as determined by both the interview with the manager of the QA Department and the procedures used by this department, sometimes live system data are used. In such scenarios, large amounts of data are generated while producing more accurate results. The test data is protected and controlled, as verified by the simulation of the encryption process performed by Webvue's personnel during the audit
While interviewing the manager of the QA Department, Keith observed that employees in the Security Training Department were not following proper procedures, even though this department fell outside the audit scope. Despite the exclusion in the audit scope, the non conformity in the Security Training Department has potential implications for the processes within the audit scope, specifically impacting data security and cryptographic practices in CloudWebvue. Therefore, Keith incorporated this finding into the audit report and accordingly informed the auditee.
Based on the scenario above, answer the following question:
Question:
Based on Scenario 7, was Keith’s choice regarding the incorporation of the Security Training Department in the audit report appropriate?
What is meant by the term 'Corrective Action'? Select one
You receive the following mail from the IT support team: Dear User,Starting next week, we will be deleting all inactive email accounts in order to create spaceshare the below details in order to continue using your account. In case of no response,
Name:
Email ID:
Password:
DOB:
Kindly contact the webmail team for any further support. Thanks for your attention.
Which of the following is the best response?
In acceptable use of Information Assets, which is the best practice?
What is we do in ACT - From PDCA cycle
After drafting the audit conclusions, the work documents of the audit team leader were reviewed by another auditor selected by the certification body. Is this acceptable?
Scenario 9: UpNet, a networking company, has been certified against ISO/IEC 27001. It provides network security, virtualization, cloud computing, network hardware, network management software, and networking technologies.
The company's recognition has increased drastically since gaining ISO/IEC 27001 certification. The certification confirmed the maturity of UpNefs operations and its compliance with a widely recognized and accepted standard.
But not everything ended after the certification. UpNet continually reviewed and enhanced its security controls and the overall effectiveness and efficiency of the ISMS by conducting internal audits. The top management was not willing to employ a full-time team of internal auditors, so they decided to outsource the internal audit function. This form of internal audits ensured independence, objectivity, and that they had an advisory role about the continual improvement of the ISMS.
Not long after the initial certification audit, the company created a new department specialized in data and storage products. They offered routers and switches optimized for data centers and software-based networking devices, such as network virtualization and network security appliances. This caused changes to the operations of the other departments already covered in the ISMS certification scope.
Therefore. UpNet initiated a risk assessment process and an internal audit. Following the internal audit result, the company confirmed the effectiveness and efficiency of the existing and new processes and controls.
The top management decided to include the new department in the certification scope since it complies with ISO/IEC 27001 requirements. UpNet announced that it is ISO/IEC 27001 certified and the certification scope encompasses the whole company.
One year after the initial certification audit, the certification body conducted another audit of UpNefs ISMS. This audit aimed to determine the UpNefs ISMS fulfillment of specified ISO/IEC 27001 requirements and ensure that the ISMS is being continually improved. The audit team confirmed that the certified ISMS continues to fulfill
the requirements of the standard. Nonetheless, the new department caused a significant impact on governing the management system. Moreover, the certification body was not informed about any changes. Thus, the UpNefs certification was suspended.
Based on the scenario above, answer the following question:
UpNet announced that the ISMS certification scope encompasses the whole company once ensuring that the new department also complies with the ISO/IEC 27001 requirements. How would you classify this situation illustrated in scenario 9?
OrgXY is an ISO/IEC 27001-certified software development company. A year after being certified, OrgXY's top management informed the certification body that the company was not ready for conducting the surveillance audit. What happens in this case?
Total 418 questions