CloudSec-Pro Paloalto Networks Palo Alto Networks Cloud Security Professional Free Practice Exam Questions (2026 Updated)
Prepare effectively for your Paloalto Networks CloudSec-Pro Palo Alto Networks Cloud Security Professional certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
Total 258 questions
A customer has Prisma Cloud Enterprise and host Defenders deployed.
What are two options that allow an administrator to upgrade Defenders? (Choose two.)
Which resource and policy type are used to calculate AWS Net Effective Permissions? (Choose two.)
A customer's Security Operations Center (SOC) team wants to receive alerts from Prisma Cloud via email once a day about all policies that have a violation, rather than receiving an alert every time a new violation occurs.
Which alert rule configuration meets this requirement?
Which of the following is displayed in the asset inventory?
When configuring SSO how many IdP providers can be enabled for all the cloud accounts monitored by Prisma Cloud?
An administrator wants to enforce a rate limit for users not being able to post five (5) .tar.gz files within five (5) seconds.
What does the administrator need to configure?
Which ROL query is used to detect certain high-risk activities executed by a root user in AWS?
Console is running in a Kubernetes cluster, and Defenders need to be deployed on nodes within this cluster.
How should the Defenders in Kubernetes be deployed using the default Console service name?
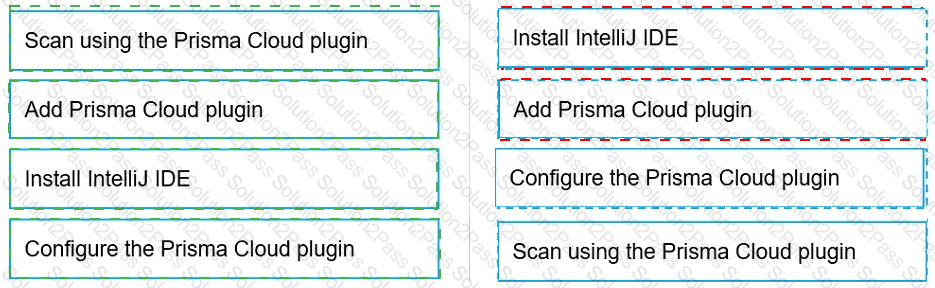
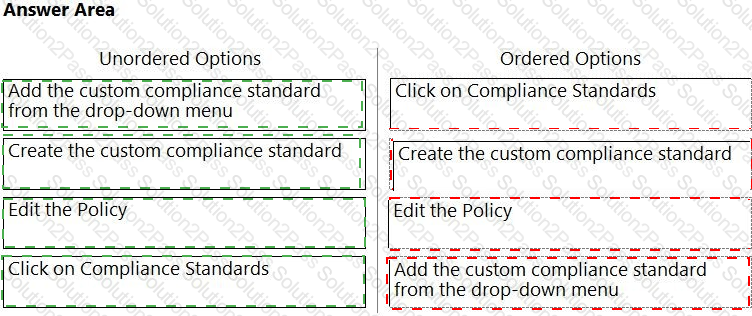
Which order of steps map a policy to a custom compliance standard?
(Drag the steps into the correct order of occurrence, from the first step to the last.)
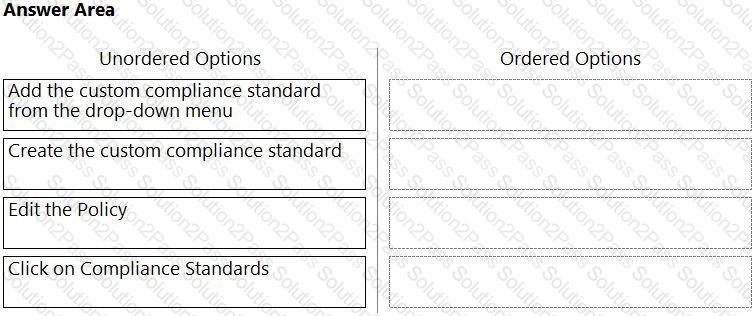
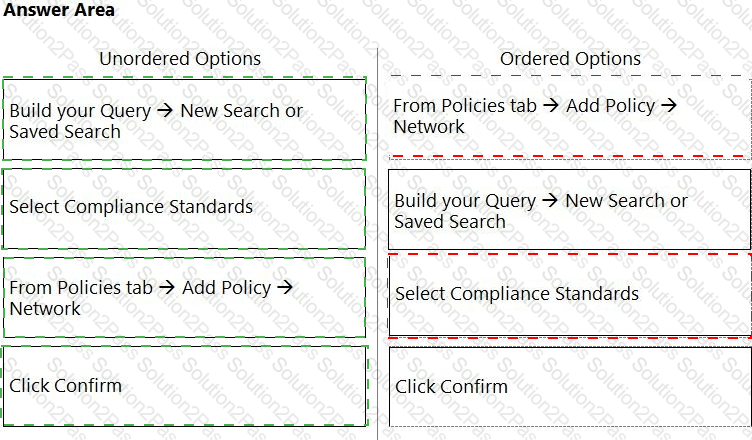
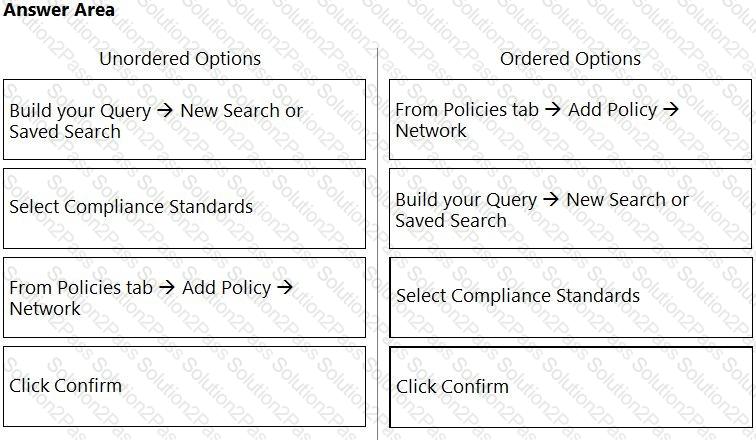
What is the order of steps to create a custom network policy?
(Drag the steps into the correct order of occurrence, from the first step to the last.)
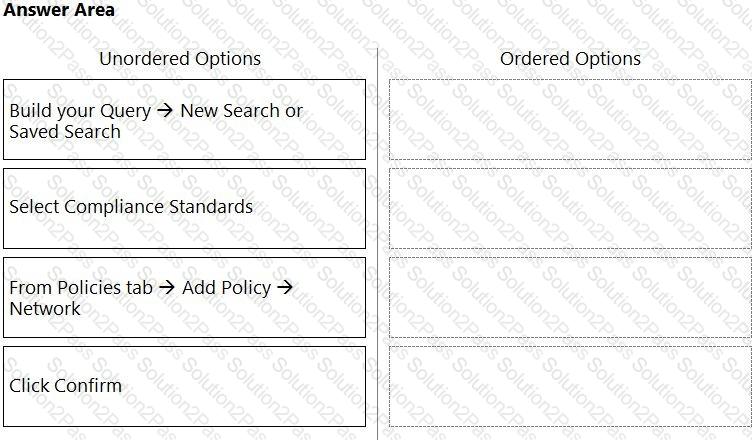
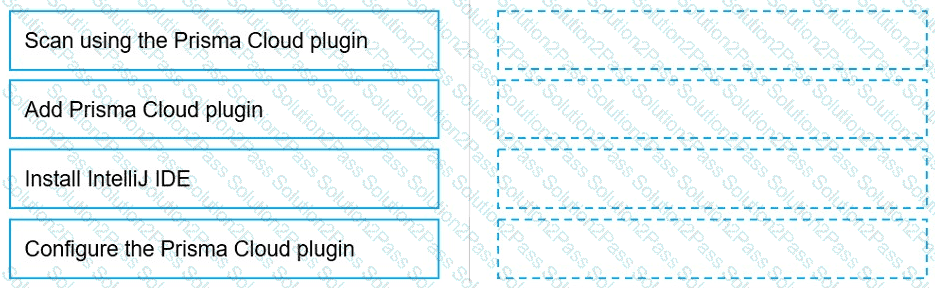
Put the steps involved to configure and scan using the IntelliJ plugin in the correct order.
In which two ways can Prisma Cloud images be retrieved in Prisma Cloud Compute Self-Hosted Edition? (Choose two.)
What improves product operationalization by adding visibility into feature utilization and missed opportunities?
Which two proper agentless scanning modes are supported with Prisma Cloud? (Choose two).
Which two services require external notifications to be enabled for policy violations in the Prisma Cloud environment? (Choose two.)
Which component of a Kubernetes setup can approve, modify, or reject administrative requests?
How many CLI remediation commands can be added in a custom policy sequence?
An administrator has access to a Prisma Cloud Enterprise.
What are the steps to deploy a single container Defender on an ec2 node?
Which step should a SecOps engineer implement in order to create a network exposure policy that identifies instances accessible from any untrusted internet sources?
What are two ways to scan container images in Jenkins pipelines? (Choose two.)
Total 258 questions
 A picture containing table Description automatically generated
A picture containing table Description automatically generated