TPAD01 Proofpoint Threat Protection Administrator Exam Free Practice Exam Questions (2026 Updated)
Prepare effectively for your Proofpoint TPAD01 Threat Protection Administrator Exam certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
Can a new email digest be generated for every email which enters quarantine?
What is the primary function of Proofpoint Targeted Attack Protection (TAP)?
You are tasked with configuring outbound mail for an organization where an external domain has multiple MX records. Only one specific host is accepting mail. What is the best way to specify this specific hostname for outbound mail?
How does TAP’s Message Defense feature work for unknown attachments?
Refer to the exhibit below to see the interface used in this scenario.
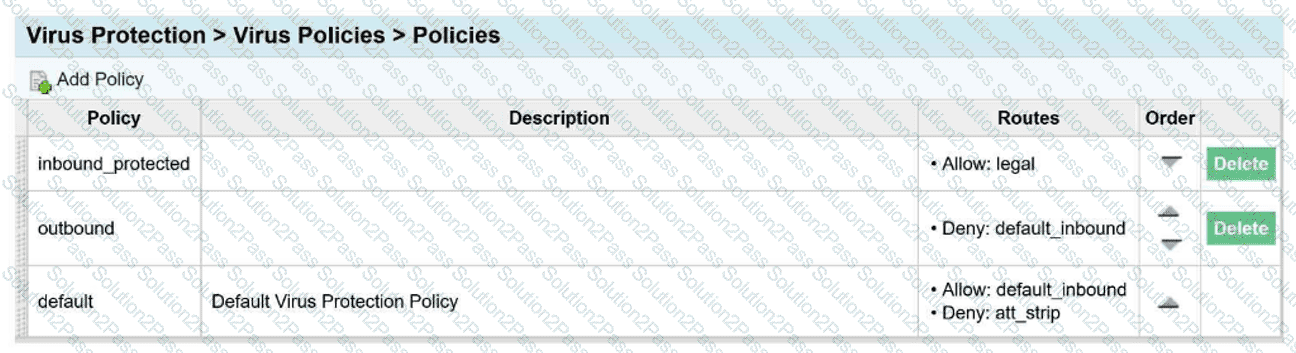
An email arrives inbound to the protection server, it is going to a single recipient and belongs
to the legal and default_inbound policy routes.
Which of the following is true regarding the virus policies?
The Abuse Mailbox event source was working in Cloud Threat Protection, but is now showing red under status and is no longer processing emails. After editing the source and clicking “Validate Source,” you receive the error “Unable to validate mailbox.” What is the likely cause of this error?
When TLS is enabled, what is the default behavior regarding TLS on the Protection Server?
You log into the Protection Server and a rule you created yesterday is no longer enabled. Where can you find out what happened to the rule you created?
Review the filter log exhibit.
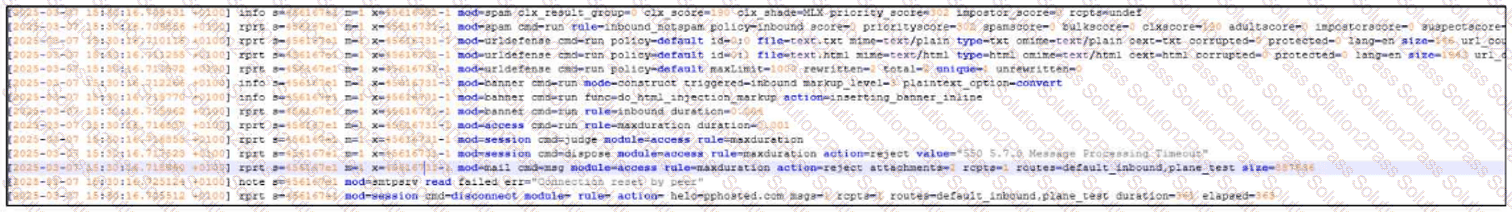
What two actions have taken place in the filter logs for this message?
What the exhibit shows clearly:
- URL Defense processing is present in the log
- A spam-related action/flag is present
How does Proofpoint use TLS in email security?
You are using Smart Search within the PPS Admin UI to investigate the final disposition of a message. Smart Search shows the message is Quarantined/Discard to adqueue. How do you trace the message?
When employees at your company change their name, their email address also changes. To ensure that the user import process associates the new email addresses with the existing users, how should you configure the primary key?
Which feature on the Protection Server would you use to prevent Email Warning Tags being inserted into a trusted sender’s emails?
You wish to ensure that all emails to an external partner are sent over a secure connection. What should you do?
What is the primary purpose of outbound mail filtering in Proofpoint?
During the configuration of an alert profile, which option is specifically required to ensure alerts are delivered to the appropriate individuals?
Which Email Firewall features should be used together to mitigate directory harvest attacks?
Smart Search has returned 13 results for a specific recipient address. You click on one of the messages in the Results list. Which of the following information is available for that message?
When using Smart Search to access the MTA Log during troubleshooting, what type of information does the MTA Log contain?
An email message fails an SPF check; which of the following is a likely reason for this failure?
