200-201 Cisco Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS) Free Practice Exam Questions (2026 Updated)
Prepare effectively for your Cisco 200-201 Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS) certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
After a large influx of network traffic to externally facing devices, a security engineer begins investigating what appears to be a denial of service attack When the packet capture data is reviewed, the engineer notices that the traffic is a single SYN packet to each port Which type of attack is occurring?
A security analyst received a ticket about suspicious traffic from one of the workstations. During the investigation, the analyst discovered that the workstation was communicating with an external IP. The analyst could not investigate further and escalated the case to a T2 security analyst. What are the two data visibility challenges that the security analyst should identify? (Choose two.)
What is the function of a command and control server?
What is a difference between tampered and untampered disk images?
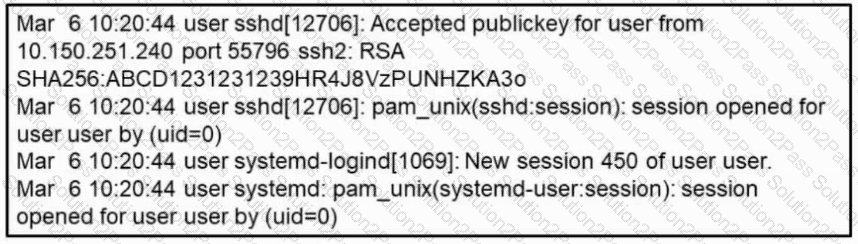
Refer to the exhibit. What occurred on this system based on this output?
How does an SSL certificate impact security between the client and the server?
Which type of verification consists of using tools to compute the message digest of the original and copied data, then comparing the similarity of the digests?
A security engineer must determine why a new core application does not work as desired The client can send requests toward the application server but receives no response One of the requirements is to gather all packets Data needs to be reliable without any delay or packet drops Which solution best meets this need?
A company is using several network applications that require high availability and responsiveness, such that milliseconds of latency on network traffic is not acceptable. An engineer needs to analyze the network and identify ways to improve traffic movement to minimize delays. Which information must the engineer obtain for this analysis?
What is a ransomware attack?
Which data format is the most efficient to build a baseline of traffic seen over an extended period of time?
Which regular expression matches loopback IP address (127.0.0.1)?
An engineer must verify vulnerabilities found in the scanning process The engineer checks the impact of those findings to the organization and compares the results with known threats inside organization What is the benefit of knowing this information?
What is data tunneling?
How is NetFlow different from traffic mirroring?
The SOC team has confirmed a potential indicator of compromise on an endpoint. The team has narrowed the executable file's type to a new trojan family. According to the NIST Computer Security Incident Handling Guide, what is the next step in handling this event?
Which process represents the application-level allow list?
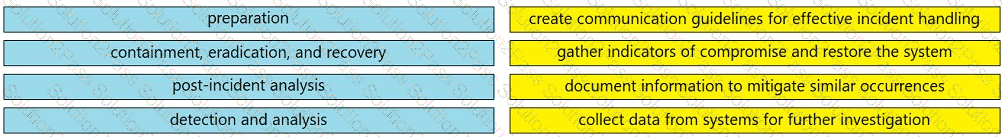
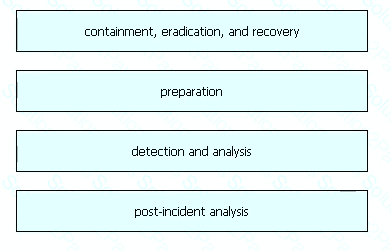
Drag and drop the elements from the left into the correct order for incident handling on the right.
What is the difference between tampered and untampered disk images?
Which regex matches only on all lowercase letters?
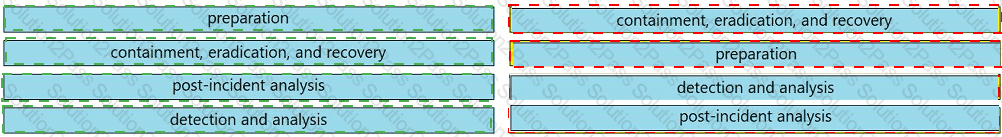
 A close-up of several blue rectangular boxes Description automatically generated
A close-up of several blue rectangular boxes Description automatically generated