200-201 Cisco Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS) Free Practice Exam Questions (2026 Updated)
Prepare effectively for your Cisco 200-201 Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS) certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
What is the advantage of agent-based protection compared to agentless protection?
Exhibit.
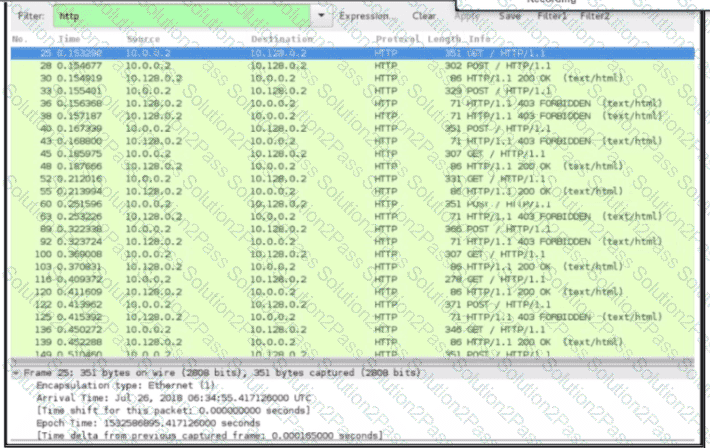
An engineer received a ticket about a slowdown of a web application, Drug analysis of traffic, the engineer suspects a possible attack on a web server. How should the engineer interpret the Wiresharat traffic capture?
Which metric is used to capture the level of access needed to launch a successful attack?
A security expert is working on a copy of the evidence, an ISO file that is saved in CDFS format. Which type of evidence is this file?
A multinational organization uses a complex network infrastructure incorporating multiple cloud services, diverse endpoints, and distributed networks with several security devices. Which challenge will the security team face when ensuring robust data visibility for effective threat detection and response?
An analyst received a ticket regarding a degraded processing capability for one of the HR department's servers. On the same day, an engineer noticed a disabled antivirus software and was not able to determine when or why it occurred. According to the NIST Incident Handling Guide, what is the next phase of this investigation?
An engineer needs to have visibility on TCP bandwidth usage, response time, and latency, combined with deep packet inspection to identify unknown software by its network traffic flow. Which two features of Cisco Application Visibility and Control should the engineer use to accomplish this goal? (Choose two.)
An engineer receives a security alert that traffic with a known TOR exit node has occurred on the network. What is the impact of this traffic?
How does the approach of a behavioral detection system to identifying security threats compare to that of a rule-based detection system?
Which attack method intercepts traffic on a switched network?
An engineer is sharing folders and files with different departments and got this error: "No such file or directory". What must the engineer verify next?
Which signature impacts network traffic by causing legitimate traffic to be blocked?
A security engineer must investigate a recent breach within the organization. An engineer noticed that a breached workstation is trying to connect to the domain "Ranso4730-mware92-647". which is known as malicious. In which step of the Cyber Kill Chain is this event?
Refer to the exhibit.
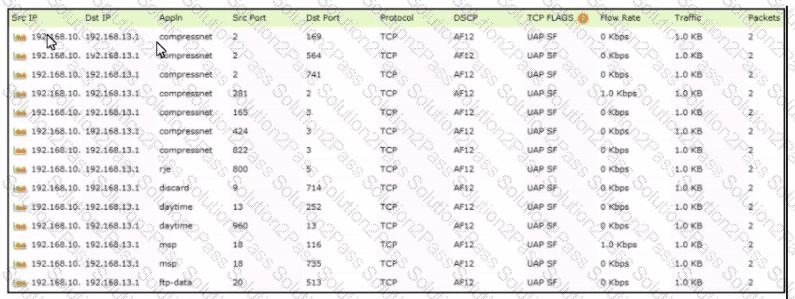
Which tool was used to generate this data?
Which security model assumes an attacker within and outside of the network and enforces strict verification before connecting to any system or resource within the organization?
An analyst is exploring the functionality of different operating systems.
What is a feature of Windows Management Instrumentation that must be considered when deciding on an operating system?
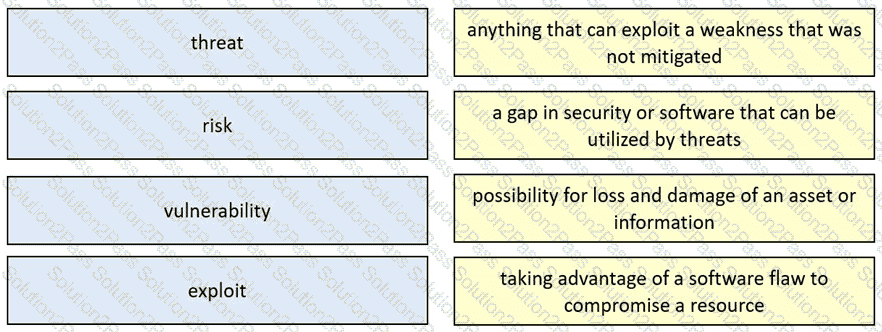
Drag and drop the security concept from the left onto the example of that concept on the right.
Which two pieces of information are collected from the IPv4 protocol header? (Choose two.)
Which CVSS metric group identifies other components that are affected by a successful security attack?
Refer to the exhibit.
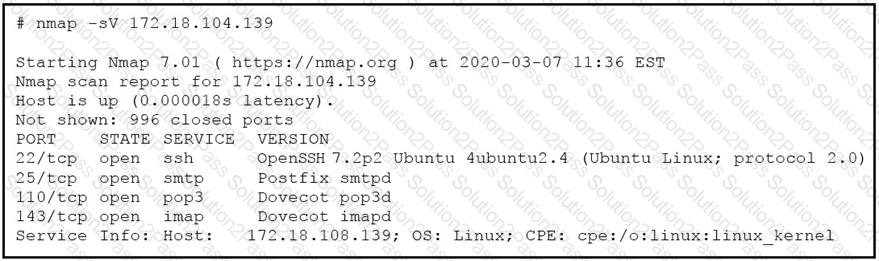
What does the output indicate about the server with the IP address 172.18.104.139?
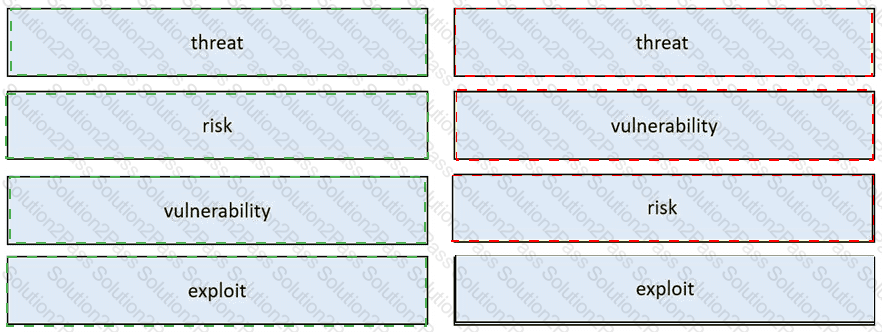
 Table Description automatically generated
Table Description automatically generated