200-201 Cisco Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS) Free Practice Exam Questions (2026 Updated)
Prepare effectively for your Cisco 200-201 Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS) certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
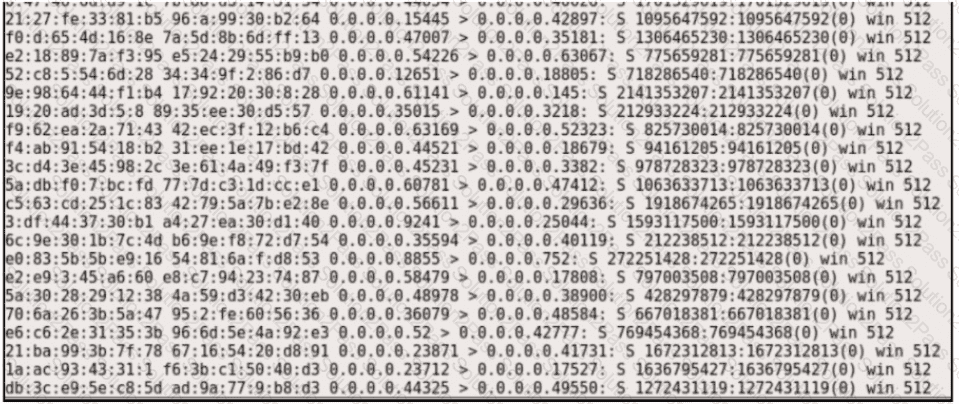
Refer to the exhibit.
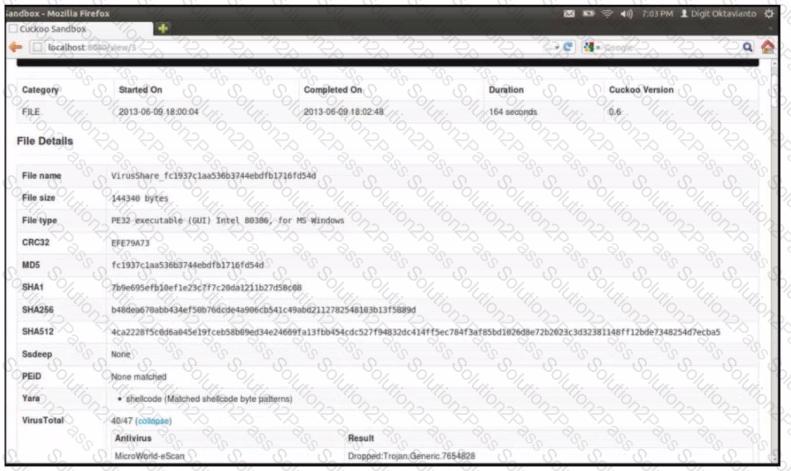
What does this Cuckoo sandbox report indicate?
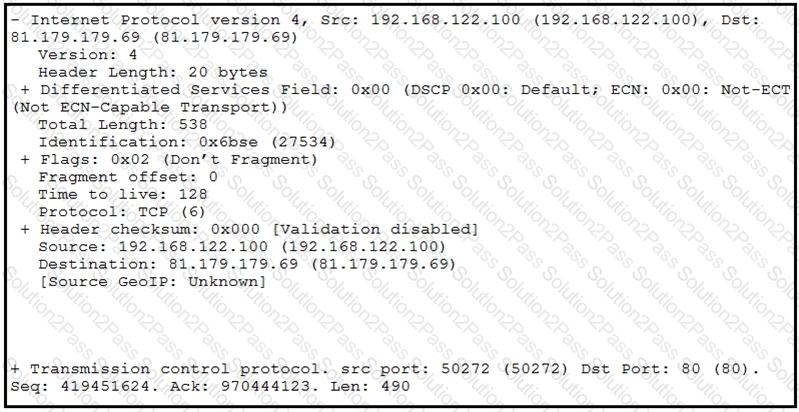
Refer to the exhibit.
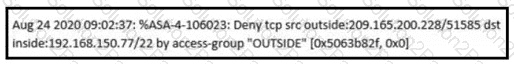
An analyst received this alert from the Cisco ASA device, and numerous activity logs were produced. How should this type of evidence be categorized?
What is the difference between inline traffic interrogation and traffic mirroring?
Syslog collecting software is installed on the server For the log containment, a disk with FAT type partition is used An engineer determined that log files are being corrupted when the 4 GB tile size is exceeded. Which action resolves the issue?
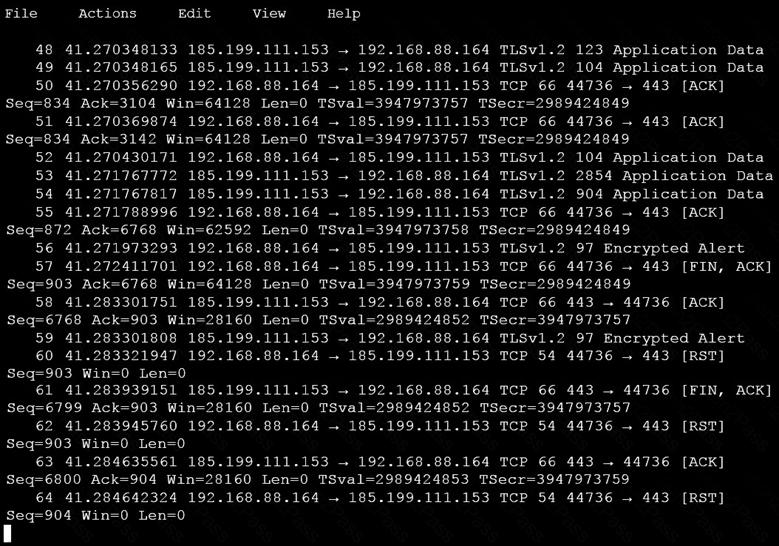
Refer to the exhibit.
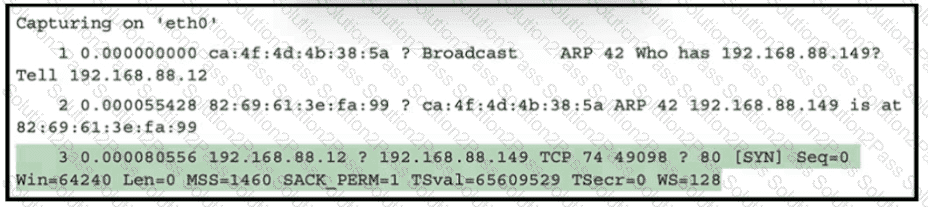
What must be interpreted from this packet capture?
A cyberattacker notices a security flaw in a software that a company is using They decide to tailor a specific worm to exploit this flaw and extract saved passwords from the software To which category of the Cyber Kill Cham model does this event belong?
Refer to exhibit.
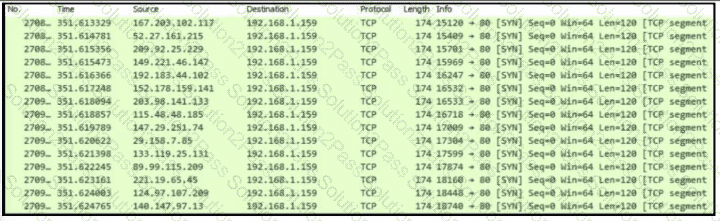
An engineer is Investigating an Intrusion and Is analyzing the pcap file. Which two key elements must an engineer consider? (Choose two.)
Which access control should a chief information security officer select to protect extremely sensitive data categorized at various levels of confidentiality?
Which data capture includes payload and header information?
Refer to the exhibit.
Which type of attack is represented?
Refer to the exhibit.
What should be interpreted from this packet capture?
An analyst is investigating a host in the network that appears to be communicating to a command and control server on the Internet. After collecting this packet capture, the analyst cannot determine the technique and payload used for the communication.
Which obfuscation technique is the attacker using?
What is a difference between SOAR and SIEM?
Which statement describes threat hunting?
What are indicators of attack?
A developer is working on a project using a Linux tool that enables writing processes to obtain these required results:
If the process is unsuccessful, a negative value is returned.
If the process is successful, 0 value is returned to the child process, and the process ID is sent to the parent process.
Which component results from this operation?
Which security technology allows only a set of pre-approved applications to run on a system?
Refer to the exhibit.
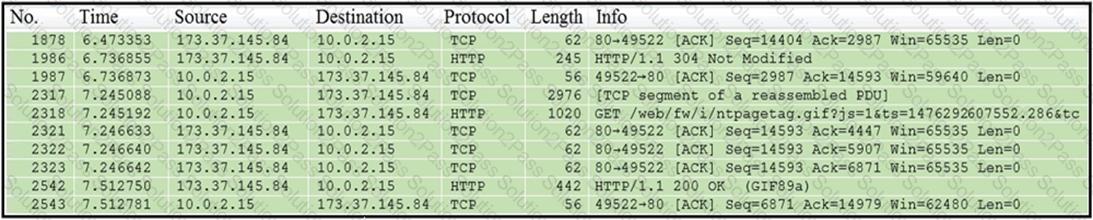
Which packet contains a file that is extractable within Wireshark?
An engineer discovered a breach, identified the threat’s entry point, and removed access. The engineer was able to identify the host, the IP address of the threat actor, and the application the threat actor targeted. What is the next step the engineer should take according to the NIST SP 800-61 Incident handling guide?
Refer to the exhibit.
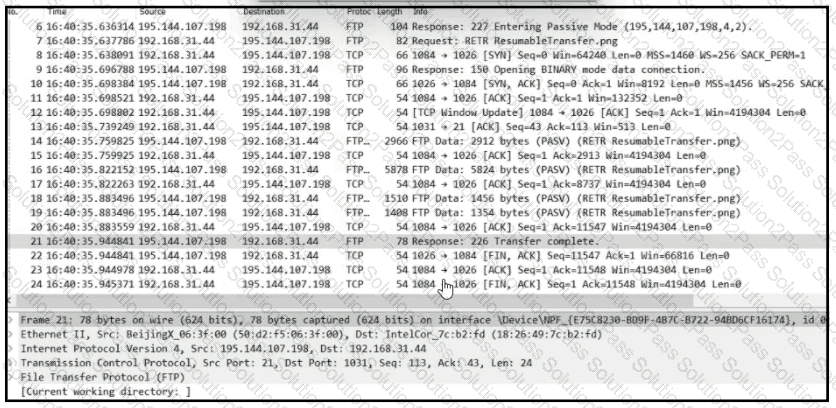
Which frame numbers contain a file that is extractable via TCP stream within Wireshark?
