200-301 Cisco Implementing and Administering Cisco Solutions (200-301 CCNA) v1.1 Free Practice Exam Questions (2026 Updated)
Prepare effectively for your Cisco 200-301 Implementing and Administering Cisco Solutions (200-301 CCNA) v1.1 certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
How does a switch process a frame received on Fa0/1 with the destination MAC address of 0e38.7363.657b when the table is missing the address?
What is a role of wireless controllers in an enterprise network?
What is the purpose of traffic shaping?
What are two functions of a Layer 2 switch? (Choose two)
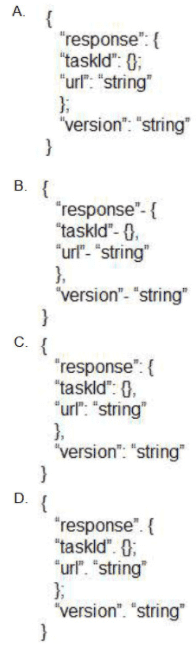
Which output displays a JSON data representation?
In software defined architectures, which plane is distributed and responsible for traffic forwarding?
When a switch receives a frame for a known destination MAC address, how is the frame handed?
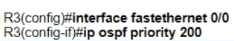
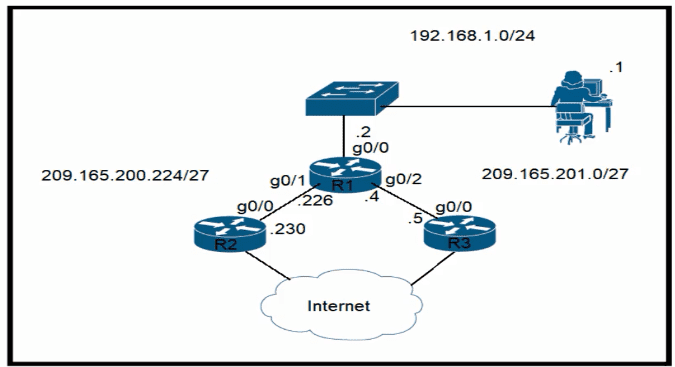
Refer to the exhibit.

Router R4 is dynamically learning the path to the server. If R4 is connected to R1 via OSPF Area 20, to R2 v2ia R2 BGP, and to R3 via EIGRP 777, which path is installed in the routing table of R4?
Which 802.11 management frame type is sent when a client roams between access points on the same SSID?
A manager asks a network engineer to advise which cloud service models are used so employees do not have to waste their time installing, managing, and updating software which is only used occasionally Which cloud service model does the engineer recommend?
By default, how Does EIGRP determine the metric of a route for the routing table?
Which API is used in controller-based architectures to interact with edge devices?
Which device segregates a network into separate zones that have their own security policies?
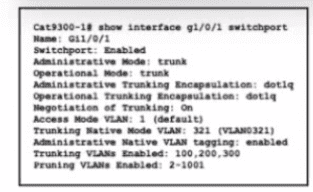
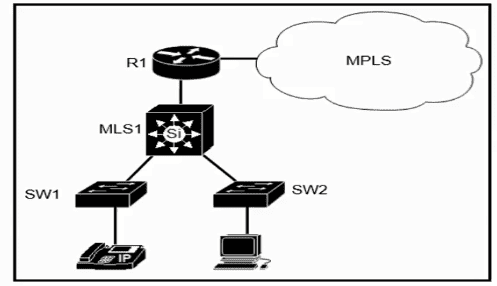
Refer to the exhibit.
A network administrator configures an interface control re switch so that it connects to interface Gi1/0/1 on switch Cat9300-1. Which configuration must be applied to the new interface?
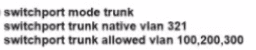
A)
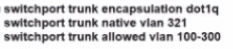
B)
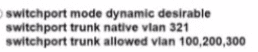
C)
D)
Which two capabilities of Cisco DNA Center make it more extensible as compared to traditional campus device management? (Choose two.)
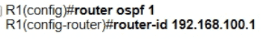
Refer to the exhibit.
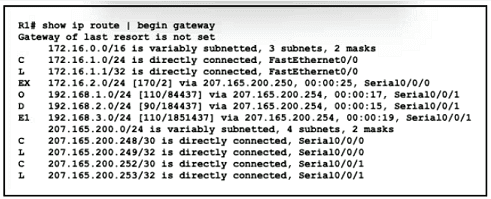
Which prefix did router R1 learn from internal EIGRP?
What is a specification for SSIDS?
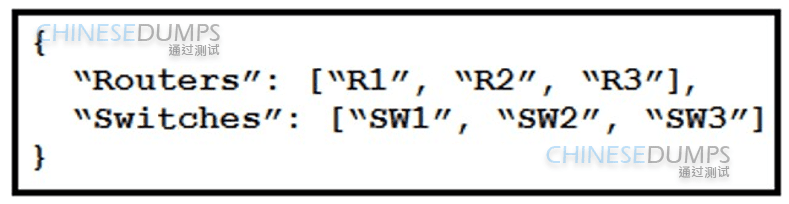
Refer to the exhibit. What is represented by “R1” and “SW1” within the JSON output?
object
value
Which part of the HTTP request is used in REST API basic authentication to carry credentials?
What are two reasons to implement DHCP in a network? (Choose two.)
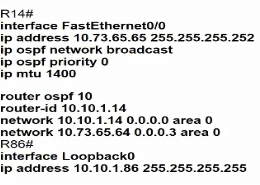
Refer to the exhibit.
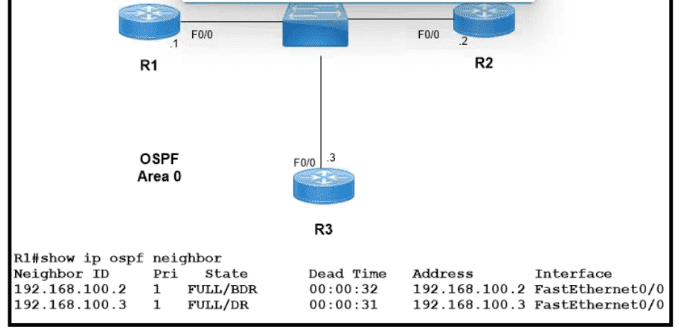
Which two configurations must the engineer apply on this network so that R1 becomes the DR? (Choose two.)
A)
B)
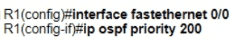
C)
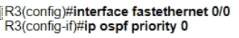
D)
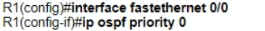
E)
Which QoS per-hop behavior changes the value of the ToS field in the IPv4 packet header?
A Cisco engineer is configuring a factory-default router with these three passwords:
• The user EXEC password for console access is p4ssw0rd1
• The user EXEC password for Telnet access is s3cr3t2
• The password for privileged EXEC mode is pnv4t3p4ss Which command sequence must the engineer configured
A)
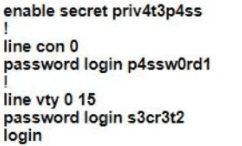
B)
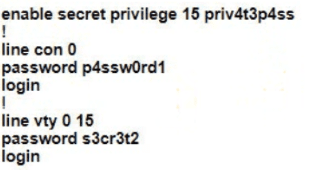
C)
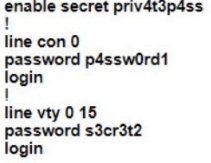
D)
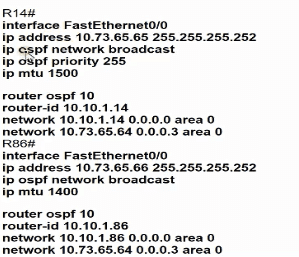
Refer to the exhibit.
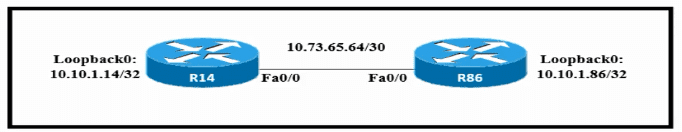
Which configuration allows routers R14 and R86 to form an OSPFv2 adjacency while acting as a central point for exchanging OSPF information between routers?
A)
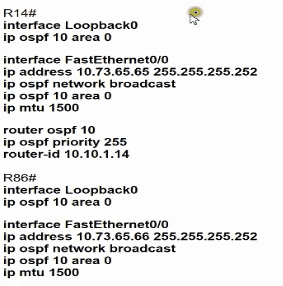
B)
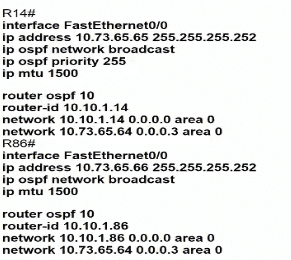
C)
D)
Which protocol is used for secure remote CLI access?
Refer to the exhibit.
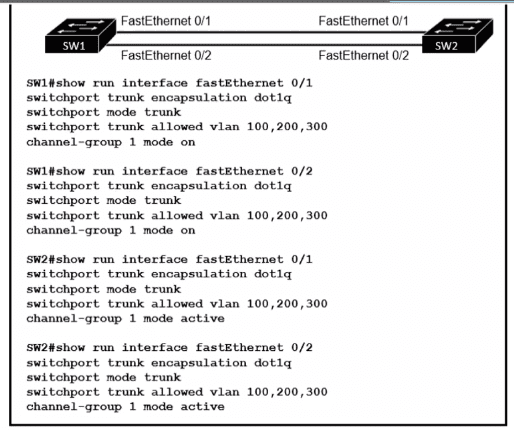
An engineer built a new L2 LACP EtherChannel between SW1 and SW2 and executed these show commands to verify the work. Which additional task allows the two switches to establish an LACP port channel?
Refer to the exhibit.
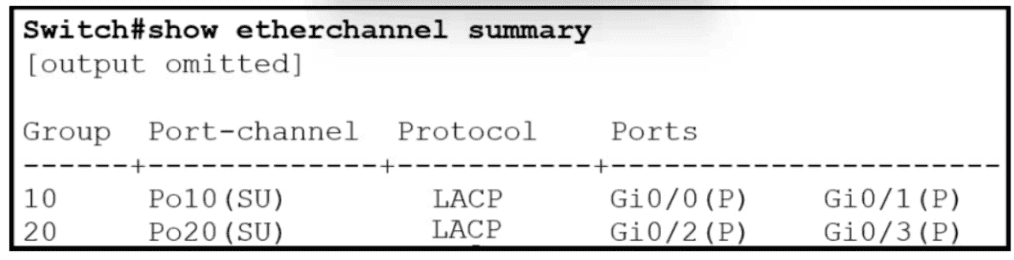
Which two commands when used together create port channel 10? (Choose two.)
What provides centralized control of authentication and roaming In an enterprise network?
Refer to the exhibit.
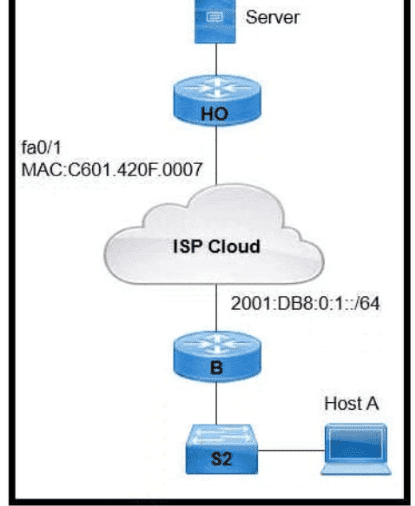
An engineer is configuring the HO router. Which IPv6 address configuration must be applied to the router fa0'1 interface for the router to assign a unique 64-brt IPv6 address to Itself?
Refer to the exhibit.
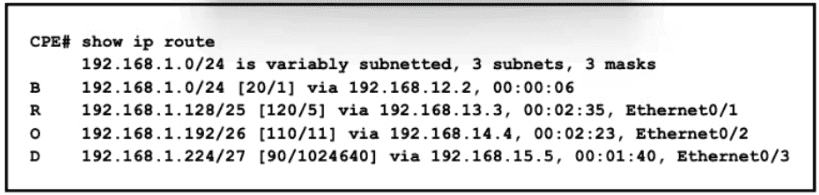
All traffic enters the CPE router from interface Serial0/3 with an IP address of 192 168 50 1 Web traffic from the WAN is destined for a LAN network where servers are load-balanced An IP packet with a destination address of the HTTP virtual IP of 192 1681 250 must be forwarded Which routing table entry does the router use?
What are two benefits of FHRPs? (Choose two.)
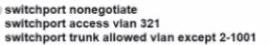
Refer to the exhibit.
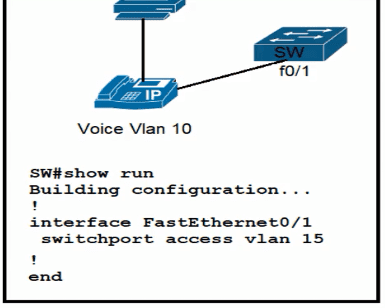
All VLANs are present in the VLAN database. Which command sequence must be applied to complete the configuration?
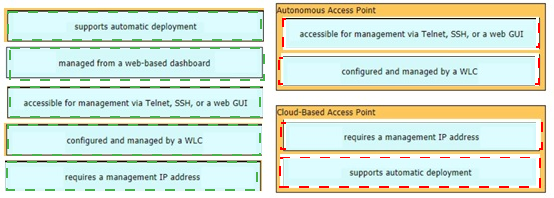
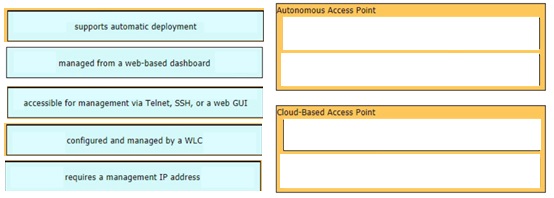
Drag and drop the facts about wireless architectures from the left onto the types of access point on the right. Not all options are used.
Which interface mode must be configured to connect the lightweight APs in a centralized architecture?
Refer to the exhibit.
Router R1 currently is configured to use R3 as the primary route to the Internet, and the route uses the default administrative distance settings. A network engineer must configure R1 so that it uses R2 as a backup, but only if R3 goes down. Which command must the engineer configure on R1 so that it correctly uses R2 as a backup route, without changing the administrative distance configuration on the link to R3?
Refer to the exhibit.
Which plan must be Implemented to ensure optimal QoS marking practices on this network?
What is the difference between IPv6 unicast and anycast addressing?
Which WLC management connection type is vulnerable to man-in-the-middle attacks?
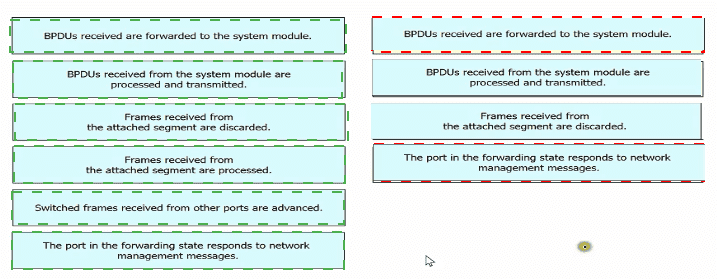
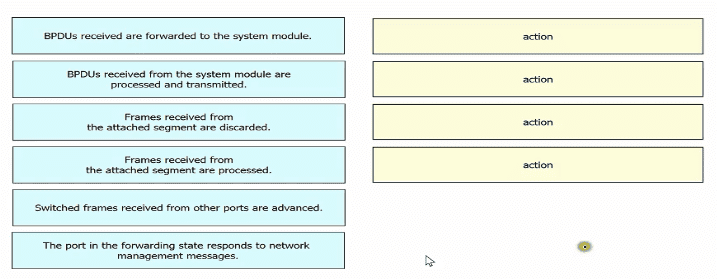
Drag and drop the Rapid PVST+ forwarding slate actions from the loft to the right. Not all actions are used.
A network engineer is installing an IPv6-only capable device. The client has requested that the device IP address be reachable only from the internal network. Which type of IPv6 address must the engineer assign?
Refer to the exhibit.
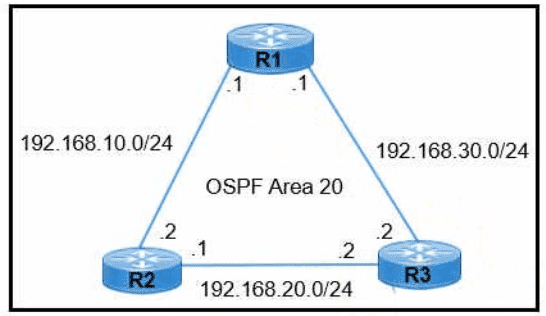
R1 learns all routes via OSPF Which command configures a backup static route on R1 to reach the 192 168.20.0/24 network via R3?
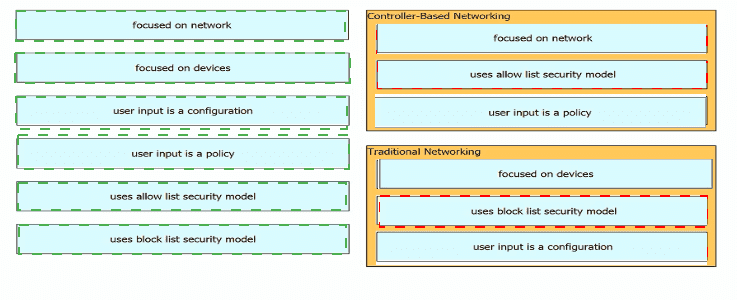
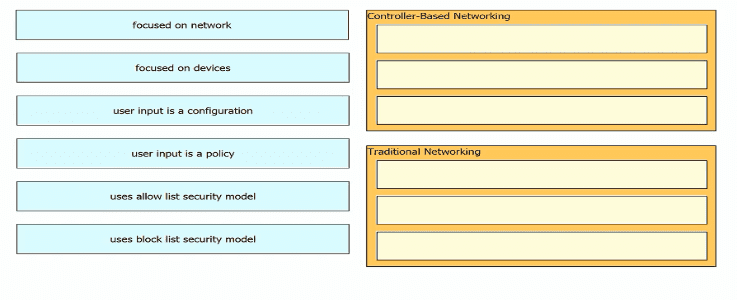
Drag and drop the characteristics of networking from the left onto the networking types on the right.
Refer to the exhibit.
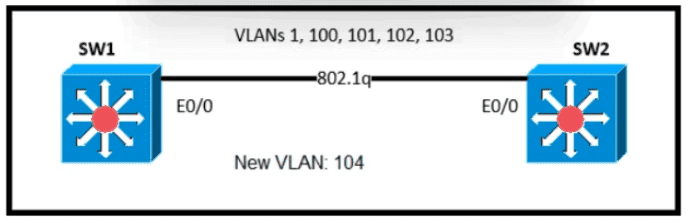
An engineer is asked to insert the new VLAN into the existing trunk without modifying anything previously configured Which command accomplishes this task?
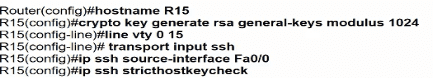
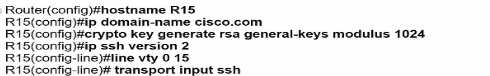
Refer to the exhibit.
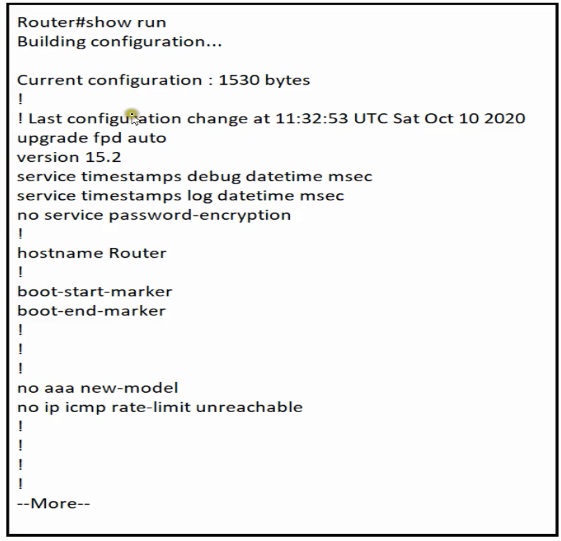
Which minimum configuration items are needed to enable Secure Shell version 2 access to R15?
A)
B)
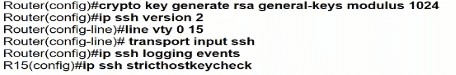
C)
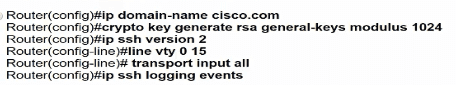
D)
Which two components comprise part of a PKI? (Choose two.)
A network engineer must implement an IPv6 configuration on the vlan 2000 interface to create a routable locally-unique unicast address that is blocked from being advertised to the internet. Which configuration must the engineer apply?
Which two network actions occur within the data plane? (Choose two.)
Which characteristic differentiates the concept of authentication from authorization and accounting?
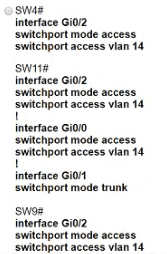
Refer to the exhibit.
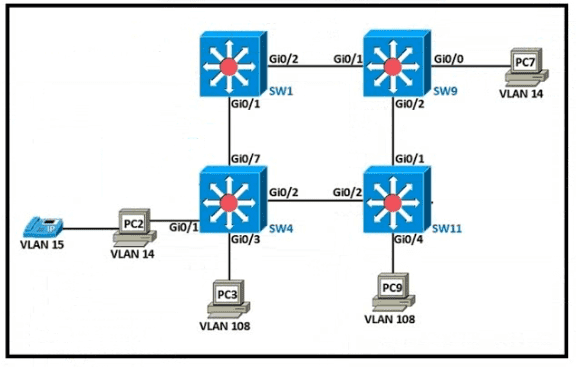
The following must be considered:
• SW1 is fully configured for all traffic
• The SW4 and SW9 links to SW1 have been configured
• The SW4 interface Gi0/1 and Gi0/0 on SW9 have been configured
• The remaining switches have had all VLANs adde d to their VLAN database
Which configuration establishes a successful ping from PC2 to PC7 without interruption to traffic flow between other PCs?
A)
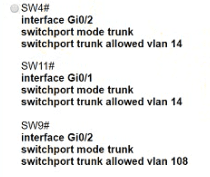
B)
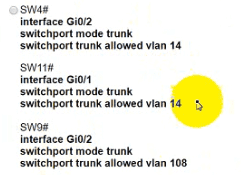
C)
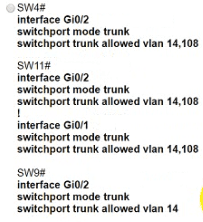
D)
Which field within the access-request packet is encrypted by RADIUS?
Refer to the exhibit.
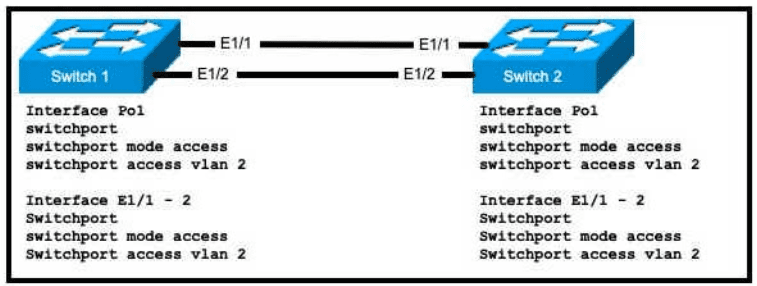
An engineer is configuring an EtherChannel using LACP between Switches 1 and 2 Which configuration must be applied so that only Switch 1 sends LACP initiation packets?
Refer to the exhibit.
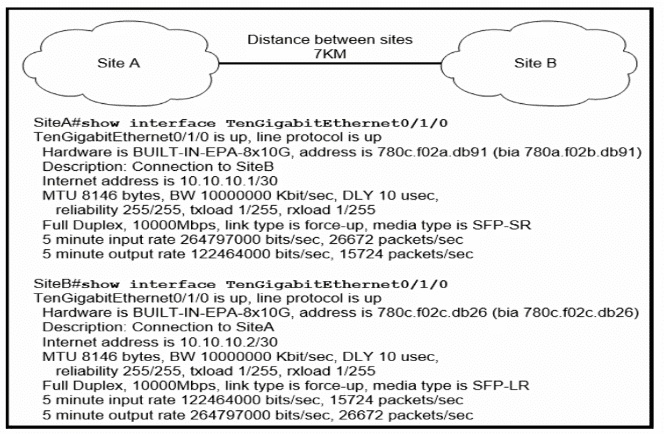
Site A was recently connected to site B over a new single-mode fiber path. Users at site A report Intermittent connectivity Issues with applications hosted at site B. What is the reason for the problem?
Refer to the exhibit.
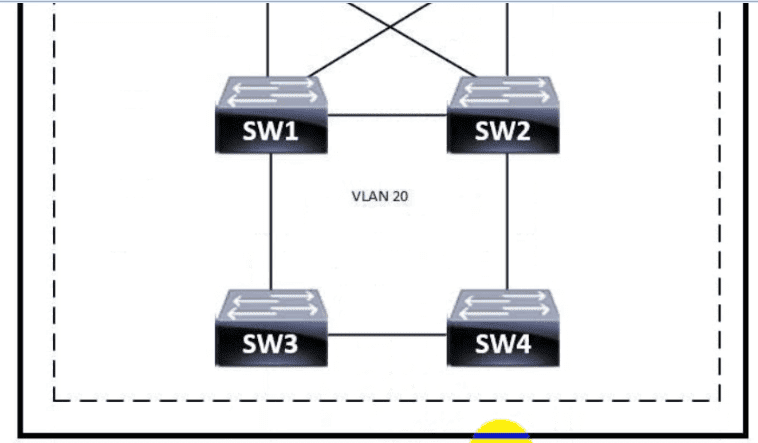
Which switch becomes the root of a spanning tree for VLAN 20 if all li links are of equal speed?
Which action implements physical access control as part of the security program of an organization?
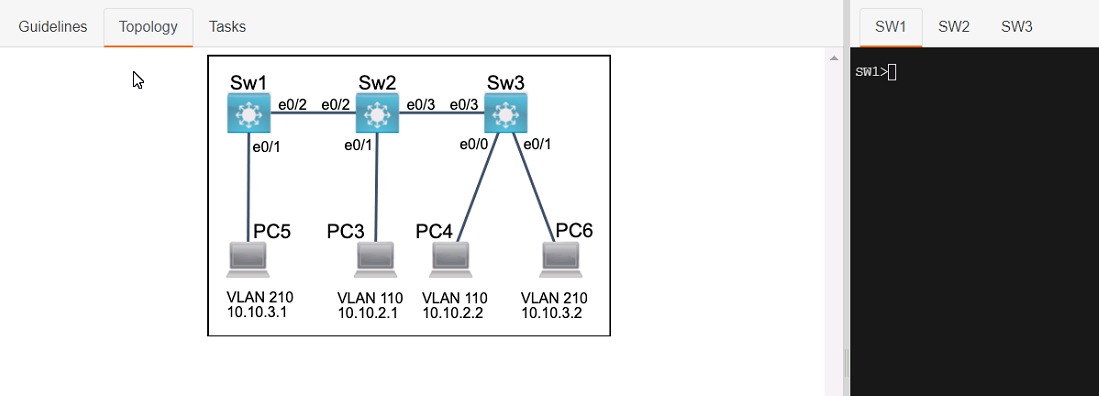
Three switches must be configured for Layer 2 connectivity. The company requires only the designated VLANs to be configured on their respective switches and permitted accross any links between switches for security purposes. Do not modify or delete VTP configurations.
The network needs two user-defined VLANs configured:
VLAN 110: MARKETING
VLAN 210: FINANCE
1. Configure the VLANs on the designated switches and assign them as access ports to the interfaces connected to the PCs.
2. Configure the e0/2 interfaces on Sw1 and Sw2 as 802.1q trunks with only the required VLANs permitted.
3. Configure the e0/3 interfaces on Sw2 and Sw3 as 802.1q trunks with only the required VLANs permitted.
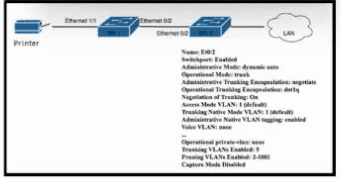
Refer to the exhibit. An administrator must connect SW_1 and the printer to the network. SW_2 requires DTP to be used for the connection to SW_1. The printer is configured as an access port with VLAN 5. Which set of commands completes the connectivity?
An engineer must update the configuration on two PCs in two different subnets to communicate locally with each other. One PC is configured with IP address 192.168.25.128/25 and the other with 192.168.25.100/25. Which network mask must the engineer configure on both PCs to enable the communication?
Which AP feature provides a captive portal for users to authenticate, register, and accept terms before accessing the internet?
Which interface is used to send traffic to the destination network?
10.90.207.87/26 [110/1912] via F0/7
10.90.207.87/26 [110/28968] via F0/6
10.90.207.87/26 [120/14] via F0/4
10.90.207.87/26 [120/11] via F0/5
Why are API keys used to enforce rate limiting?