300-720 Cisco Securing Email with Cisco Email Security Appliance (300-720 SESA) Free Practice Exam Questions (2026 Updated)
Prepare effectively for your Cisco 300-720 Securing Email with Cisco Email Security Appliance (300-720 SESA) certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
A content dictionary was created for use with Forged Email Detection. Proper data that pertains to the CEO Example CEO: < ceo@example com > must be entered. What must be added to the dictionary to accomplish this goal?
Which type of attack is prevented by configuring file reputation filtering and file analysis features?
When the spam quarantine is configured on the Cisco Secure Email Gateway, which type of query is used to validate non administrative user access to the end-user quarantine via LDAP?
Which feature must be activated on a Cisco Secure Email Gateway to combat backscatter?
The company security policy requires that the finance department have an easy way to apply encryption to their outbound messages that contain sensitive data Users must be able to flag the messages that require encryption versus a Cisco Secure Email Gateway appliance scanning all messages and automatically encrypting via detection Which action enables this capability?
What is the default method of remotely accessing a newly deployed Cisco Secure Email Virtual Gateway when a DHCP server is not available?
The CEO sent an email indicating that all emails containing a string of 123ABCDEFGHJ cannot be delivered and must be sent into quarantine for further inspection. Given the requirement, which regular expression should be used to match on that criteria?
When a network engineer is troubleshooting a mail flow issue, they discover that some emails are rejected with an SMTP code of 451 and the error message " #4.7.1 Unable to perform DMARC verification " . In the DMARC verification profile on the Cisco Secure Email Gateway appliance, which action must be set for messages that result in temporary failure to prevent these emails from being rejected?
An administrator manipulated the subnet mask but was still unable to access the user interface. How must the administrator access the Cisco Secure Email Gateway appliance to perform the initial configuration?
Which SMTP extension does Cisco ESA support for email security?
An engineer must modify the altsrchost table on a Cisco Secure Email Gateway Messages destined for a domain named @cisco.com must be mapped to Newlnterface with an IP address of 10.10.10.1. What must be added to the table?
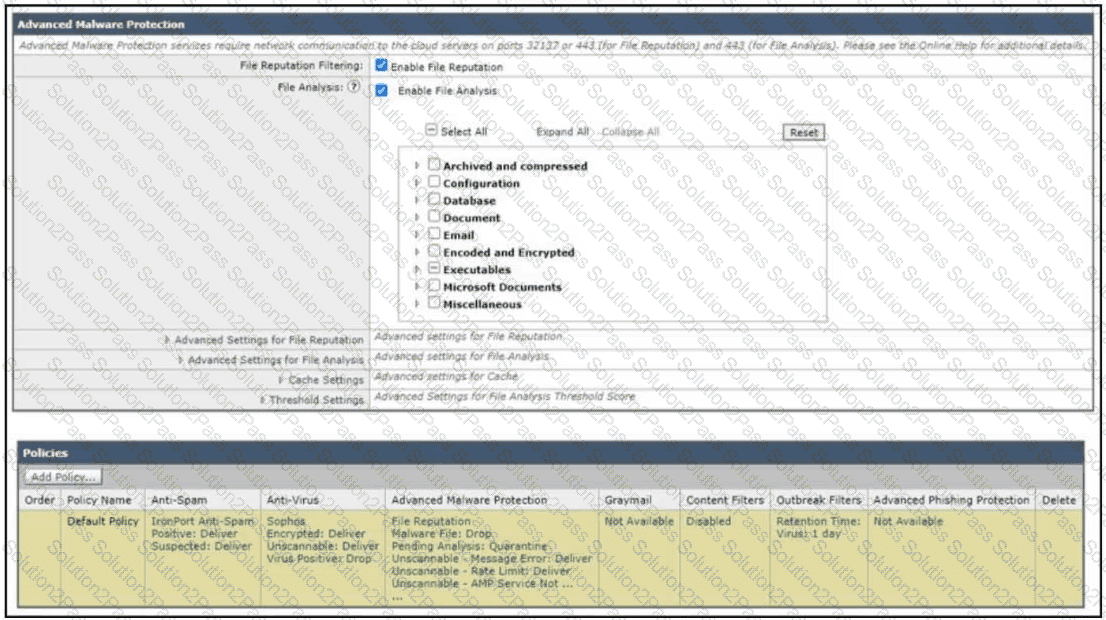
Refer to the exhibit. How does the Cisco Secure Email Gateway handle an email with an unknown Microsoft Word document?
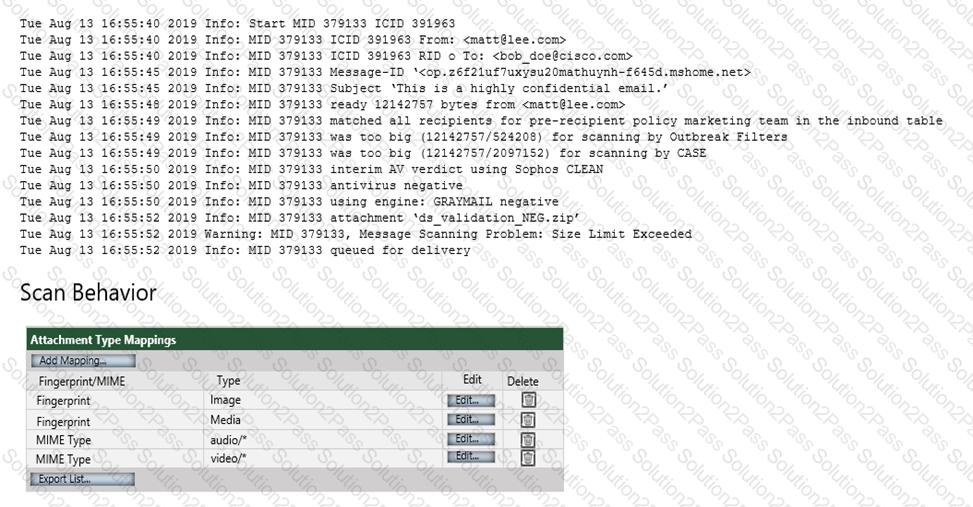
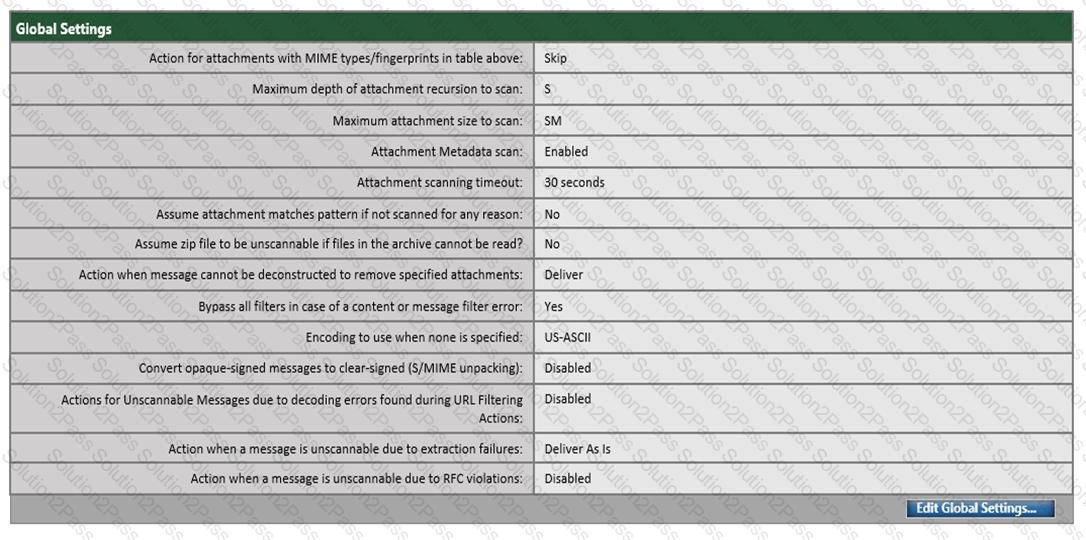
Refer to the exhibit. Which configuration on the scan behavior must be updated to allow the attachment to be scanned on the Cisco ESA?
A security administrator deployed a Cisco Secure Email Gateway appliance with a mail policy configured to store suspected spam for review. The appliance is the DMZ and only the standard HTTP/HTTPS ports are allowed by the firewall. An administrator wants to ensure that users can view any suspected spam that was blocked. Which action must be taken to meet this requirement?
An engineer must add cisco.com to the listed domains in Cisco Secure Email Gateway that accept messages. All other domains must be blocked, and the message must be sent back to the sender is Domain Blocked. Which two actions must be taken to meet the requirement? (Choose two.)
Which setting affects the aggressiveness of spam detection?
Which method enables an engineer to deliver a flagged message to a specific virtual gateway address in the most flexible way?
Which two are configured in the DMARC verification profile? (Choose two.)
An engineer is tasked with creating a content filter to catch attachments, including credit card numbers, and hold them for review until further action is taken. Which component on a Cisco Secure Email Gateway must be configured to meet this requirement?
A trusted partner of an organization recently experienced a new campaign that was leveraging JavaScript attachments to trick users into executing malware. As a result, they created a local policy to deny messages with JavaScript attachments. Which action should the administrator of the organization take to ensure encrypted communications are delivered to the intended partner recipient?
