300-720 Cisco Securing Email with Cisco Email Security Appliance (300-720 SESA) Free Practice Exam Questions (2026 Updated)
Prepare effectively for your Cisco 300-720 Securing Email with Cisco Email Security Appliance (300-720 SESA) certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
An engineer must configure Directory Harvest Attack Prevention for SMTP in Cisco Secure Email Gateway. This error message must be sent when the listener receives more than 50 invalid
recipients per hour.
•500 - Too many requests
•Max. Invalid Recipients Per Hour was set to 50 already.
Which two actions must be taken next to set maximum invalid recipients per hour to meet the requirement? (Choose two.)
A network administrator notices that there are a high number of queries to the LDAP server. The mail logs show an entry “550 Too many invalid recipients | Connection closed by foreign host.”
Which feature must be used to address this?
What is the purpose of checking the CRL during SMTP authentication on a Cisco Secure Email Gateway?
A network engineer is reviewing the record presented.

Which type of DNS record would contain the record as per the DKIM public key RFC 6376?
An engineer must configure Cisco Secure Email Gateway to scan all email from the HR department for viruses. The Sophos scanning engine must be used, and messages that potentially
still contain viruses after repair must be quarantined. These configurations were performed already:
•Enable antivirus scanning on the email gateway.
•Create a mail policy for the HR department.
Which two actions must be taken to complete the configuration? (Choose two.)
What are two prerequisites for implementing undesirable URL protection in Cisco ESA? (Choose two.)
A list of company executives is routinely being spoofed, which puts the company at risk of malicious email attacks An administrator must ensure that executive messages are originating from legitimate sending addresses Which two steps must be taken to accomplish this task? (Choose two.)
An organization wants to use DMARC to improve its brand reputation by leveraging DNS records.
Which two email authentica tion mechanisms are utilized during this process? (Choose two.)
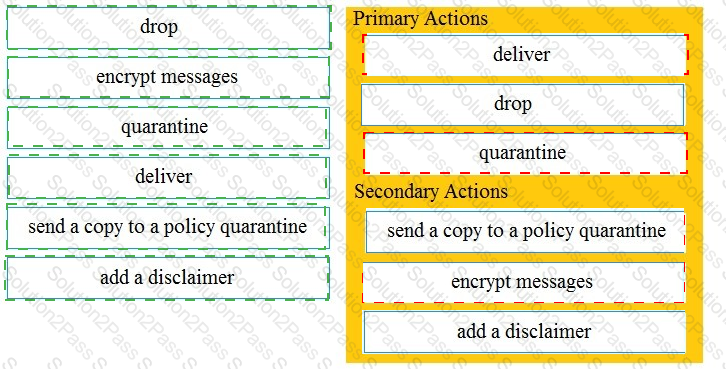
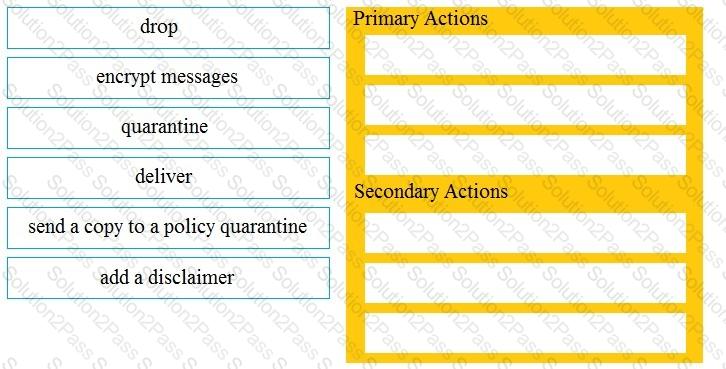
Drag and drop the Cisco ESA reactions to a possible DLP from the left onto the correct action types on the right.
Which action must be taken before a custom quarantine that is being used can be deleted?
Which cloud service provides a reputation verdict for email messages based on the sender domain and other attributes?
To comply with a recent audit, an engineer must configure anti-virus message handling options on the incoming mail policies to attach warnings to the subject of an email.
What should be configured to meet this requirement for known viral emails?
Which process is skipped when an email is received from safedomain.com, which is on the safelist?
Which two features of Cisco Email Security are added to a Sender Group to protect an organization against email threats? (Choose two.)
Refer to the exhibit.
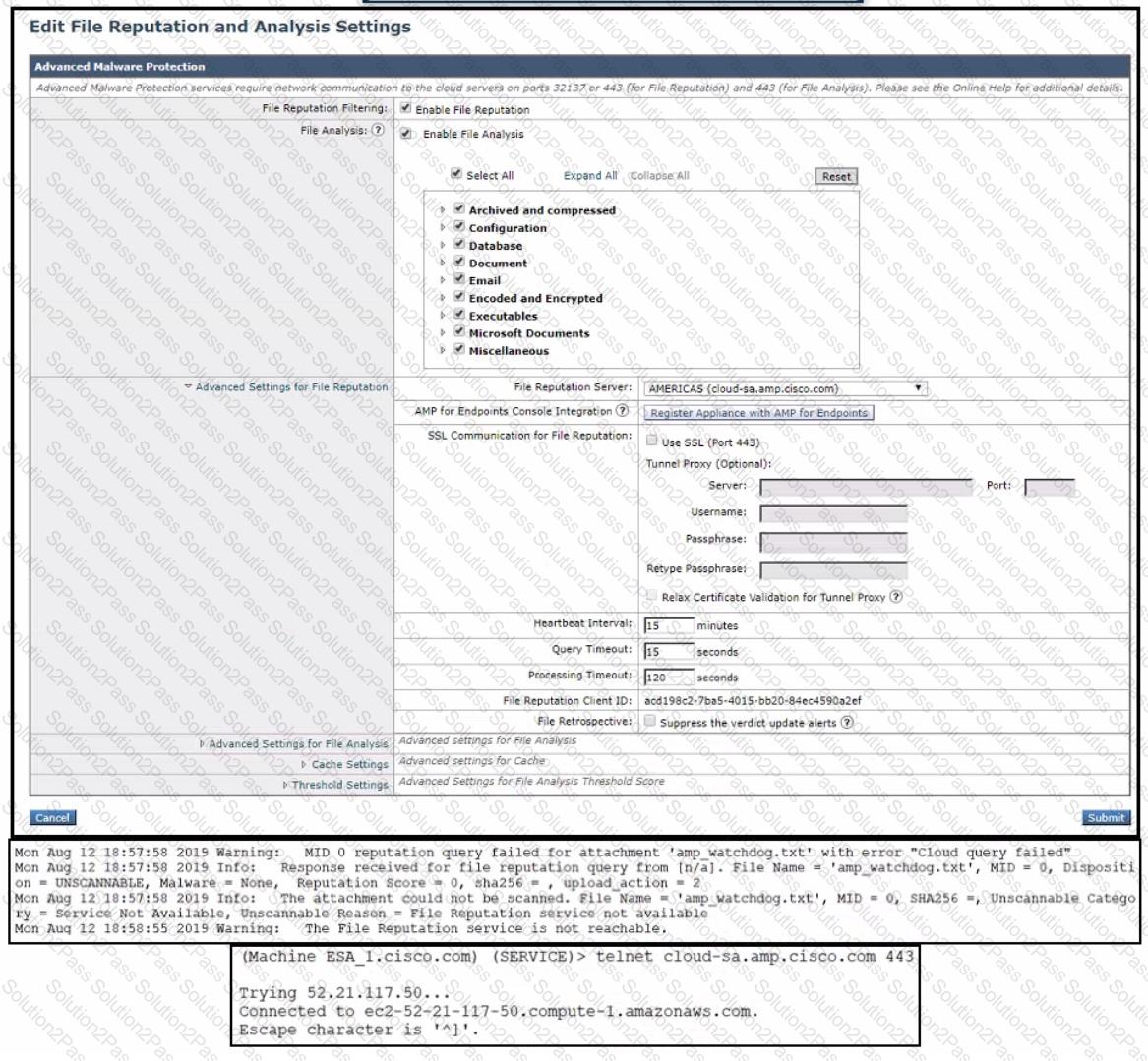
An administrator has configured File Reputation and File Analysis on the Cisco Secure Email Gateway appliance however it does not function as expected What must be configured on the appliance for this to function?
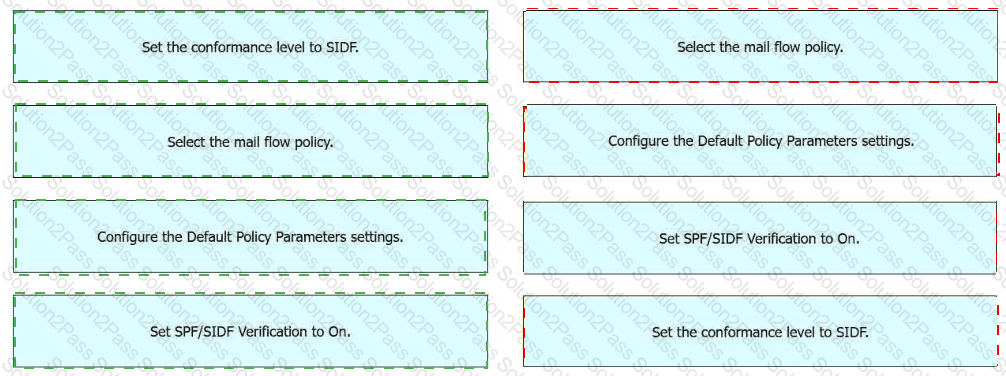
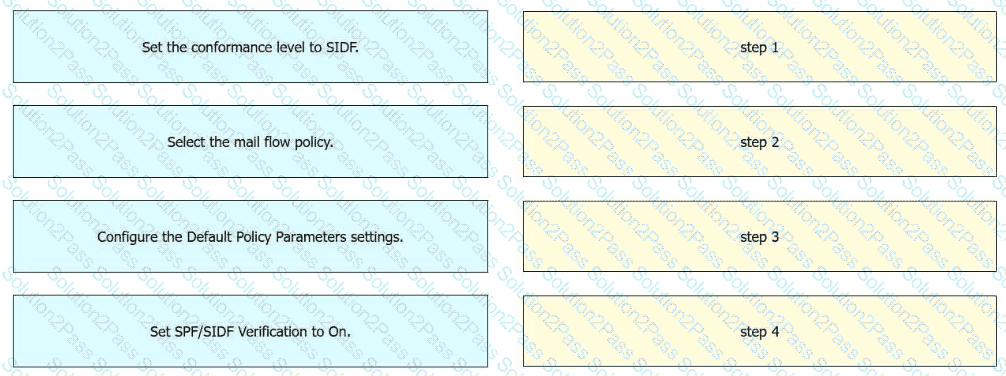
An engineer must enable SIDF for a mail flow policy on an incoming listener in Cisco Secure Email Gateway. Drag and drop the actions from the left into the sequence on the right to meet the requirement.
An organization has multiple Cisco Secure Email Gateway appliances deployed, resulting in several spam quarantines to manage. To manage the quarantined messages, the administrator enabled the centralized spam quarantine on the Cisco Secure Email and Web Manager appliance and configured the external spam quarantine on the Cisco Secure Email Gateway appliances. However, messages are still being directed to the local quarantine on the Cisco Secure Email Gateway appliances What change is necessary to complete the configuration?