300-720 Cisco Securing Email with Cisco Email Security Appliance (300-720 SESA) Free Practice Exam Questions (2026 Updated)
Prepare effectively for your Cisco 300-720 Securing Email with Cisco Email Security Appliance (300-720 SESA) certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
When the Cisco ESA is configured to perform antivirus scanning, what is the default timeout value?
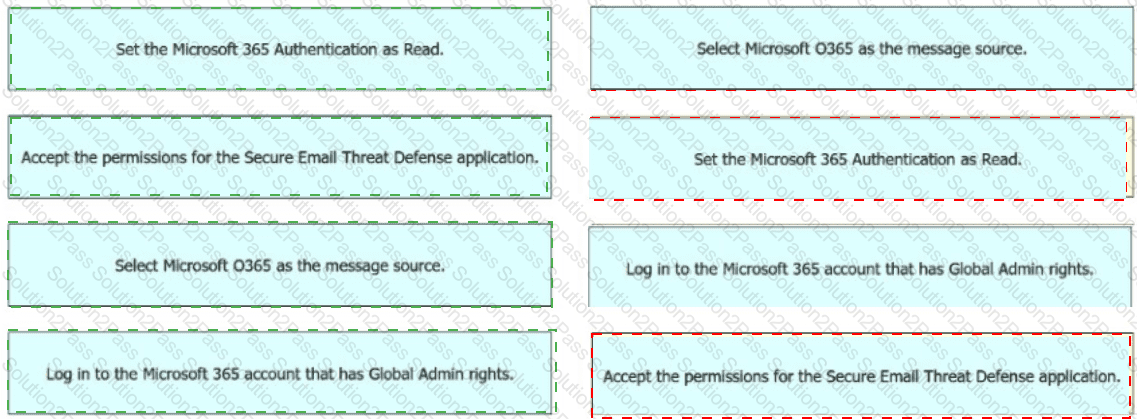
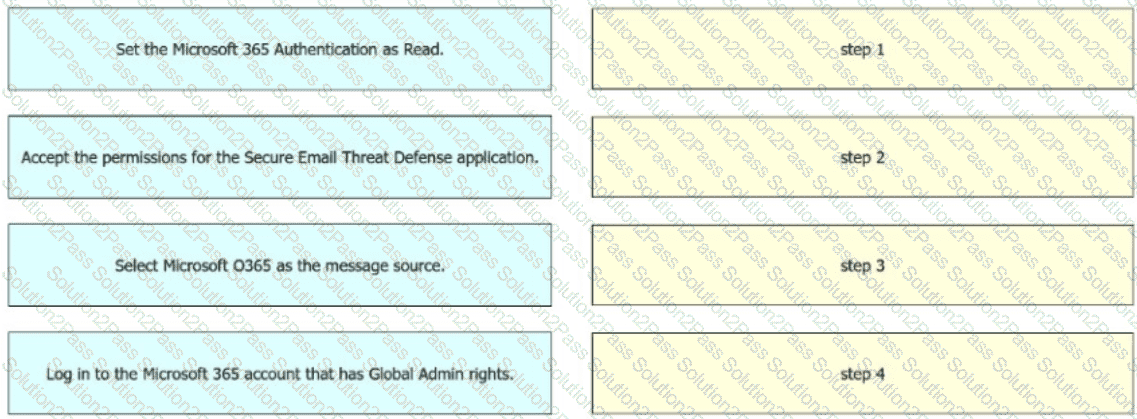
An engineer must configure the message source when integrating Cisco Secure Email Threat Defense with Microsoft 365. The integration must allow visibility but not remediation. Drag and drop the actions from the left into sequence on the right to meet the requirement.
An engineer must add the user1@cisco.co m with an IP address of 10.1.1.13 to a safelist in Cisco Secure Email Gateway. Which two safelist syntaxes must be configured to meet the requirement? (Choose two.)
Which action is allowed while managing list of certificate authorities on Cisco Secure Email Gateway?
What are organizations trying to address when implementing a SPAM quarantine?
The security administrator wants to configure alerts on Cisco Secure Email Gateway for outbreak filters. Which two actions must be taken to meet the requirement? (Choose two.)
An Encryption Profile has been set up on the Cisco ESA.
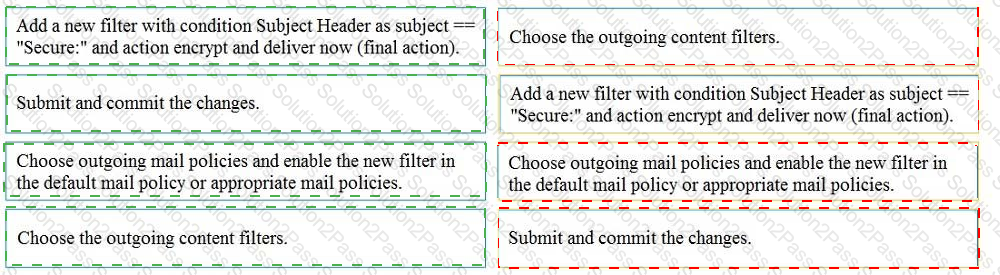
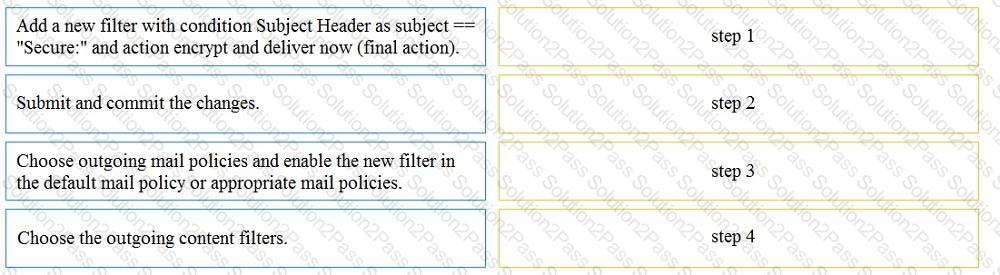
Drag and drop the steps from the left for creating an outgoing content filter to encrypt emails that contains the subject " Secure: " into the correct order on the right.
Which content filter condition checks to see if the " From: header " in the message is similar to any of the users in the content dictionary?
Which predefined DLP category must be used by a network administrator to ensure that a company employee cannot send credit card information outside the company?
A network engineer must tighten up the SPAM control policy of an organization due to a recent SPAM attack. In which scenario does enabling regional scanning improve security for this organization?
Which scenario prevents a message from being sent to the quarantine as an action in the scan behavior on Cisco ESA?
What is a valid content filter action?
When an email is sent with bounce verification enabled, which address is rewritten by the Cisco Secure Email Gateway in the message?
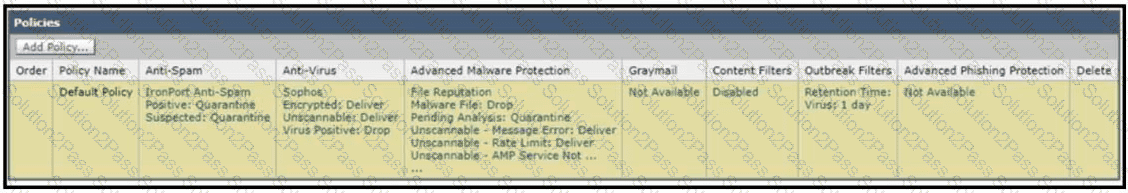
Refer to the exhibit. How does a Cisco Secure Email Gateway handle an email that is identified both as spam positive and outbreak positive by outbreak filters?
An administrator notices that the Cisco Secure Email Gateway delivery queue on an appliance is consistently full. After further investigation, it is determined that the IP addresses currently in use by appliance are being rate-limited by some destinations. The administrator creates a new interface with an additional IP address using virtual gateway technology, but the issue is not solved Which configuration change resolves the issue?
What is needed to sign outbound emails using Domain Keys Identified Mail after a signing profile is created in the Cisco Secure Email Gateway?
What is the maximum message size that can be configured for encryption on the Cisco ESA?
Which two factors must be considered when message filter processing is configured? (Choose two.)
Which feature utilizes sensor information obtained from Talos intelligence to filter email servers connecting into the Cisco ESA?
What is the default behavior of any listener for TLS communication?