350-401 Cisco Implementing Cisco Enterprise Network Core Technologies (350-401 ENCOR) Free Practice Exam Questions (2026 Updated)
Prepare effectively for your Cisco 350-401 Implementing Cisco Enterprise Network Core Technologies (350-401 ENCOR) certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
Which technique is used to protect end user devices and data from unknown file behavior?
When deploying Cisco SD-Access Fabric APs, where does the data plane VXLAN tunnel terminate?
An engineer is reviewing a PCAP file that contains a packet capture of a four-way handshake exchange between a dient and AP using WPA2 Enterprise Which EAPOL message validates and confirms that the client device has successfully Installed the GTK?
Which feature works with SSO to continue forwarding packets after a route processor failure until the control plane recovers?
What is YANG used for?
Which API does Cisco DNA Center use to retrieve information about images?
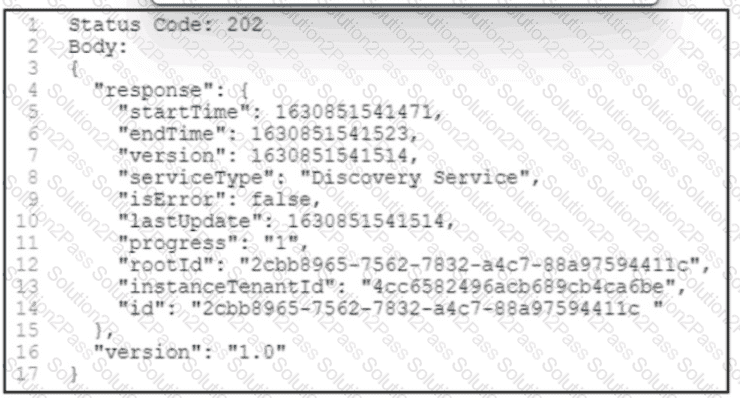
Refer to the exhibit. A POST /discovery request spawns an asynchronous task. After querying for more information about the task, the Cisco DNA Center platform returns the REST API response. What is the status of the discovery task?
What does the statement print(format(0.8, \0%')) display?
Which solution simplifies management of secure access to network resources?
What is a characteristic of VRRP?
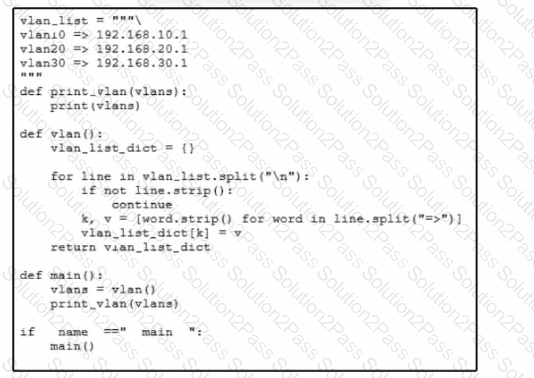
Refer to the exhibit A network engineer must use a Python script lo convert data received from a network device. Which type of data is printed to the console when the script runs?
Which controller is the single plane of management for Cisco SD-WAN?