400-007 Cisco Certified Design Expert (CCDE v3.1) Free Practice Exam Questions (2026 Updated)
Prepare effectively for your Cisco 400-007 Cisco Certified Design Expert (CCDE v3.1) certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
Company XYZ has implemented policy-based routing in their network. Which potential problem must be kept in mind about network reconvergence and PBR?
Which CIA triad principle is used by social media platforms to constitute a standard procedure of user IDs and passwords requirements?
A network hacker is trying to interrupt the transport packet on IPsec. A packet with duplicate sequence numbers is introduced. The customer sends high-priority traffic during this window. Which design parameter should be considered to mitigate this issue?
A centralized control plane generally means one or more controllers gather the reachability and topology information from each switching device and calculate some part of the forwarding information at some place. How can a centralized control plane be defined or described?
An engineer is designing a DMVPN network where OSPF has been chosen as the routing protocol A spoke-to-spoke data propagation model must be set up Which two design considerations must be taken into account ? (Choose two)
While positive feedback loops generally don ' t last long enough to bring down a network completely, they can still last long enough to disrupt traffic flows or to cause the network to converge more slowly than it should.
What are two examples of cases where a positive feedback loop can be long-lived and devastating to the network ' s control plane? (Choose two)
If the desire is to connect virtual network functions together to accommodate different types of
network service connectivity, what must be deployed?
In an OSPF network with routers connected together with Ethernet cabling, which topology typically takes the longest to converge?
A communication network failure is usually defined as a situation where the network is unable to deliver communication services Thus a failure can be viewed as a disruption of service rather than degradation due to congestion One of the survivability techniques for improving network resilience is traffic management Which network-level traffic management and restoration technique can be used to achieve this?
A network automation team plans to develop tasks to configure services on a network by using a Python controller The configuration tasks must be implemented by using operations that support network-wide transactions The candidate configuration must be validated automatically for all targeted devices before being applied to each specific device What can be used to apply the configuration to the network devices?
Which development model is closely associated with Agile project management?
What are two primary design constraints when a robust infrastructure solution is created? (Choose two.)
What is a characteristic of a secure cloud architecture model?
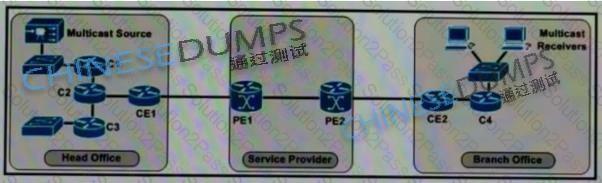
Refer to the exhibit. The enterprise customer wants to stream one-way video from their head office to eight branch offices using multicast. Their current service provider provides a Layer3 VPN solution and manages the CE routers, but they do not currently support multicast. Which solution quickly allows this multicast traffic to go through while allowing for future scalability?
Agile and Waterfall are two popular methods for organizing projects What describes any Agile network design development process?
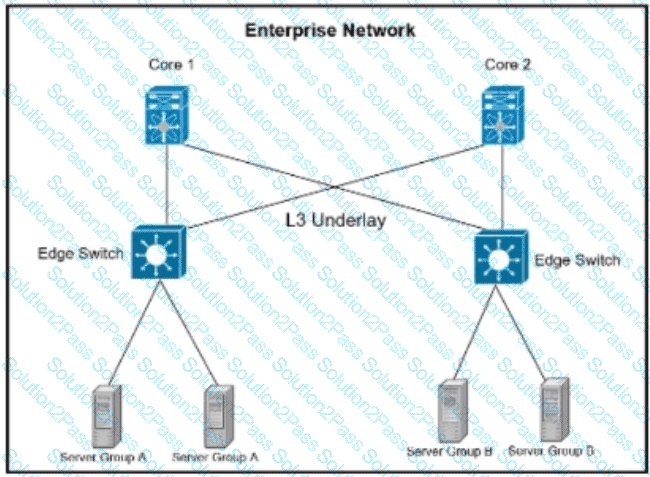
Refer to the exhibit. A company is running their data center based on VXLAN and BGP EVPN with stretched subnets for servers attaching to the edge devices being an important feature. The security team has defined a requirement where server group A must not be able to communicate with each other but is allowed to communicate with server group B. while servers in Group B must be able to communicate with all servers. Which scalable solution can be deployed to support these requirements?
Company XYZ wants to redesign the Layer 2 part of their network and wants to use all available uplinks for increased performance They also want to have end host reachability supporting conversational learning However, due to design constraints, they cannot implement port-channel on the uplinks Which other technique can be used to make sure the uplinks are in active/active state?
As a service provider is implementing Strong Access Control Measures, which two of the following PCI Data Security Standard requirements must be met? (Choose two . )
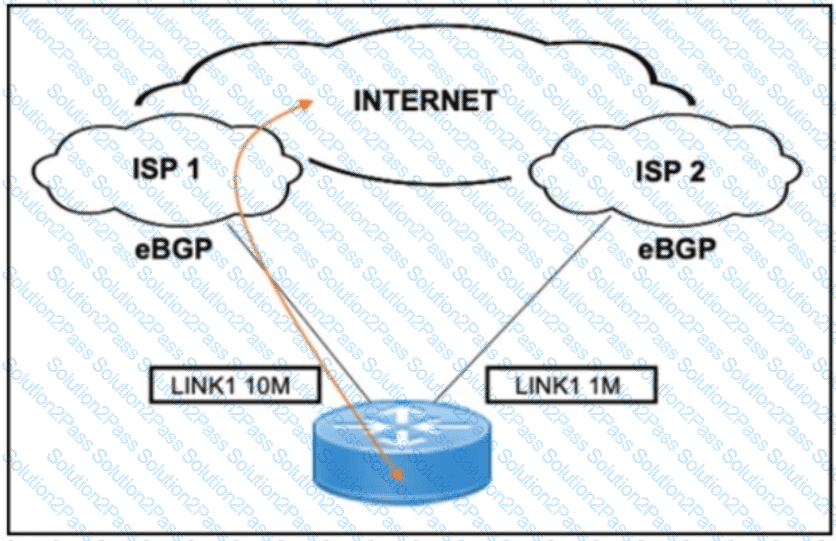
Refer to the exhibit. A customer needs to implement a connectivity model by using one active link for inbound and outbound traffic and a second link for backup. The backup link is low speed and is required only during outages of the primary link. Which design solution should be implemented?
A multinational corporation intends to deploy Al/ML-driven analytics for consumer data The company operates in multiple locations, including the EU, where data protection regulations are rigorous The organization must guarantee that its Al/ML solution adheres to local regulations, especially with data storage and processing
Which cloud environment will most effectively meet the company’s data sovereignty needs while assuring adherence to regional data protection regulations?
