CAS-005 CompTIA SecurityX Certification Exam Free Practice Exam Questions (2026 Updated)
Prepare effectively for your CompTIA CAS-005 CompTIA SecurityX Certification Exam certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
While investigating an email server that crashed, an analyst reviews the following log files:
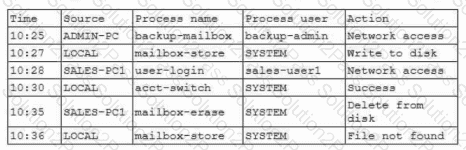
Which of the following is most likely the root cause?
A security architect wants to develop abaseline of security configurations These configurations automatically will be utilized machine is created Which of the following technologies should the security architect deploy to accomplish this goal?
All organization is concerned about insider threats from employees who have individual access to encrypted material. Which of the following techniques best addresses this issue?
Company A and Company D ate merging Company A ' s compliance reports indicate branchprotections are not in place A security analyst needs to ensure that potential threats to the software development life cycle are addressed. Which of the following should me analyst cons < der when completing this basic?
A user tried to access a web page at http://10.1.1.1. Previously the web page did not require authentication, and now the browser is prompting for credentials. Which of the following actions would best prevent the issue from reoccurring and reduce the likelihood of credential exposure?
The ISAC for the retail industry recently released a report regarding social engineering tactics in which small groups create distractions for employees while other malicious individuals install advanced card skimmers on the payment systems. The Chief Information Security Officer (CISO) thinks that security awareness training, technical control implementations, and governance already in place is adequate to protect from this threat. The board would like to test these controls. Which of the following should the CISO recommend?
Which of the following AI concerns is most adequately addressed by input sanitation?
A network engineer must ensure that always-on VPN access is enabled Curt restricted to company assets Which of the following best describes what the engineer needs to do ' '
A security engineer wants to propose an MDM solution to mitigate certain risks. The MDM solution should meet the following requirements:
• Mobile devices should be disabled if they leave the trusted zone.
• If the mobile device is lost, data is not accessible.
Which of the following options should the security engineer enable on the MDM solution? (Select two).
An attacker infiltrated the code base of a hardware manufacturer and inserted malware before the code was compiled. The malicious code is now running at the hardware level across a number of industries and sectors. Which of the following categories best describes this type of vendor risk?
A central bank implements strict risk mitigations for the hardware supply chain, including an allow list for specific countries of origin. Which of the following best describes the cyberthreat to the bank?
Engineers at a cloud service provider can now access newly deployed customer environments from their personal laptops. The engineers are concerned that unmanaged systems may present unknown vulnerabilities to customer environments, which might become a significant liability to the service provider. Which of the following deployments provides the most secure solution to prevent access through non-authorized endpoints?
A building camera is remotely accessed and disabled from the remote console application during off-hours. A security analyst reviews the following logs:
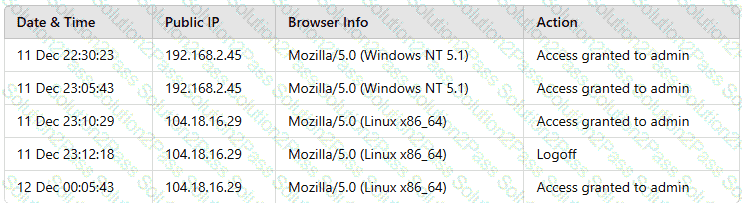
Which of the following actions should the analyst take to best mitigate the threat?
The material finding from a recent compliance audit indicate a company has an issue with excessive permissions. The findings show that employees changing roles or departments results in privilege creep. Which of the following solutions are the best ways to mitigate this issue? (Select two).
Setting different access controls defined by business area
A security analyst is reviewing the following log:
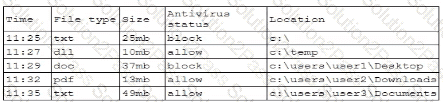
Which of the following possible events should the security analyst investigate further?
A developer receives feedback about code quality and efficiency. The developer needs to identify and resolve the following coding issues before submitting the code changes for peer review:
Indexing beyond arrays
Dereferencing null pointers
Potentially dangerous data type combinations
Unreachable code
Non-portable constructs
Which of the following would be most appropriate for the developer to use in this situation?
A global company’s Chief Financial Officer (CFO) receives a phone call from someone claiming to be the Chief Executive Officer (CEO). The caller claims to be stranded and in desperate need of money. The CFO is suspicious, but the caller’s voice sounds similar to the CEO’s. Which of the following best describes this type of attack?
A company implemented a NIDS and a NIPS on the most critical environments. Since this implementation, the company has been experiencing network connectivity issues. Which of the following should the security architect recommend for a new NIDS/NIPS implementation?
A security engineer reviews an after action report from a previous security breach and notes a long lag time between detection and containment of a compromised account. The engineer suggests using SOAR to address this concern. Which of the following best explains the engineer ' s goal?
A software engineer is creating a CI/CD pipeline to support the development of a web application The DevSecOps team is required to identify syntax errors Which of the following is the most relevant to the DevSecOps team ' s task '
