CV0-004 CompTIA Cloud+ (V4) Free Practice Exam Questions (2026 Updated)
Prepare effectively for your CompTIA CV0-004 CompTIA Cloud+ (V4) certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
A systems administrator notices a surge of network traffic is coming from the monitoring server. The administrator discovers that large amounts of data are being downloaded to an external source. While investigating, the administrator reviews the following logs:
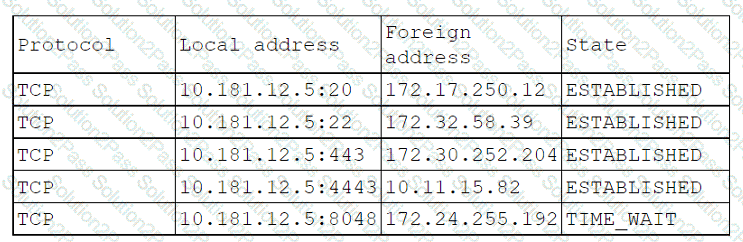
Which of the following ports has been compromised?
Which of the following facilitates the continuous deployment of cloud applications without performing a clean install on each iteration?
A cloud engineer hardened the WAF for a company that operates exclusively in North America. The engineer did not make changes to any ports, and all protected applications have
continued to function as expected. Which of the following configuration changes did the engineer most likely apply?
The company's IDS has reported an anomaly. The cloud engineer remotely accesses the cloud instance, runs a command, and receives the following information:
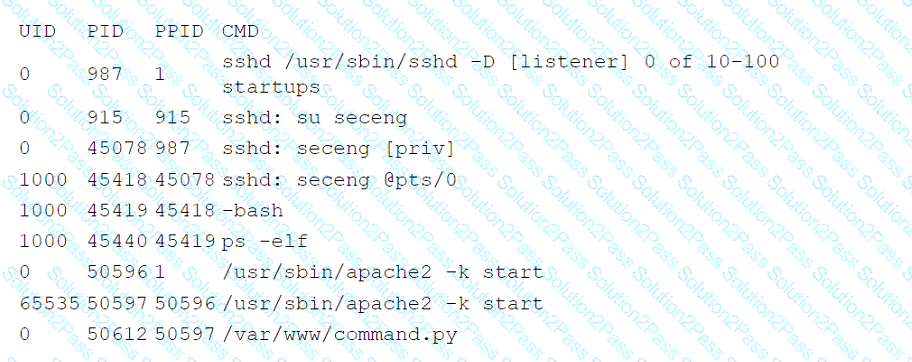
Which of the following is the most likely root cause of this anomaly?
A company has ten cloud engineers working on different manual cloud deployments. In the past, engineers have had difficulty keeping deployments consistent. Which of the following is the best method to address this issue?
Which of the following interfaces is most commonly used for SSDs but not for HDDs?
A systems engineer is migrating a batch of 25 VMs from an on-premises compute cluster to a public cloud using the public cloud's migration agent. The migration job shows data
copies at a rate of 250Mbps. After five servers migrate, the data copies at a rate of 25Mbps. Which of the following should the engineer review first to troubleshoot?
Following a ransomware attack, the legal department at a company instructs the IT administrator to store the data from the affected virtual machines for a minimum of one year.
Which of the following is this an example of?
A company recently migrated to a public cloud provider. The company's computer incident response team needs to configure native cloud services tor detailed logging. Which of the following should the team implement on each cloud service to support root cause analysis of past events? {Select two).
A government agency in the public sector is considering a migration from on premises to the cloud. Which of the following are the most important considerations for this cloud migration? (Select two).
A cloud service provider requires users to migrate to a new type of VM within three months. Which of the following is the best justification for this requirement?
A company has decided to adopt a microservices architecture for its applications that are deployed to the cloud. Which of the following is a major advantage of this type of architecture?
A company wants to create a few additional VDIs so support vendors and contractors have a secure method to access the company's cloud environment. When a cloud
administrator attempts to create the additional instances in the new locations, the operation is successful in some locations but fails in others. Which of the following is the
most likely reason for this failure?
A junior cloud administrator was recently promoted to cloud administrator and has been added to the cloud administrator group. The cloud administrator group is the only one that can access the engineering VM. The new administrator unsuccessfully attempts to access the engineering VM. However, the other administrators can access it without issue. Which of the following is the best way to identify the root cause?
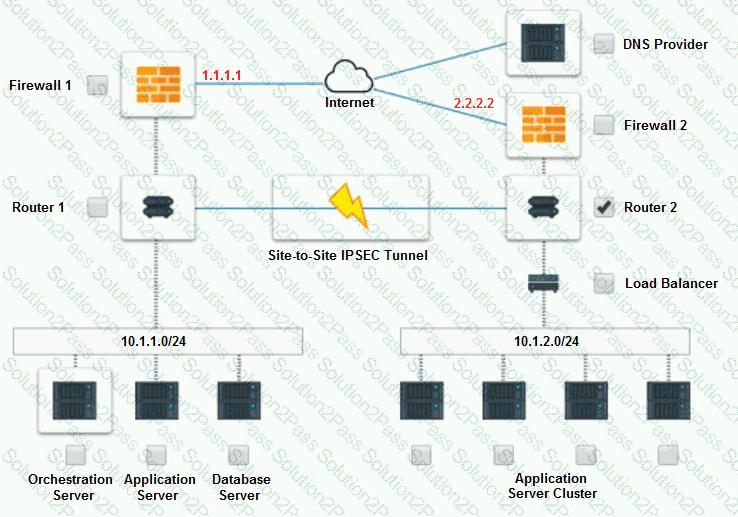
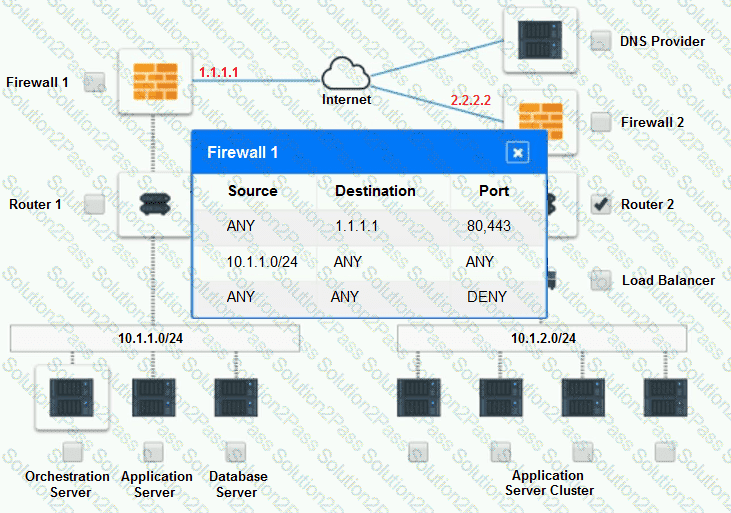
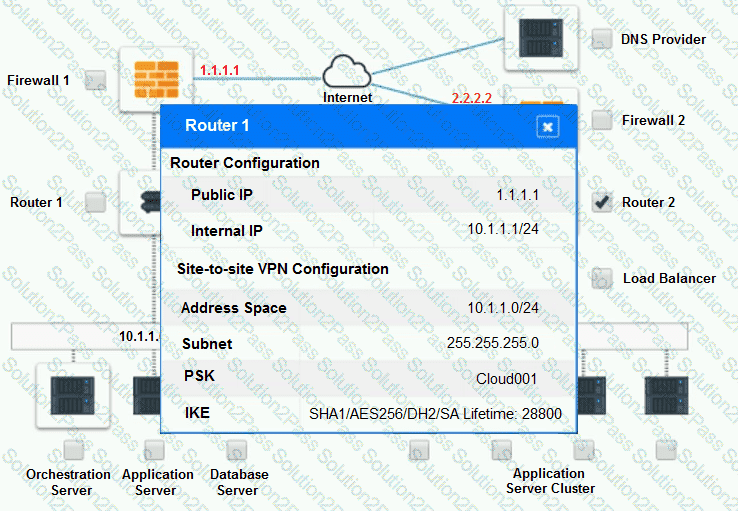
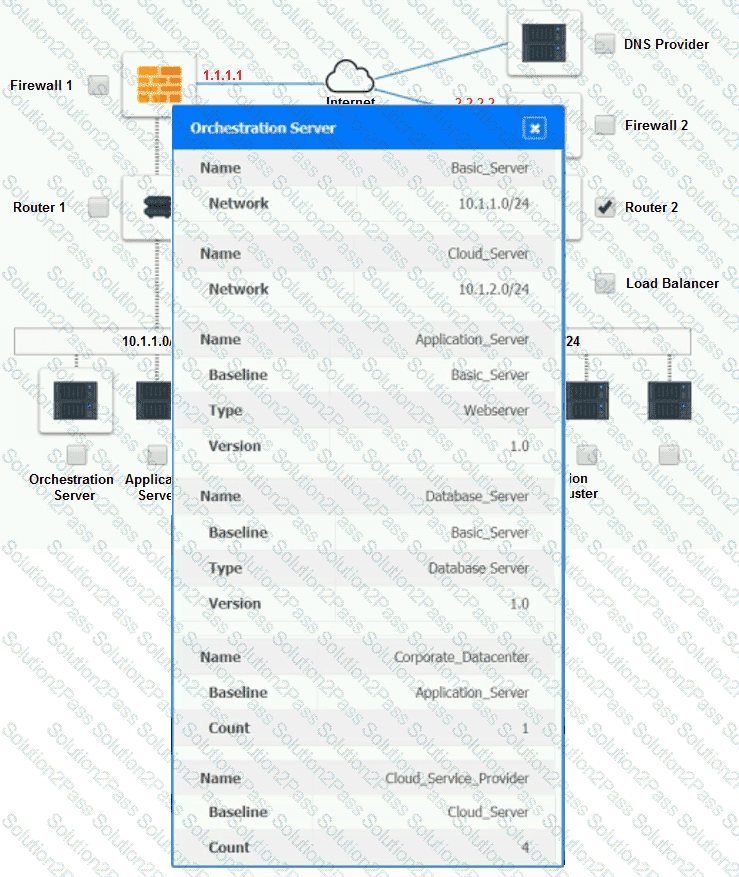
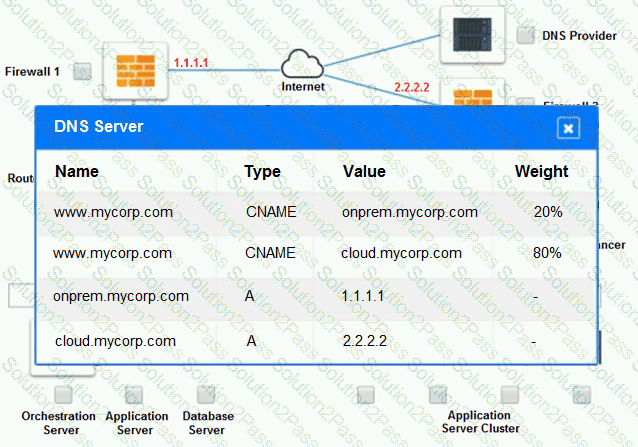
A company has decided to scale its e-commerce application from its corporate datacenter to a commercial cloud provider to meet an anticipated increase in demand during an upcoming holiday.
The majority of the application load takes place on the application server under normal conditions. For this reason, the company decides to deploy additional application servers into a commercial cloud provider using the on-premises orchestration engine that installs and configures common software and network configurations.
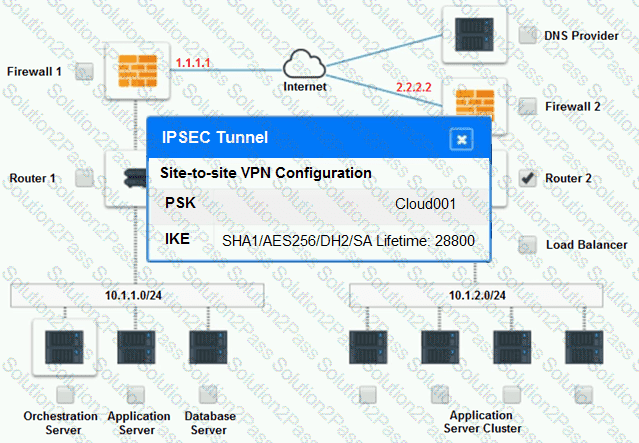
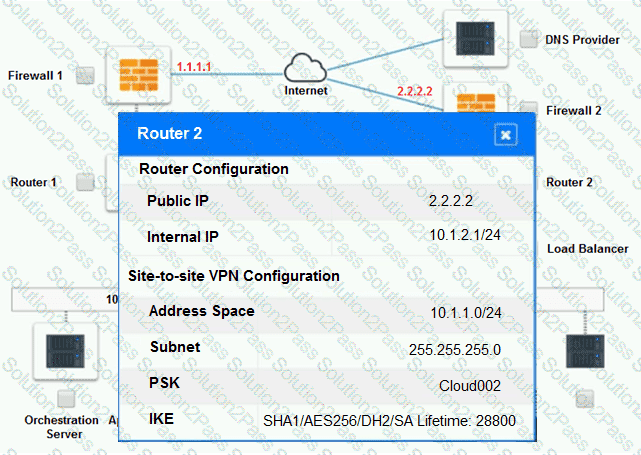
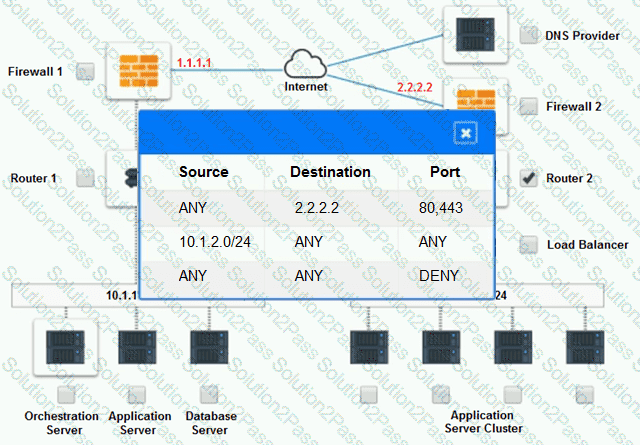
The remote computing environment is connected to the on-premises datacenter via a site-to-site IPSec tunnel. The external DNS provider has been configured to use weighted round-robin routing to load balance connections from the Internet.
During testing, the company discovers that only 20% of connections completed successfully.
INSTRUCTIONS
Review the network architecture and supporting documents and fulfill these requirements:
Part 1:
 Analyze the configuration of the following components: DNS, Firewall 1, Firewall 2, Router 1, Router 2, VPN and Orchestrator Server.
Analyze the configuration of the following components: DNS, Firewall 1, Firewall 2, Router 1, Router 2, VPN and Orchestrator Server.
 Identify the problematic device(s).
Identify the problematic device(s).
Part 2:
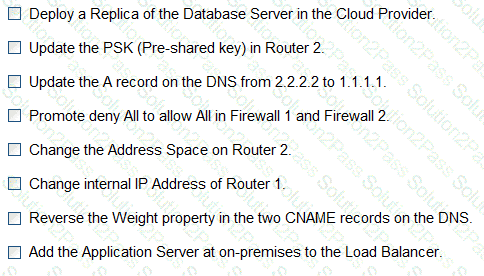
 Identify the correct options to provide adequate configuration for hybrid cloud architecture.
Identify the correct options to provide adequate configuration for hybrid cloud architecture.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
Part 1:
Cloud Hybrid Network Diagram
Part 2:
Only select a maximum of TWO options from the multiple choice question
A cloud engineer wants to replace the current on-premises. unstructured data storage with a solution in the cloud. The new solution needs to be cost-effective and highly scalable. Which of the following types of storage would be best to use?
Which of the following service options would provide the best availability for critical applications in the event of a disaster?
A security engineer recently discovered a vulnerability in the operating system of the company VMs. The operations team reviews the issue and decides all VMs need to be updated
from version 3.4.0 to 3.5. Which of the following best describes the type of update that will be applied?
A company is required to save historical data for seven years. A cloud administrator implements a script that automatically deletes data older than seven years. Which of the following concepts best describes why the historical data is being deleted?
Which of the following is true of SSDs?
