CV0-004 CompTIA Cloud+ (V4) Free Practice Exam Questions (2026 Updated)
Prepare effectively for your CompTIA CV0-004 CompTIA Cloud+ (V4) certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
The change control board received a request to approve a configuration change 10 deploy in the cloud production environment. Which of the following should have already been competed?
Which of the following is a protocol frequently used with IoT devices to communicate with a gateway?
Which of the following is a direct effect of cloud migration on an enterprise?
A network administrator is budding a site-to-site VPN tunnel from the company's headquarters office 10 the company's public cloud development network. The network administrator confirms the following:
The VPN tunnel is established on the headquarter office firewall.
While inside the office, developers report that they cannot connect to the development network resources.
While outside the office on a client VPN, developers report that they can connect to the development network resources.
The office and the client VPN have different IP subnet ranges.
The firewall flow logs show VPN traffic is reaching the development network from the office.
Which of the following is the next step the next network administrator should take to troubleshoot the VPN tunnel?
A company wants to optimize cloud resources and lower the overhead caused by managing multiple operating systems. Which of the following compute resources would be best to help to achieve this goal?
A cloud architect is preparing environments to develop a new application that will process sensitive data. The project team consists of one internal developer, two external consultants, and three testers. Which of the following is the most important security control for the cloud architect to consider implementing?
A cross-site request forgery vulnerability exploited a web application that was hosted in a public laaS network. A security engineer determined that deploying a WAF in blocking mode at a CDN would prevent the application from being exploited again. However, a week after implementing the WAF, the application was exploited again. Which of the following should the security engineer do to make the WAF control effective?
A cloud administrator is working on the deployment of an e-commerce website. The administrator evaluates the scaling methods to be implemented when seasonal or flash sales are launched. Which of the following scaling approaches should the administrator use to best manage this scenario?
A company uses containers stored in Docker Hub to deploy workloads (or its laaS infrastructure. The development team releases changes to the containers several times per hour. Which of the following should a cloud engineer do to prevent the proprietary code from being exposed to third parties?
A DevOps engineer is integrating multiple systems. Each system has its own API that exchanges data based on different application-level transactions. Which of the following
delivery mechanisms would best support this integration?
A systems administrator needs to configure backups for the company's on-premises VM cluster. The storage used for backups will be constrained on free space until the company
can implement cloud backups. Which of the following backup types will save the most space, assuming the frequency of backups is kept the same?
A company wants to build its new platform using a public cloud. The workload requirements include the following:
• Implementation of custom CIS compliance
• Patch for vulnerabilities within 24 hours
• Warrant at least 1,800 IOPS per volume
Which of the following meets the requirements?
A company's VMs that are created using the noncritical application tag are automatically shut down at 5:00 p.m. using a cronjob. Which of the following actions would allow a cloud engineer to stop all unresponsive instances with the least effort in case the automation fails?
The performance of an e-commerce website decreases dramatically during random periods. The IT team is evaluating available resources to mitigate the situation. Which of the following is the best approach to effectively manage this scenario'?
A cloud engineer is collecting web server application logs to troubleshoot intermittent issues. However, the logs are piling up and causing storage issues. Which of the following log
mechanisms should the cloud engineer implement to address this issue?
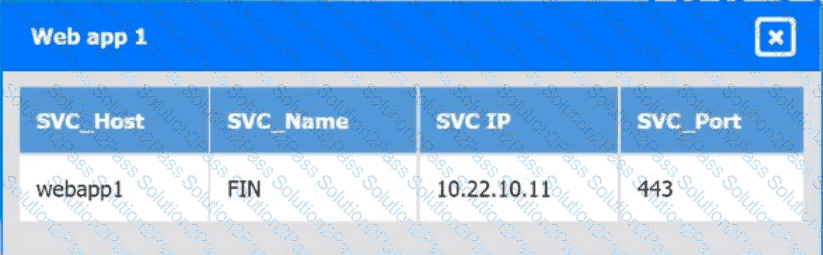
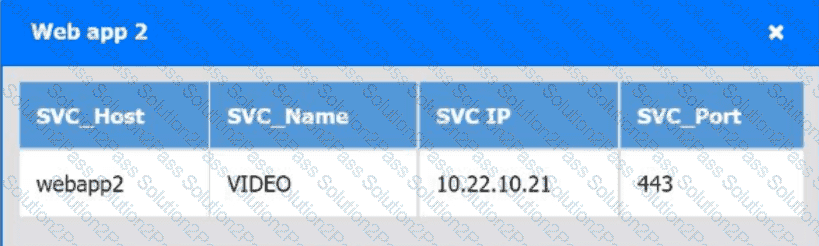
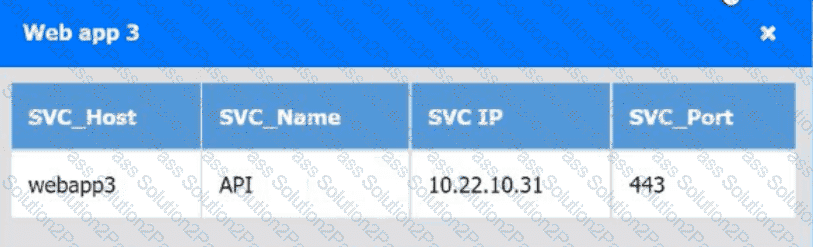
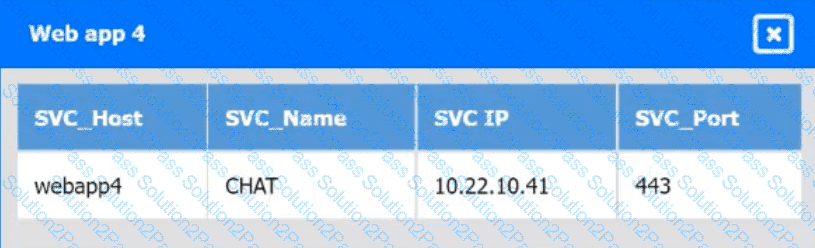
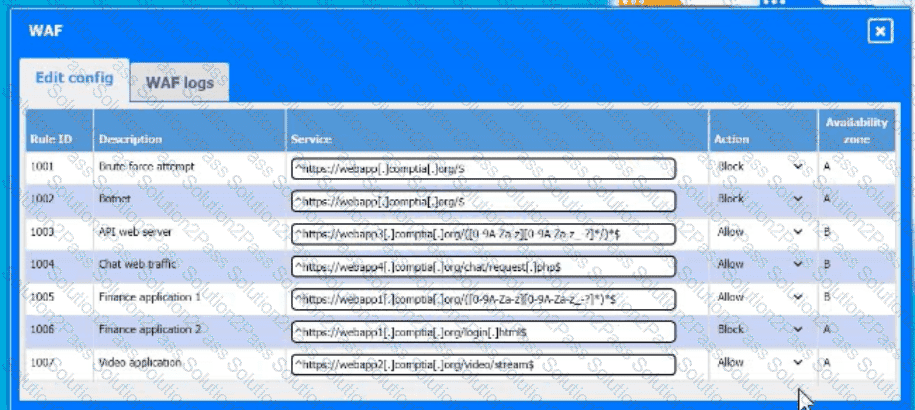
A company hosts various containerized applications for business uses. A client reports that one of its routine business applications fails to load the web-based login prompt hosted in the company cloud.
Click on each device and resource. Review the configurations, logs, and characteristics of each node in the architecture to diagnose the issue. Then, make the necessary changes to the WAF configuration to remediate the issue.
Which of the following is a customer be responsible for in a provider-managed database service? (Select two).
Given the following command:
Sdocker pull images.comptia.org/user1/myimage:latest
Which of the following correctly identifies images.comptia.org?
A software engineer is integrating an application lo The cloud that is web socket based. Which of the following applications is the engineer most likely deploying?
Which of the following best explains the concept of migrating from on premises to the cloud?
