CV0-004 CompTIA Cloud+ (V4) Free Practice Exam Questions (2026 Updated)
Prepare effectively for your CompTIA CV0-004 CompTIA Cloud+ (V4) certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
An on-premises data center is located in an earthquake-prone location. The workload consists of real-time, online transaction processing. Which ot the following data protection strategies should be used to back up on-premises data to the cloud while also being cost effective?
Five thousand employees always access the company's public cloud-hosted web application on a daily basis during the same time frame. Some users have been reporting performance issues while attempting to connect to the web application Which of the following is the best configuration approach to resolve this issue?
A software development team must manage changes to source code for different clients who utilize the same product with different features. Which of the following meets this requirement?
A developer is building a new application version using a CI/CD pipeline. The developer receives the following error message log when the build fails:
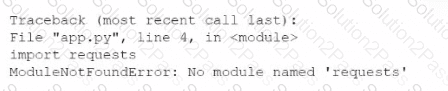
Which of the following is the most likely cause of this failure?
Which of the following describes the main difference between public and private container repositories?
An IT manager is migrating the production environment to the cloud but needs to keep control of the operating systems, patches, and settings of all resources. Which of the following deployment models will best meet the requirements?
A cloud engineer is deploying a cloud solution that will be used on premises with need-to-know access. Which of the following cloud deployment models best meets this
requirement?
Which of the following cloud-native architecture designs is the most easily maintained, decentralized, and decoupled?
A cloud engineer needs to determine a scaling approach for a payroll-processing solution that runs on a biweekly basis. Given the complexity of the process, the deployment to each
new VM takes about 25 minutes to get ready. Which of the following would be the best strategy?
A cloud engineer is concerned about command-and-control (C2) communication out of a cloud network over HTTPS. Which of the following should the cloud engineer implement to most efficiently identify the type of communication?
A cloud architect attempts to modify a protected branch but is unable to do so. The architect receives an error indicating the action cannot be completed. Which of the following should the architect try instead''
A cloud engineer creates an IaC repository to deploy an application to a specific region. The cloud engineer receives a new request to deploy the same application to ten different regions. Which of the following options best fulfills this new request?
A company migrated its CRM system to a SaaS solution. The security team is updating the RAG matrix for the newly migrated CRM. Given the following table:
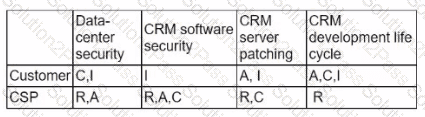
Which of the following responsibility assignments best aligns with the shared responsibility model for the new CRM?
A company serves customers globally from its website hosted in North America. A cloud engineer recently deployed new instances of the website in the Europe region. Which of the
following is the most likely reason?
An organization has been using an old version of an Apache Log4j software component in its critical software application. Which of the following should the organization use to
calculate the severity of the risk from using this component?
A company's website suddenly crashed. A cloud engineer investigates the following logs:
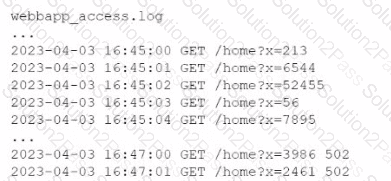
Which of the following is the most likely cause of the issue?
