SY0-701 CompTIA Security+ Exam 2026 Free Practice Exam Questions (2026 Updated)
Prepare effectively for your CompTIA SY0-701 CompTIA Security+ Exam 2026 certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
A company is developing a business continuity strategy and needs to determine how many staff members would be required to sustain the business in the case of a disruption. Which of the following best describes this step?
While a user reviews their email, a host gets infected by malware from an external hard drive plugged into the host. The malware steals all the user ' s credentials stored in the browser. Which of the following training topics should the user review to prevent this situation from reoccurring?
A security analyst reviews domain activity logs and notices the following:
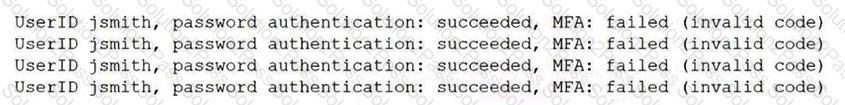
Which of the following is the best explanation for what the security analyst has discovered?
Various stakeholders are meeting to discuss their hypothetical roles and responsibilities in a specific situation, such as a security incident or major disaster. Which of the following best describes this meeting?
While reviewing logs, a security administrator identifies the following code:
< script > function(send_info) < /script >
Which of the following best describes the vulnerability being exploited?
A security analyst estimates that a small security incident will cost $10,000 and will occur twice per year. The analyst recommends a budget of $20,000 for next year. Which of the following does the $10,000 represent?
Which of the following is a social engineering attack in which a bad actor impersonates a web URL?
A security analyst sees the following entries in web server logs:
200.17.88.121 [05/May/2025:01:05:18 -0200] " GET /aboutus.htm " 200 3344
200.17.88.121 [05/May/2025:01:08:22 -0200] " GET /corporateOrg.htm " 200 4200
132.18.62.144 [05/May/2025:01:08:23 -0200] " GET /../../vhosts " 403 502
200.17.88.121 [05/May/2025:01:10:33 -0200] " POST /ContactUs.asp " 403 512
118.19.200.55 [05/May/2025:01:10:45 -0200] " POST/search " 200 1212 " SELECT * FROM company WHERE keyword = ' VP
105.86.13.11 [05/May/2025:01:15:45 -0200] " GET /latestContracts.htm " 404 512
Which of the following IP addresses is most likely involved in a malicious attempt?
An employee emailed a new systems administrator a malicious web link and convinced the administrator to change the email server ' s password. The employee used this access to remove the mailboxes of key personnel. Which of the following security awareness concepts would help prevent this threat in the future?
An organization recently updated its security policy to include the following statement:
Regular expressions are included in source code to remove special characters such as $, |, ;. & , `, and ? from variables set by forms in a web application.
Which of the following best explains the security technique the organization adopted by making this addition to the policy?
Which of the following vulnerabilities is exploited when an attacker overwrites a register with a malicious address?
Several employees received a fraudulent text message from someone claiming to be the Chief Executive Officer (CEO). The message stated:
“I’m in an airport right now with no access to email. I need you to buy gift cards for employee recognition awards. Please send the gift cards to following email address.”
Which of the following are the best responses to this situation? (Choose two).
A financial institution would like to store its customer data m the cloud but still allow the data to be accessed and manipulated while encrypted. Doing so would prevent the cloud service provider from being able to decipher the data due to its sensitivity. The financial institution Is not concerned about computational overheads and slow speeds. Which of the following cryptographic techniques would best meet the requirement?
An organization experiences a cybersecurity incident involving a command-and-control server. Which of the following logs should be analyzed to identify the impacted host? (Select two).
Which of the following would help ensure a security analyst is able to accurately measure the overall risk to an organization when a new vulnerability is disclosed?
Which of the following aspects of the data management life cycle is most directly impacted by local and international regulations?
A security team receives reports about high latency and complete network unavailability throughout most of the office building. Flow logs from the campus switches show high traffic on TCP 445. Which of the following is most likely the root cause of this incident?
An organization has too many variations of a single operating system and needs to standardize the arrangement prior to pushing the system image to users. Which of the following should the organization implement first?
A company processes a large volume of business-to-business transactions and prioritizes data confidentiality over transaction availability. The company ' s firewall administrator must configure a new hardware-based firewall to replace the current one. Which of the following should the administrator do to best align with the company requirements in case a security event occurs?
Which of the following allows an exploit to go undetected by the operating system?
An administrator installs an SSL certificate on a new system. During testing, errors indicate that the certificate is not trusted. The administrator has verified with the issuing CA and has validated the private key. Which of the following should the administrator check for next?
At the start of a penetration test, the tester checks OSINT resources for information about the client environment. Which of the following types of reconnaissance is the tester performing?
After a recent vulnerability scan, a security engineer needs to harden the routers within the corporate network. Which of the following is the most appropriate to disable?
Which of the following data types relates to data sovereignty?
Which of the following can be used to compromise a system that is running an RTOS?
A security engineer needs to quickly identify a signature from a known malicious file. Which of the following analysis methods would the security engineer most likely use?
An organization failed to account for the right-to-be-forgotten regulations. Which of the following impacts might this action have on the company?
Which of the following describes the reason for using an MDM solution to prevent jailbreaking?
A new corporate policy requires all staff to use multifactor authentication to access company resources. Which of the following can be utilized to set up this form of identity and access management? (Select two)
During a recent log review, an analyst found evidence of successful injection attacks. Which of the following will best address this issue?
