SY0-701 CompTIA Security+ Exam 2026 Free Practice Exam Questions (2026 Updated)
Prepare effectively for your CompTIA SY0-701 CompTIA Security+ Exam 2026 certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
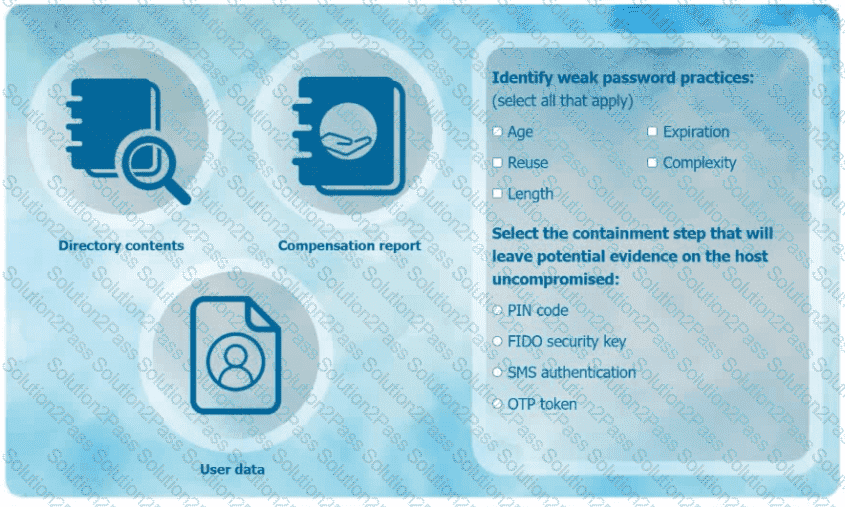
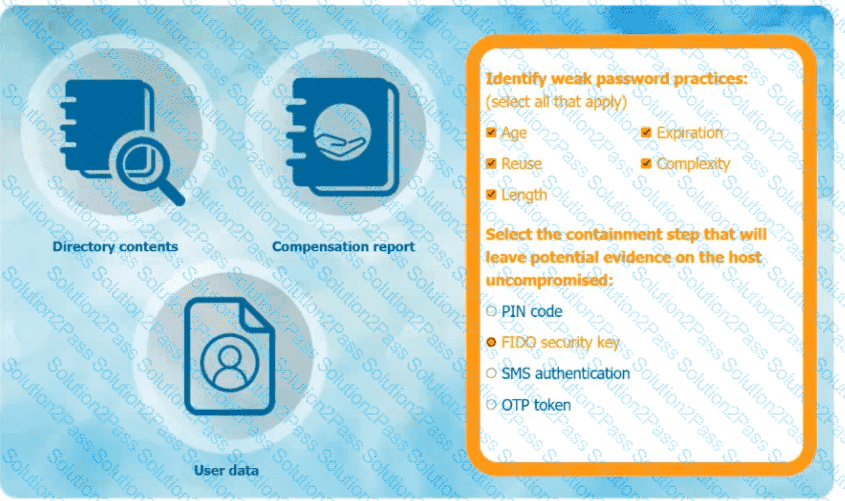
An organization has learned that its data is being exchanged on the dark web. The CIO
has requested that you investigate and implement the most secure solution to protect employee accounts.
INSTRUCTIONS
Review the data to identify weak security practices and provide the most appropriate
security solution to meet the CIO ' s requirements.
Which of the following scenarios describes a possible business email compromise attack?
Which of the following best describes the practice of researching laws and regulations related to information security operations within a specific industry?
Which of the following is the most relevant reason a DPO would develop a data inventory?
An accounting employee recently used software that was not approved by the company. Which of the following risks does this most likely represent?
A company discovers suspicious transactions that were entered into the company ' s database and attached to a user account that was created as a trap for malicious activity. Which of the following is the user account an example of?
The security operations center is researching an event concerning a suspicious IP address A security analyst looks at the following event logs and discovers that a significant portion of the user accounts have experienced faded log-In attempts when authenticating from the same IP address:
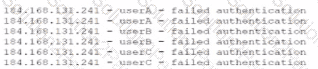
Which of the following most likely describes attack that took place?
An engineer has ensured that the switches are using the latest OS, the servers have the latest patches, and the endpoints ' definitions are up to date. Which of the following will these actions most effectively prevent?
A company suffered a critical incident where 30GB of data was exfiltrated from the corporate network. Which of the following actions is the most efficient way to identify where the system data was exfiltrated from and where it was sent?
A company wants to ensure employees are allowed to copy files from a virtual desktop during the workday but are restricted during non-working hours. Which of the following security measures should the company set up?
Which of the following is the best way to prevent data from being leaked from a secure network that does not need to communicate externally?
Which of the following is a possible consequence of a VM escape?
Which of the following technologies must be used in an organization that intends to automate infrastructure deployment?
A security analyst has determined that a security breach would have a financial impact of $15,000 and is expected to occur twice within a three-year period. Which of the following is the ALE for this risk?
The Cruel Information Security Officer (CISO) asks a security analyst to install an OS update to a production VM that has a 99% uptime SLA. The CISO tells me analyst the installation must be done as quickly as possible. Which of the following courses of action should the security analyst take first?
An engineer needs to find a solution that creates an added layer of security by preventing unauthorized access to internal company resources. Which of the following would be the best solution?
Which of the following is used to quantitatively measure the criticality of a vulnerability?
In an effort to reduce costs, a company is implementing a strategy that gives employees access to internal company resources, including email, from personal devices. Which of the following strategies is the company implementing?
Which of the following incident response activities ensures evidence is properly handied?
Which of the following can best protect against an employee inadvertently installing malware on a company system?
An administrator discovers a cross-site scripting vulnerability on a company website. Which of the following will most likely remediate the issue?
Which of the following should be used to ensure that a new software release has not been modified before reaching the user?
An administrator discovers that some files on a database server were recently encrypted. The administrator sees from the security logs that the data was last accessed by a domain user. Which of the following best describes the type of attack that occurred?
A company must ensure sensitive data at rest is rendered unreadable. Which of the following will the company most likely use?
A security analyst identifies an incident in the network. Which of the following incident response activities would the security analyst perform next?
Which of the following architecture models ensures that critical systems are physically isolated from the network to prevent access from users with remote access privileges?
Which of the following is an example of implementing Zero Trust architecture?
A company identified the potential for malicious insiders to harm the organization. Which of the following measures should the organization implement to reduce this risk?
Which of the following is a vulnerability concern for end-of-life hardware?
An organization maintains intellectual property that it wants to protect. Which of the following concepts would be most beneficial to add to the company ' s security awareness training program?
 A screenshot of a computer AI-generated content may be incorrect.
A screenshot of a computer AI-generated content may be incorrect.