SY0-701 CompTIA Security+ Exam 2026 Free Practice Exam Questions (2026 Updated)
Prepare effectively for your CompTIA SY0-701 CompTIA Security+ Exam 2026 certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
An employee receives a text message from an unknown number claiming to be the company ' s Chief Executive Officer and asking the employee to purchase several gift cards. Which of the following types of attacks does this describe?
Which of the following is a common data removal option for companies that want to wipe sensitive data from hard drives in a repeatable manner but allow the hard drives to be reused?
Which of the following digital forensics activities would a security team perform when responding to legal requests in a pending investigation?
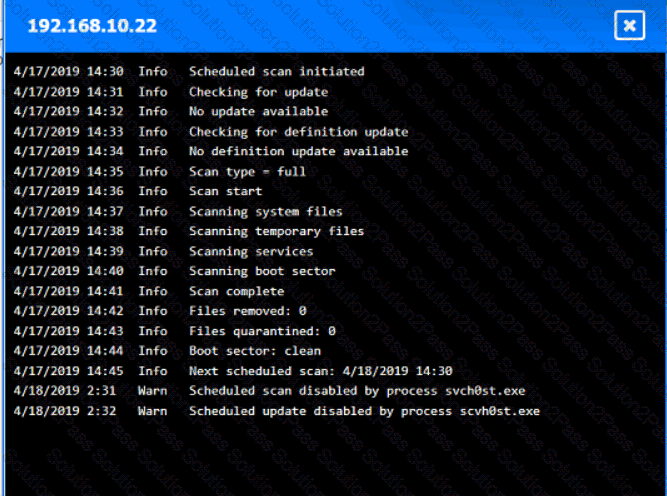
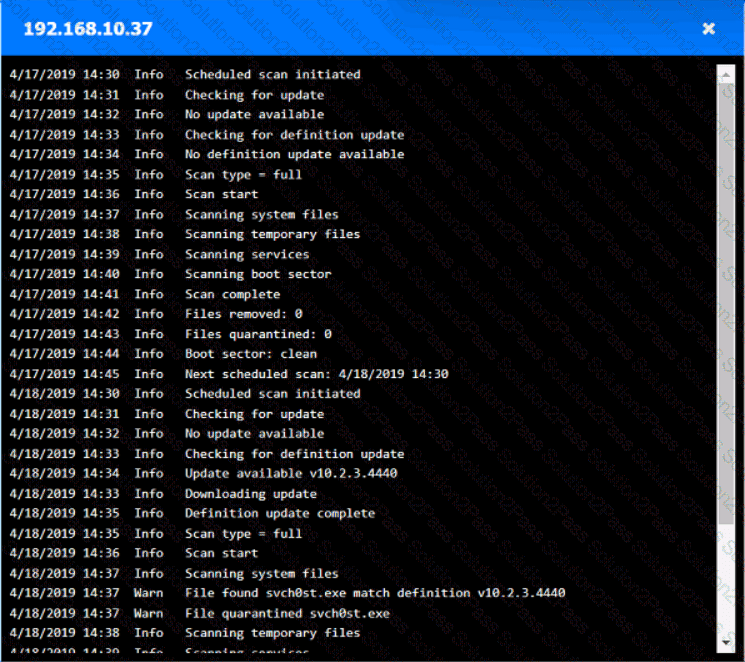
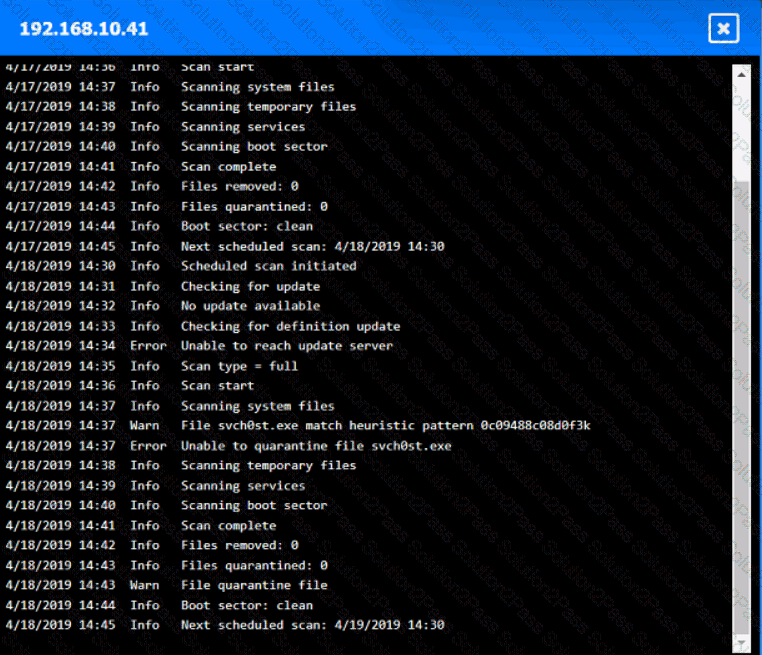
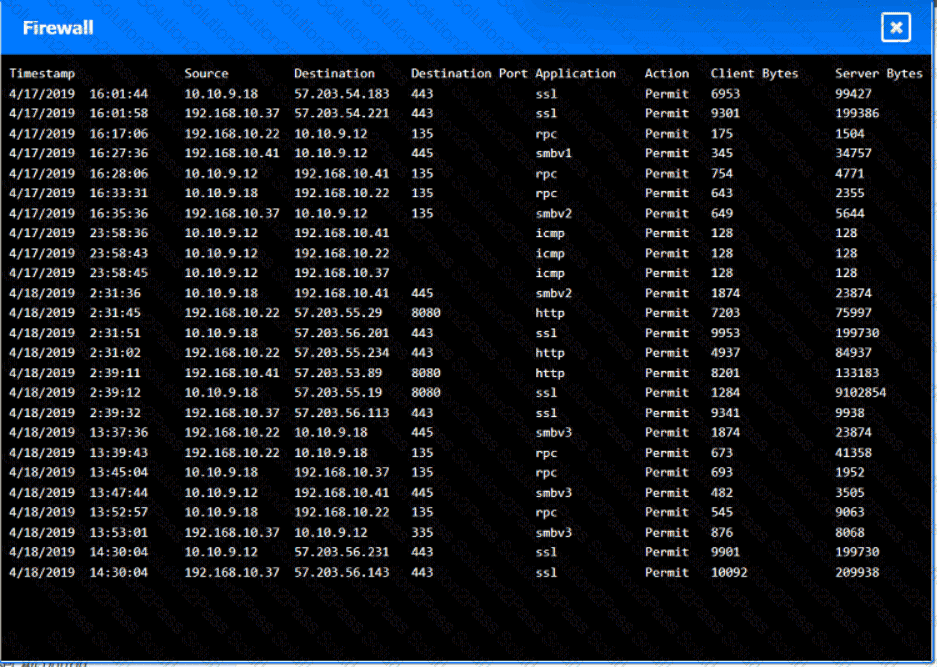
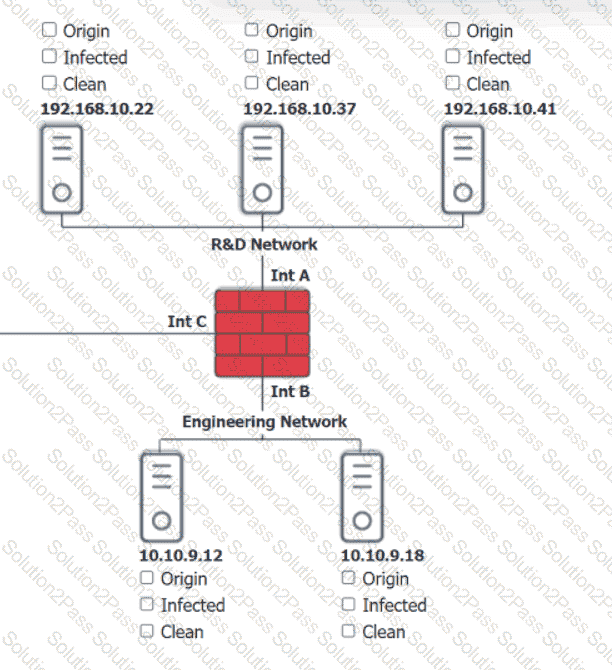
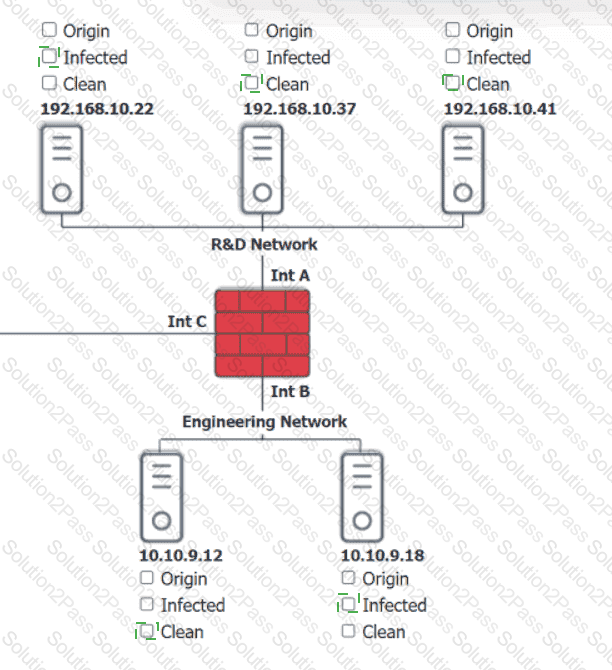
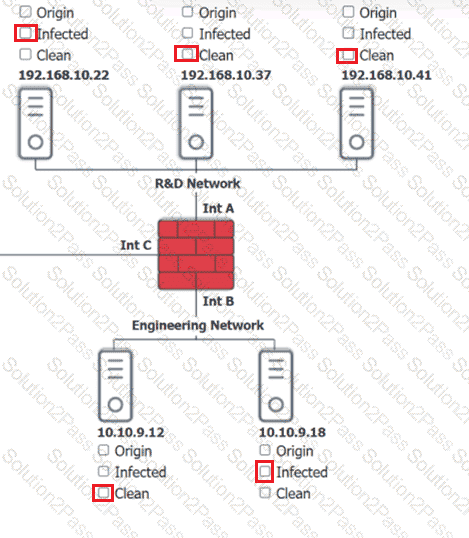
You are security administrator investigating a potential infection on a network.
Click on each host and firewall. Review all logs to determine which host originated the Infecton and then deny each remaining hosts clean or infected.
A security operations center determines that the malicious activity detected on a server is normal. Which of the following activities describes the act of ignoring detected activity in the future?
An administrator is estimating the cost associated with an attack that could result in the replacement of a physical server. Which of the following processes is the administrator performing?
A security team must help secure a company site after attackers defaced it. The site must be available to a wide range of countries over a secure protocol, but access from known malicious networks should be blocked. Which of the following will best secure the site?
A remote employee navigates to a shopping website on their company-owned computer. The employee clicks a link that contains a malicious file. Which of the following would prevent this file from downloading?
Company A jointly develops a product with Company B, which is located in a different country. Company A finds out that their intellectual property is being shared with unauthorized companies. Which of the following has been breached?
Which of the following describes a situation where a user is authorized before being authenticated?
An organization is developing a security program that conveys the responsibilities associated with the general operation of systems and software within the organization. Which of the following documents would most likely communicate these expectations?
Employees are missing features on company-provided tablets, affecting productivity. Management demands resolution in 48 hours. Which is the best solution?
Employees located off-site must have access to company resources in order to complete their assigned tasks These employees utilize a solution that allows remote access without interception concerns. Which of the following best describes this solution?
An analyst identifies that multiple users have the same passwords, but the hashes appear to be completely different. Which of the following most likely explains this issue?
A systems administrator is working on a solution with the following requirements:
• Provide a secure zone.
• Enforce a company-wide access control policy.
• Reduce the scope of threats.
Which of the following is the systems administrator setting up?
Which of the following threat actors would most likely target an organization by using a logic bomb within an internally-developed application?
A company is considering an expansion of access controls for an application that contractors and internal employees use to reduce costs. Which of the following risk elements should the implementation team understand before granting access to the application?
Which of the following is a use of CVSS?
An analyst is evaluating the implementation of Zero Trust principles within the data plane. Which of the following would be most relevant for the analyst to evaluate?
A security analyst receives alerts about an internal system sending a large amount of unusual DNS queries to systems on the internet over short periods of time during non-business hours. Which of the following is most likely occurring?
Which of the following strategies most effectively protects sensitive data at rest in a database?
A systems administrator is concerned users are accessing emails through a duplicate site that is not run by the company. Which of the following is used in this scenario?
Which of the following is a hardware-specific vulnerability?
An analyst wants to move data from production to the UAT server to test the latest release. Which of the following strategies should the analyst use to protect sensitive data from being viewed by the testing team?
An external vendor recently visited a company ' s headquarters tor a presentation. Following the visit a member of the hosting team found a file that the external vendor left behind on a server. The file contained detailed architecture information and code snippets. Which of the following data types best describes this file?
Which of the following teams combines both offensive and defensive testing techniques to protect an organization ' s critical systems?
A new employee can select a particular make and model of an employee workstation from a preapproved list. Which of the following is this an example of?
A business needs a recovery site but does not require immediate failover. The business also wants to reduce the workload required to recover from an outage. Which of the following recovery sites is the best option?
Which of the following describes the reason root cause analysis should be conducted as part of incident response?
Which of the following control types is AUP an example of?
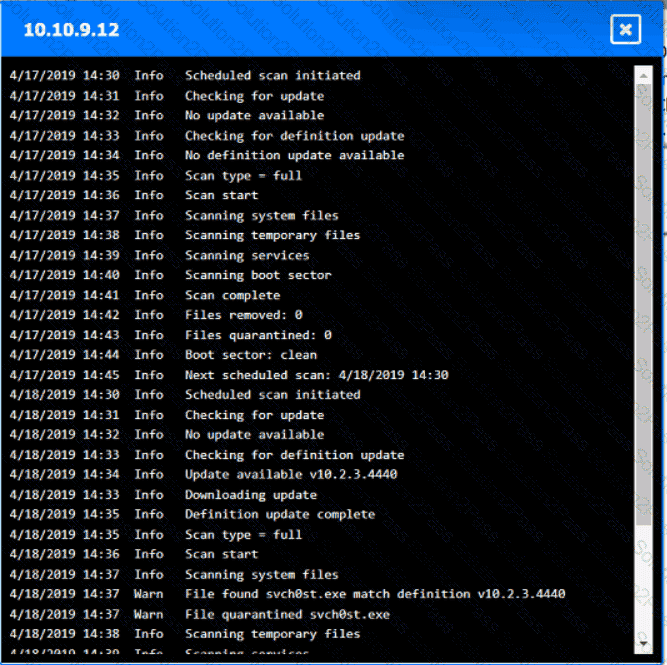
 A screenshot of a computer AI-generated content may be incorrect.
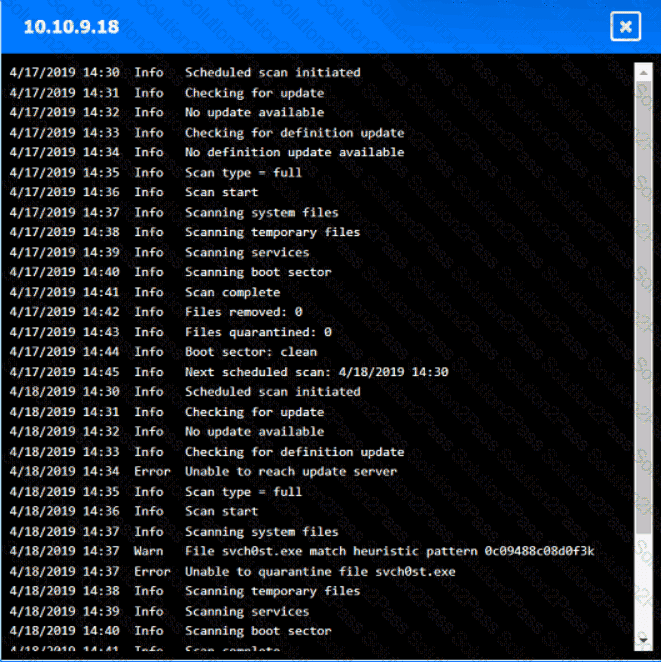
A screenshot of a computer AI-generated content may be incorrect.