XK0-005 CompTIA Linux+ Exam Free Practice Exam Questions (2026 Updated)
Prepare effectively for your CompTIA XK0-005 CompTIA Linux+ Exam certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
A non-privileged user is attempting to use commands that require elevated account permissions, but the commands are not successful. Which of the following most likely needs to be updated?
An administrator added a new disk to expand the current storage. Which of the following commands should the administrator run first to add the new disk to the LVM?
A Linux administrator is attempting to capture all network traffic coming to the server from the 10.0.6.5 IP address. Which of the following commands should the administrator run on the server to achieve the goal?
Users report issues when trying to securely connect to a web server. The systems administrator receives the following outputs:
bash
firewall-cmd --list-all
(Only ports for ssh, cockpit, dhcp-client are listed.)
netstat -an | grep LISTEN
tcp 0 0 0.0.0.0:443 ... LISTEN
Which of the following actions will fix this issue?
A systems administrator identifies multiple processes in a zombie state. Which of the following signals would be best for the administrator to send to the PPID?
An administrator thinks that the user Joe may be running an unauthorized process on a Linux server. Which of the following commands should the administrator run to confirm this idea?
A Linux administrator is tasked with moving files in a database server. The administrator must not overwrite any existing files. Which of the following commands would indicate that the file already exists?
A new database is installed on a server. To comply with the database vendor requirement, the huge page function should be set permanently. Which of the following commands will set this parameter?
A Linux administrator needs to forward port 8000 on a remote server to port 8000 on a local server. Which of the following commands should the administrator run on the local server to achieve this goal?
Which of the following command sequences is used to install Linux software directly from source code?
A systems administrator wants to list all local account names and their respective UIDs. Which of the following commands will provide output containing this information?
An application developer received a file with the following content:
##This is a sample Image ##
FROM ubuntu:18.04
MAINTAINER demohut@gtmail.com.hac
COPY . /app
RUN make /app
CMD python /app/app.py
RUN apt-get update
RUN apt-get install -y nginx
CMD ["echo","Image created"]
The developer must use this information to create a test bed environment and identify the image (myimage) as the first version for testing a new
application before moving it to production. Which of the following commands will accomplish this task?
A Linux administrator created a virtual clone of a physical server and would like to remove any existing entries related to SSH keys from outside entities on the virtual clone. Which of the following files should the administrator remove? (Select two).
A systems administrator receives reports that several virtual machines in a host are responding slower than expected. Upon further investigation, the administrator obtains the following output from one of the affected systems:
Which of the following best explains the reported issue?
Which of the following should be used to verify the integrity of a file?
A Linux engineer wants to give read-write-execute permissions for the cloud_users directory to user Oliver. Which of the following commands should the engineer use?
The application team is having issues accessing their data in their /app filesystem. Given the following outputs:
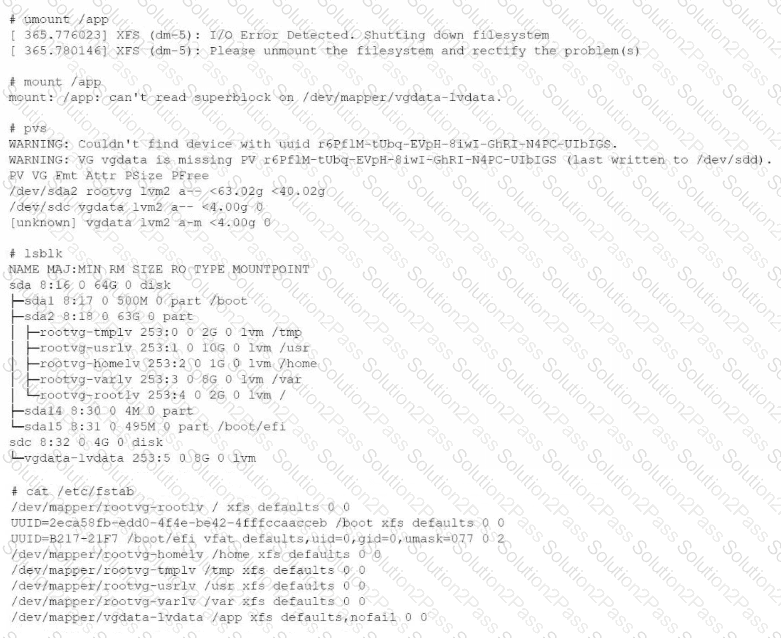
Which of the following is the reason for this issue?
A technician wants to temporarily use a Linux virtual machine as a router for the network segment 10.10.204.0/24. Which of the following commands should the technician issue? (Select three).
A Linux administrator was informed that the server time zone is incorrect. Which of the following commands should the administrator use to correct the time zone?
Joe, a user, is unable to log in to the system. The Linux administrator checks the /etc/passwd file and reviews the following output:
Joe:x:1002:1002::/home/Joe:/sbin/nologin
Which of the following should the administrator do to fix this issue?
