312-39 ECCouncil Certified SOC Analyst (CSA v2) Free Practice Exam Questions (2026 Updated)
Prepare effectively for your ECCouncil 312-39 Certified SOC Analyst (CSA v2) certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
SecureTech Inc. operates critical infrastructure and applications in AWS. The SOC detects suspicious activities such as unexpected API calls, unusual outbound traffic from instances, and DNS requests to potentially malicious domains. They need a fully managed AWS security service that continuously monitors for malicious activity, analyzes CloudTrail logs, VPC Flow Logs, and DNS query logs, leverages machine learning and threat intelligence, and provides actionable findings. Which AWS service best fits?
Which of the following technique protects from flooding attacks originated from the valid prefixes (IP addresses) so that they can be traced to its true source?
Which of the following is a set of standard guidelines for ongoing development, enhancement, storage, dissemination and implementation of security standards for account data protection?
Jannet works in a multinational corporation that operates multiple data centers, cloud environments, and on-premises systems. As a SOC analyst, she notices that security incidents are taking too long to detect and investigate. After analyzing this, she discovers that logs from firewalls, endpoint security solutions, authentication servers, and cloud applications are scattered across different systems in various formats. Her team has to manually convert logs into a readable format before investigating incidents. What approach should she implement to accept logs from heterogeneous sources with different formats, convert them into a common format, and improve incident detection and response time?
A security team is designing SIEM use-case logic to detect privilege escalation attempts on Windows servers. They have already identified and validated the necessary event sources (e.g., Active Directory logs, Windows Security logs). What should be their next step in the use case logic development process?
Which of the following event detection techniques uses User and Entity Behavior Analytics (UEBA)?
An organization is implementing and deploying the SIEM with following capabilities.
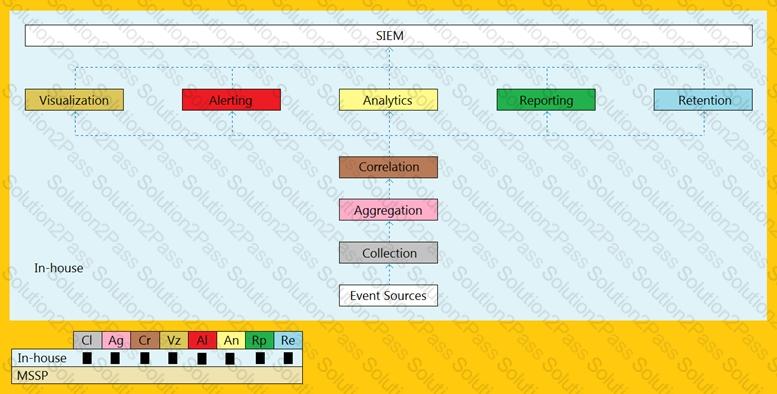
What kind of SIEM deployment architecture the organization is planning to implement?
Bonney's system has been compromised by a gruesome malware.
What is the primary step that is advisable to Bonney in order to contain the malware incident fromspreading?
The Security Operations Center (SOC) team at Rapid Response Group, a leading cybersecurity firm, is facing challenges in managing security incidents efficiently. With an increasing volume of alerts and security events being generated daily in their Microsoft Sentinel environment, the team is struggling to respond to threats quickly and consistently. To enhance their incident response capabilities, they aim to automate routine security tasks, such as log collection, alert triaging, remediation steps, and notifications to stakeholders. By implementing automated workflows, they seek to reduce response times, eliminate manual intervention for repetitive actions, and ensure a standardized approach to handling security threats across the organization. Which component of Microsoft Sentinel should they utilize to create these automated workflows for incident response?
Jennifer, a SOC analyst, initiates an investigation after receiving an alert about potential unauthorized activity on Marcus's workstation. She starts by retrieving EDR logs from the endpoint, analyzing network traffic patterns in the Security Information and Event Management (SIEM) system, and inspecting email gateway logs for signs of malicious attachments. Her objective is to determine whether this alert represents a legitimate security incident. In which phase of the Incident Response process is Jennifer currently operating?
The threat intelligence, which will help you, understand adversary intent and make informed decision to ensure appropriate security in alignment with risk.
What kind of threat intelligence described above?
At GlobalTech, the SOC team detects a suspicious ransomware outbreak affecting multiple endpoints. After successfully isolating the infected systems from the network, the Digital Forensics team begins their investigation. They deploy a forensics workstation to acquire RAM dumps, extract Windows Event Logs, and collect network PCAP files from the compromised hosts. Which phase of the Incident Response lifecycle is currently underway?
Which of the following threat intelligence is used by a SIEM for supplying the analysts with context and "situational awareness" by using threat actor TTPs, malwarecampaigns, tools used by threat actors.
1.Strategic threat intelligence
2.Tactical threat intelligence
3.Operational threat intelligence
4.Technical threat intelligence
John, SOC analyst wants to monitor the attempt of process creation activities from any of their Windows endpoints.
Which of following Splunk query will help him to fetch related logs associated with process creation?
The SOC team found a suspicious document file on a user's workstation. Upon initial inspection, the document appears benign, but deeper analysis reveals an embedded PowerShell script. The team suspects the script is designed to download and execute a malicious payload. They need to understand the script's functionality without triggering it. Which malware analysis technique is recommended to understand the PowerShell script's functionality without executing it?
Which of the following is a report writing tool that will help incident handlers to generate efficientreports on detected incidents during incident response process?
The team receives an alert about a ransomware incident affecting the organization’s email infrastructure. Forensic analysis identifies the ransomware exploited CVE-2024-0123 in an unpatched mail server. The incident response team is deploying an emergency patch (KB5025941), updating mail filtering rules to block malicious payloads, and implementing additional network segmentation to limit lateral movement. Which phase of the Incident Response process is the SOC currently executing?
Wesley is an incident handler in a company named Maddison Tech. One day, he was learning techniques for eradicating the insecure deserialization attacks.
What among the following should Wesley avoid from considering?
You are a SOC analyst at a leading financial institution tasked with developing a comprehensive threat model to safeguard critical assets: sensitive customer data, online banking applications, and real-time payment processing systems. The organization has observed increased targeted attacks on financial entities, including credential theft, account takeovers, and sophisticated phishing. Senior management is concerned about long-term financial and reputational damage. You need intelligence providing insights into high-level risks, geopolitical threats, and emerging cybercriminal strategies with long-term implications for security posture. Which type of threat intelligence are you seeking?
Sarah, a financial analyst at a multinational corporation, is suspected of leaking sensitive financial data to an unauthorized external party. The SOC team observed anomalous data transfer patterns originating from her account, flagged by the SIEM, indicating potential data exfiltration. The incident response team must contain the incident swiftly to minimize data loss and protect critical assets. As a SOC analyst, which should be prioritized as the initial containment measure?
