FCSS_NST_SE-7.6 Fortinet NSE 6 - Network Security 7.6 Support Engineer Free Practice Exam Questions (2026 Updated)
Prepare effectively for your Fortinet FCSS_NST_SE-7.6 Fortinet NSE 6 - Network Security 7.6 Support Engineer certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
Consider the scenario where the server name indication (SNI) does not match either the common name (CN) or any of the subject alternative names (SAN) in the server certificate. Which two actions will FortiGate take when using the default settings for SSL certificate inspection? (Choose two answers)
Which Iwo actions does FortiGate take after an administrator enables the auxiliary session selling? (Choose two.)
Exhibit.
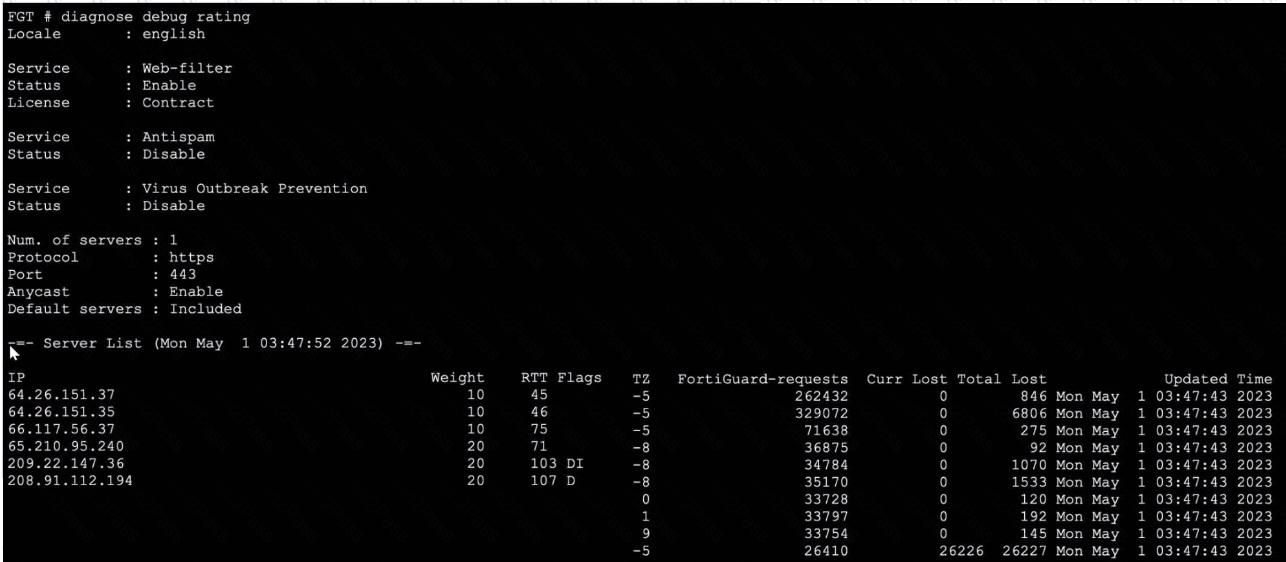
Refer to the exhibit, which shows the output of a diagnose command.
What can you conclude about the debug output in this scenario?
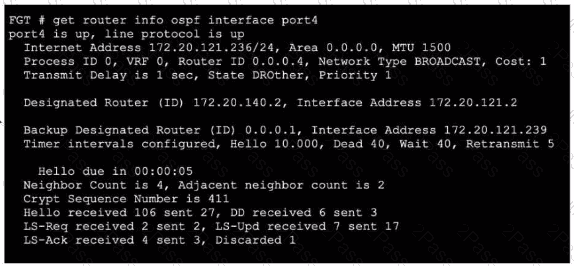
Refer to the exhibit, which shows the output of get router info ospf neighbor.
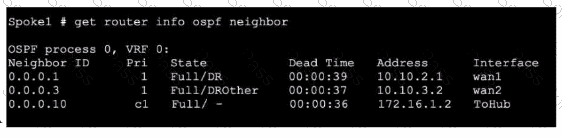
What can you conclude from the command output?
Exhibit.
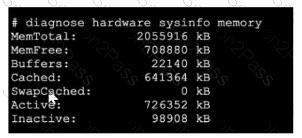
Refer to the exhibit, which shows a partial output of diagnose hardware aysinfo memory.
Which two statements about the output are true? (Choose two.)
Refer to the exhibit, which shows the partial output of a diagnose command.
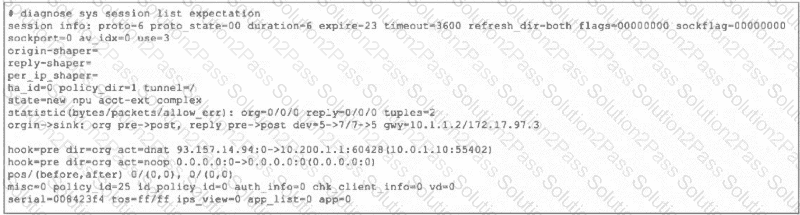
Which two conclusions can you draw from the output shown in the exhibit? (Choose two.)
Refer to the exhibit.
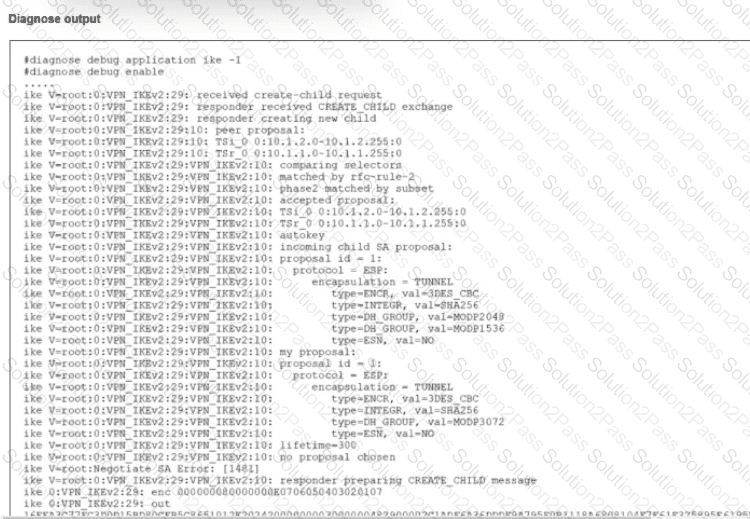
An IPsec VPN tunnel using IKEv2 was brought up successfully, but when the tunnel rekey takes place the tunnel goes down.
The debug command for IKE was enabled and, in the exhibit, you can review the partial output of the debug IKE while attempting to bring the tunnel up.
What is causing. The tunnel to be down?
Refer to the exhibit.
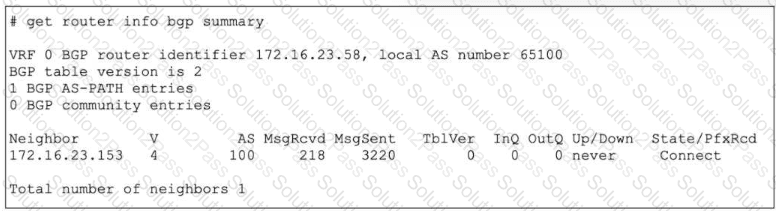
The output of a BGP debug command is shown.
Why has the local router at 172.16.23.58 been unable to establish adjacency with its only neighbor?
Consider the scenario where the server name indication (SNI) does not match either the common name (CN) or any of the subject alternative names (SAN) in the server certificate.
Which action will FortiGate take when using the default settings for SSL certificate inspection?
Which Iwo troubleshooting steps should you perform lf you encounter issues with intermittent web filter behavior? (Choose two.)
Refer to the exhibit, which shows a truncated output of a real-time RADIUS debug.
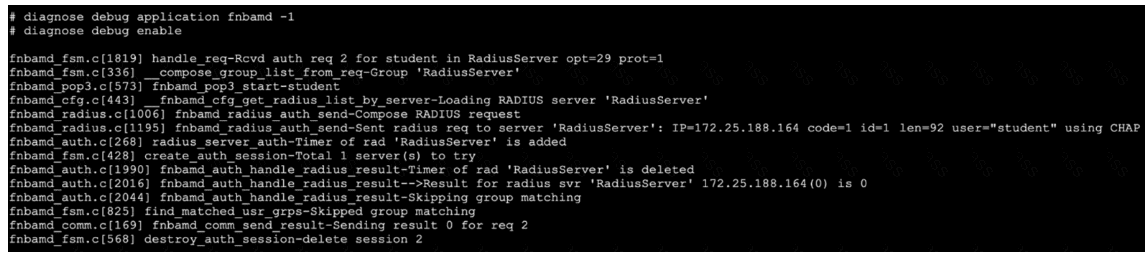
Which two statements are true? (Choose two answers)
Refer to the exhibit.
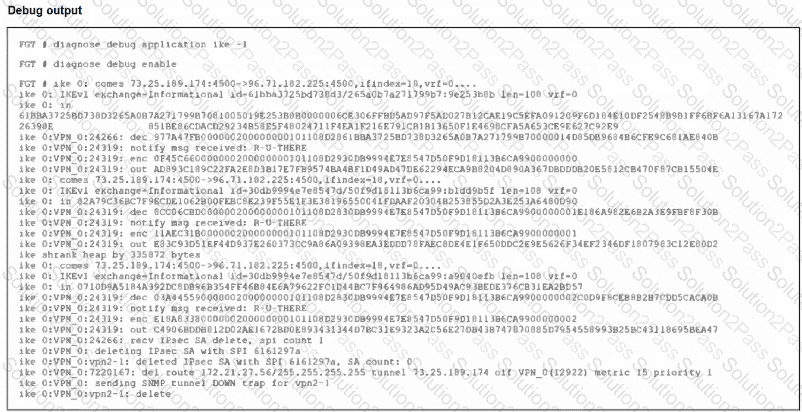
An IPsec VPN tunnel is dropping, as shown by the debug output.
Analyzing the debug output, what could be causing the tunnel to go down?
Refer to the exhibit, which shows the output of a debug command.
Which two statements about the output are true? (Choose two.)
Refer to the exhibit, which contains partial output from an IKE real-time debug.
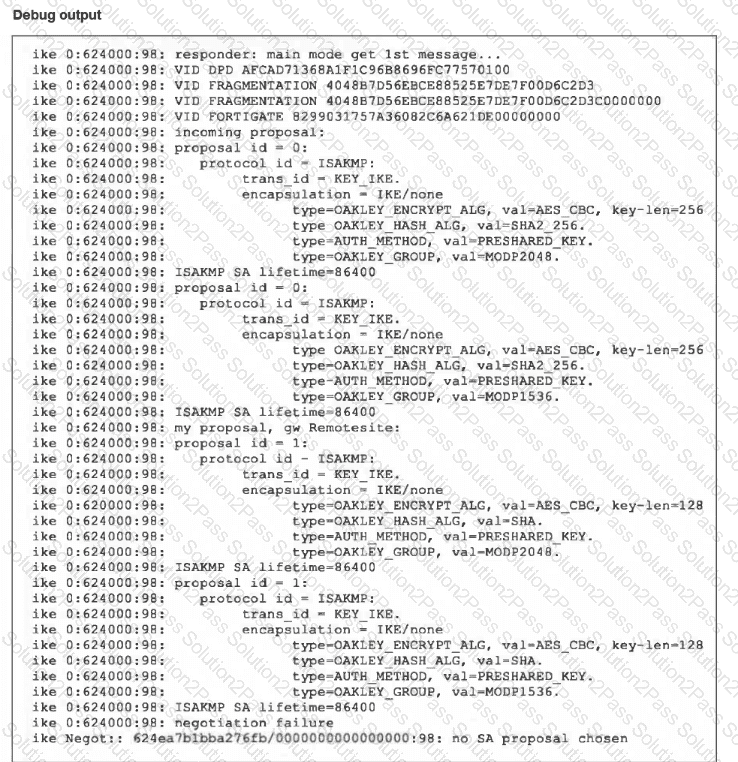
The administrator does not have access to the remote gateway.
Based on the debug output, which configuration change the administrator make to the local gateway to resolve the phase 1 negotiation error?
Refer to the exhibit.
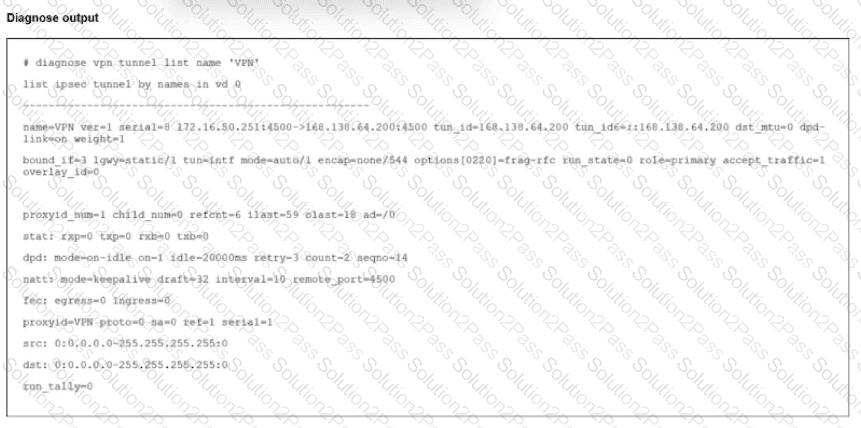
The output of the command diagnose vpn tunnels liar is shown.
Which two statements accurately describe the status of the tunnel? (Choose two.)
Exhibit 1.
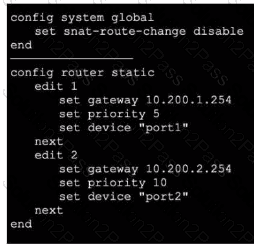
Exhibit 2.
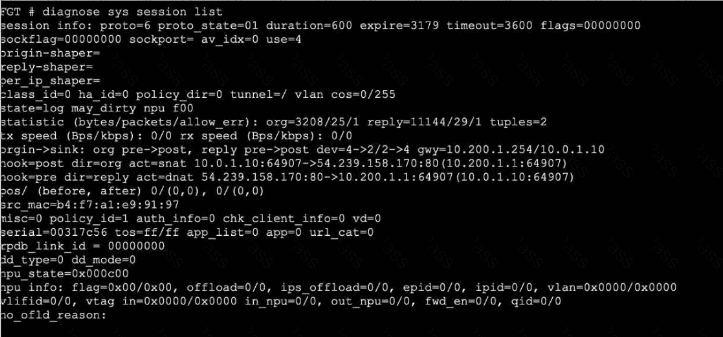
Refer to the exhibits, which show the configuration on FortiGate and partial internet session information from a user on the internal network.
An administrator would like to lest session failover between the two service provider connections.
Which two changes must the administrator make to force this existing session to immediately start using the other interface? (Choose two.)
Refer to the exhibit.
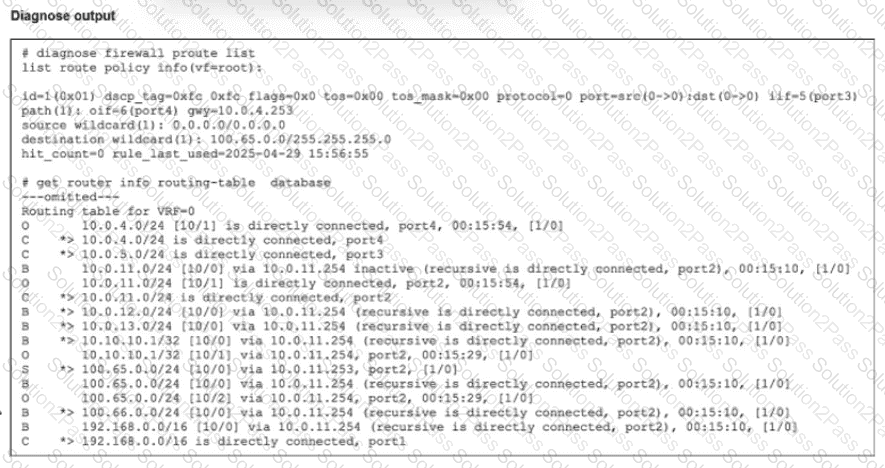
Which route will traffic take to get to the 100.65.0.0/24 network considering the routes are all configured with the same distance?
Refer to the exhibit.
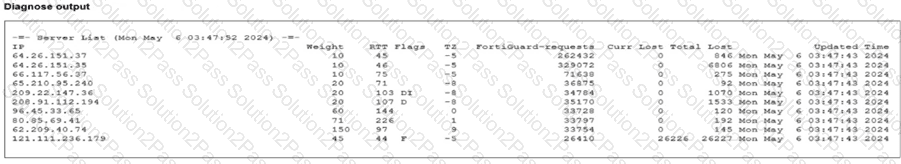
Partial output of command diagnose debug rating is shown. Which FDS server will the FortiGate algorithm choose?
Which two statements about Security Fabric communications are true? (Choose two.)
