HPE7-A02 HP Aruba Certified Network Security Professional Exam Free Practice Exam Questions (2026 Updated)
Prepare effectively for your HP HPE7-A02 Aruba Certified Network Security Professional Exam certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
You have installed an HPE Aruba Networking Network Analytic Engine (NAE) script on an AOS-CX switch to monitor a particular function.
Which additional step must you complete to start the monitoring?
An AOS-CX switch has been configured to implement UBT to a cluster of three HPE Aruba Networking gateways.
How does the switch determine to which gateways to tunnel UBT users ' traffic?
A company has HPE Aruba Networking gateways that implement gateway IDS/IPS. Admins sometimes check the Security Dashboard, but they want a faster way to discover if a gateway starts detecting threats in traffic.
What should they do?
You have created this rule in an HPE Aruba Networking ClearPass Policy Manager (CPPM) service’s enforcement policy:
IF Authorization [Endpoints Repository] Conflict EQUALS true
THEN apply " quarantine_profile "
What information can help you determine whether you need to configure cluster-wide profiler parameters to ignore some conflicts?
A security team needs to track a device ' s communication patterns and identify patterns such as how many destinations the device is accessing.
Which Aruba solution can show this information at a glance?
A company has HPE Aruba Networking APs running AOS-10 and managed by HPE Aruba Networking Central. The company also has AOS-CX switches. The
security team wants you to capture traffic from a particular wireless client. You should capture this client ' s traffic over a 15 minute time period and then send the
traffic to them in a PCAP file.
What should you do?
What is a benefit of Online Certificate Status Protocol (OCSP)?
A company has HPE Aruba Networking APs running AOS-10 that connect to AOS-CX switches. The APs will:
Authenticate as 802.1X supplicants to HPE Aruba Networking ClearPass Policy Manager (CPPM)
Be assigned to the " APs " role on the switches
Have their traffic forwarded locally
What information do you need to help you determine the VLAN settings for the " APs " role?
A company uses HPE Aruba Networking APs running AOS-10, HPE Aruba Networking Central, and HPE Aruba Networking ClearPass Policy Manager (CPPM). After starting to implement TEAP to authenticate wireless clients, admins notice that all clients are showing up on APs and in HPE Aruba Networking Central with the “anonymous” username. They want to see users’ actual names there.
What can they do to address this issue?
HPE Aruba Networking ClearPass Policy Manager (CPPM) uses a service to authenticate clients. You are now adding the Endpoints Repository as an
authorization source for the service, and you want to add rules to the service ' s policies that apply different access levels based, in part, on a client ' s device
category. You need to ensure that CPPM can apply the new correct access level after discovering new clients ' categories.
What should you enable on the service?
A company has several use cases for using its AOS-CX switches ' HPE Aruba Networking Network Analytics Engine (NAE).
What is one guideline to keep in mind as you plan?
A company is implementing HPE Aruba Networking Wireless IDS/IPS (WIDS/WIPS) on its AOS-10 APs, which are managed in HPE Aruba Networking Central.
What is one requirement for enabling detection of rogue APs?
A company has AOS-CX switches and HPE Aruba Networking ClearPass Policy Manager (CPPM). The company wants switches to implement 802.1X authentication to CPPM and download user roles. What is one task that you must complete on CPPM to support this use case?
HPE Aruba Networking Central displays a Gateway Threat Count alert in the alert list. How can you gather more information about what caused the alert to trigger?
You need to set up an HPE Aruba Networking VIA solution for a customer who needs to support 2100 remote employees. The customer wants employees to
download their VIA connection profile from the VPNC. Only employees who authenticate with their domain credentials to HPE Aruba Networking ClearPass Policy
Manager (CPPM) should be able to download the profile. (A RADIUS server group for CPPM is already set up on the VPNC.)
How do you configure the VPNC to enforce that requirement?
What can help justify the extra cost of air monitors (AMs) to a company?
You are configuring the HPE Aruba Networking ClearPass Device Insight Integration settings on ClearPass Policy Manager (CPPM). For which use case should you set the ' Tag Updates Action " to " apply for all tag updates " ?
A company has HPE Aruba Networking APs (AOS-10), which authenticate clients to HPE Aruba Networking ClearPass Policy Manager (CPPM). CPPM is set up
to receive a variety of information about clients ' profile and posture. New information can mean that CPPM should change a client ' s enforcement profile.
What should you set up on the APs to help the solution function correctly?
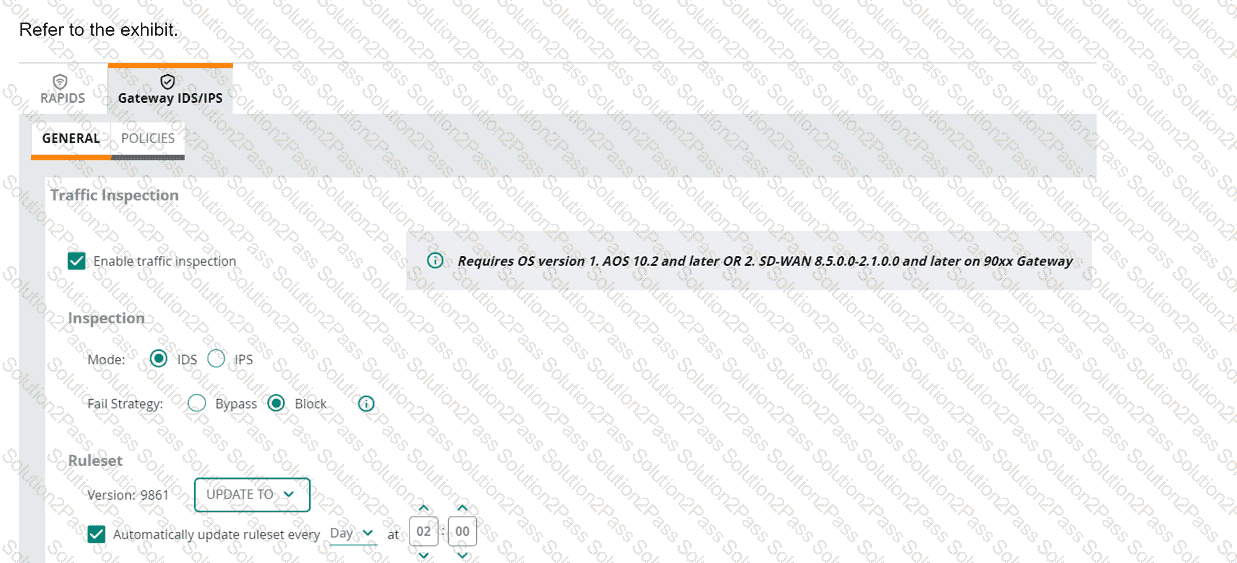
(Note that the HPE Aruba Networking Central interface shown here might look slightly different from what you see in your HPE Aruba Networking Central
interface as versions change; however, similar concepts continue to apply.)
An HPE Aruba Networking 9x00 gateway is part of an HPE Aruba Networking Central group that has the settings shown in the exhibit. What would cause the
gateway to drop traffic as part of its IDPS settings?
You are setting up HPE Aruba Networking SSE. Which use case requires you to apply a non-default device posture in a rule?
